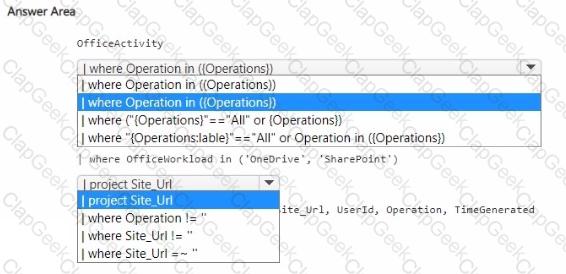
You have a Microsoft Sentinel workspace.
You plan to visualize data from Microsoft SharePoint Online and OneDrive sites.
You need to create a KQL query for the visual. The solution must meet the following requirements:
• Select all workloads as a single operation.
• Include two parameters named Operations and Users.
• In the results, exclude empty values for the site URLs.
How should you complete the query? To answer, select the appropriate options in the answer area. NOTE: Each correct selection is worth one point.
Note: This question is part of a series of questions that present the same scenario. Each question in the series contains a unique solution that might meet the stated goals. Some question sets might have more than one correct solution, while others might not have a correct solution.
After you answer a question in this section, you will NOT be able to return to it. As a result, these questions will not appear in the review screen.
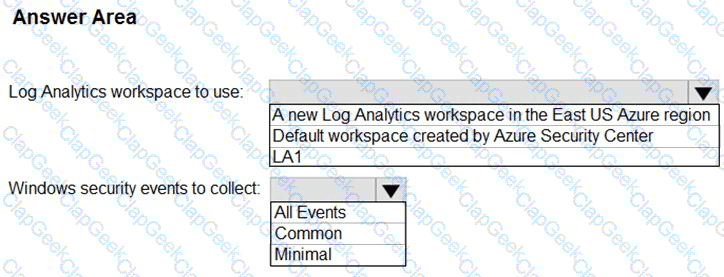
You have Linux virtual machines on Amazon Web Services (AWS).
You deploy Azure Defender and enable auto-provisioning.
You need to monitor the virtual machines by using Azure Defender.
Solution: You enable Azure Arc and onboard the virtual machines to Azure Arc.
Does this meet the goal?
You use Azure Sentinel.
You need to use a built-in role to provide a security analyst with the ability to edit the queries of custom Azure Sentinel workbooks. The solution must use the principle of least privilege.
Which role should you assign to the analyst?
A company uses Azure Sentinel.
You need to create an automated threat response.
What should you use?
You need to implement Microsoft Defender for Cloud to meet the Microsoft Defender for Cloud requirements and the business requirements. What should you include in the solution? To answer, select the appropriate options in the answer area. NOTE: Each correct selection is worth one point.
You are configurin g Microsoft Cloud App Security.
You have a custom threat detection policy based on the IP address ranges of your company’s United States-based offices.
You receive many alerts related to impossible travel and sign-ins from risky IP addresses.
You determine that 99% of the alerts are legitimate sign-ins from your corporate offices.
You need to prevent alerts for legitimate sign-ins from known locations.
Which two actions should you perform? Each correct answer presents part of the solution.
NOTE: Each correct selection is worth one point.
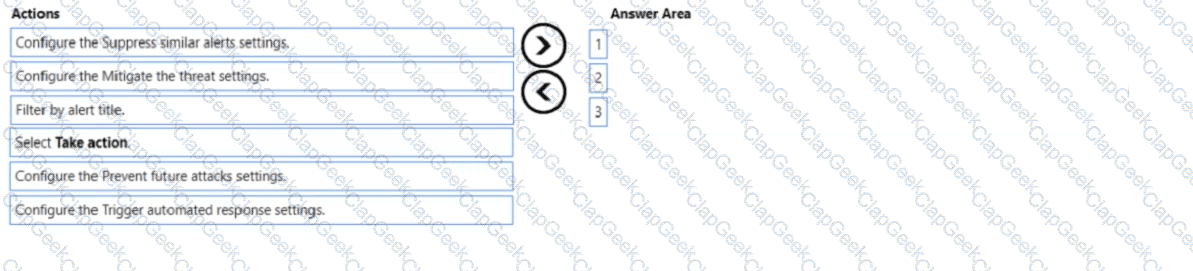
You use Azure Security Center.
You receive a security alert in Security Center.
You need to view recommendations to resolve the alert in Security Center.
What should you do?
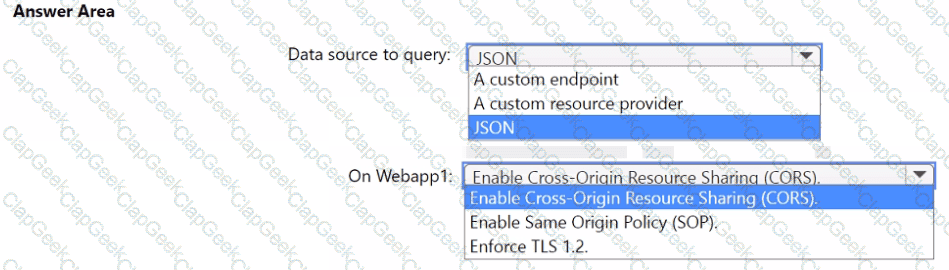
You need to implement the query for Workbook1 and Webapp1. The solution must meet the Microsoft Sentinel requirements. How should you configure the query? To answer, select the appropriate options in the answer area. NOTE: Each correct selection is worth one point.
You have a Microsoft 365 E5 subscription.
You have 1,000 Windows devices that have a third-party antivirus product installed and Microsoft Defender Antivirus in passive mode.
All Windows devices are on boarded to Microsoft Defender for Endpoint.
You need to ensure that the devices are protected from malicious artifacts that were undetected by the third-party antivirus product.
Solution: You enable Live Response.
Does this meet the goal?
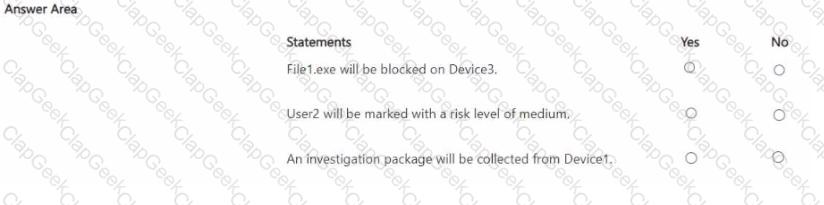
You have a Microsoft 365 subscription that contains three users named User1. User2 and User3 and the resources shown in the following table.
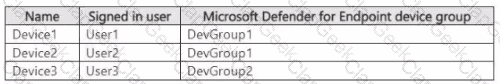
You have a Microsoft Defender XDR detection rule named Rule1 that has the following configurations:
• Scope: DevGroup1
• File hash: File1.exe
• Actions
o Devices: Collect investigation package
o User: Mark as compromised o Files: Block
Each user attempts to run File1.exe on their device.
For each of the following statements, select Yes if the statement is true. Otherwise, select No.
NOTE: Each correct selection is worth one point.
You have an Azure subscription named Sub1 that contains the resources shown in the following table.
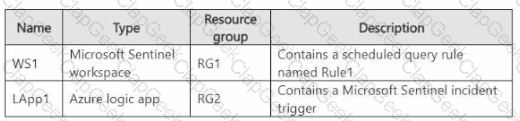
You plan to configure Rule1 to trigger Lapp1 when an incident is generated.
You need to recommend the role-based access control (RBAC) role that you should assign to WS1, and the scope at which should you assign the role. The solution must follow the principle of least privilege.
What should you recommend? To answer, select the appropriate options in the answer area.
NOTE: Each correct selection is worth one point.
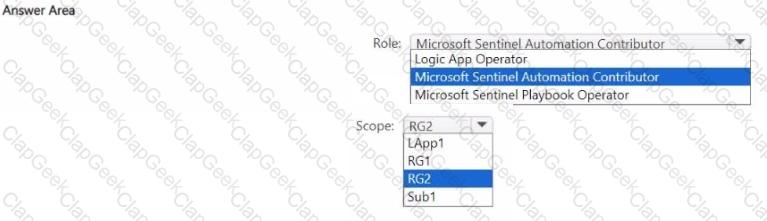
You need to build a KQL query in a Microsoft Sentinel workspace. The query must return the SecurityEvent record for accounts that have the last record with an EventID value of 4624. How should you complete the query ' To answer, select the appropriate options in the answer area.
NOTE: Each coned selection is worth one point
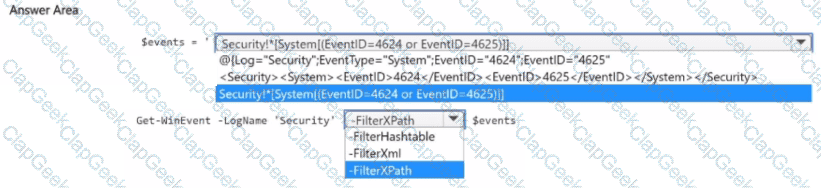
You have on-premises servers that run Windows Server.
You have a Microsoft Sentinel workspace named SW1. SW1 is configured to collect Windows Security log entries from the servers by using the Azure Monitor Agent data connector.
You plan to limit the scope of collected events to events 4624 and 462S only.
You need to use a PowerShell script to validate the syntax of the filter applied to the connector.
How should you complete the script? To answer, select the appropriate options in the answer area.
NOTE: Each correct selection is worth one point.
You have a Microsoft subscription that has Microsoft Defender for Cloud enabled You configure the Azure logic apps shown in the following table.
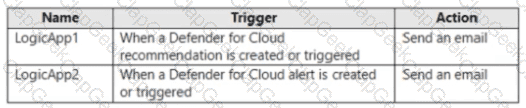
You need to configure an automatic action that will run if a Suspicious process executed alert is triggered. The solution must minimize administrative effort.
Which three actions should you perform in sequence? To answer, move the appropriate actions from the list of actions to the answer area and arrange them in the correct order.
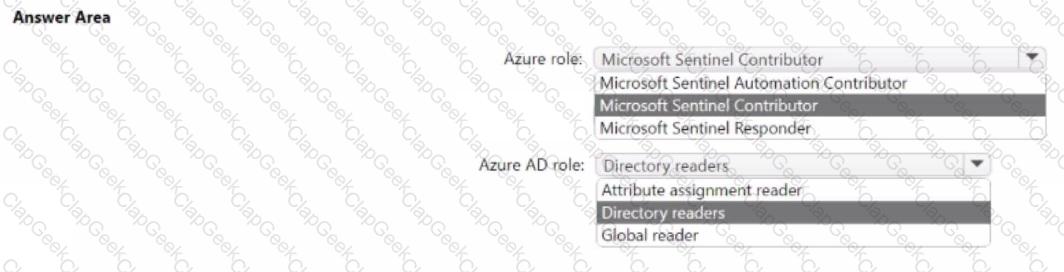
You have an Azure subscription that contains a guest user named User1 and a Microsoft Sentinel workspace named workspace1.
You need to ensure that User1 can triage Microsoft Sentinel incidents in workspace1. The solution must use the principle of least privilege.
Which roles should you assign to User1? To answer, select the appropriate options in the answer area.
NOTE: Each correct selection is worth one point.
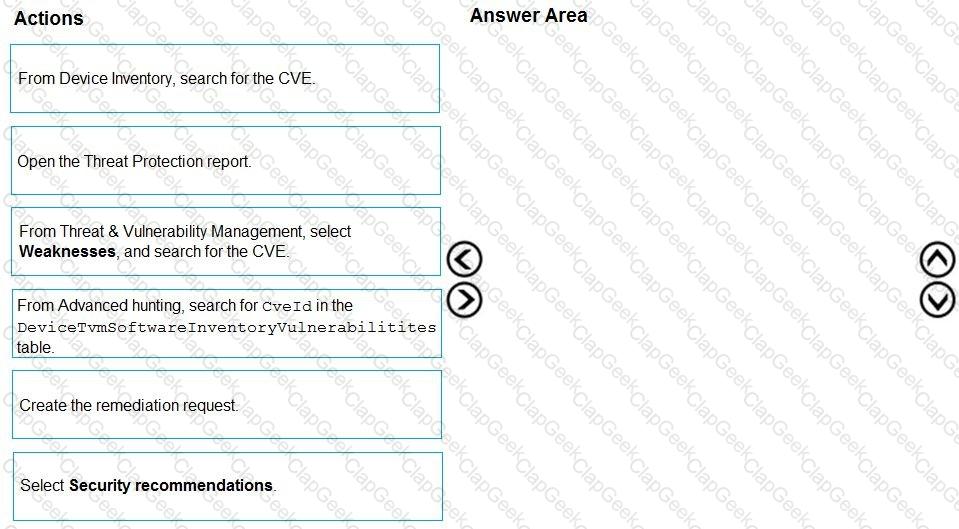
You are informed of a new common vulnerabilities and exposures (CVE) vulnerability that affects your environment.
You need to use Microsoft Defender Security Center to request remediation from the team responsible for the affected systems if there is a documente d active exploit available.
Which three actions should you perform in sequence? To answer, move the appropriate actions from the list of actions to the answer area and arrange them in the correct order.
You have a Microsoft 365 subscription that uses Microsoft Defender for Endpoint Plan Z and contains 1,000 Windows devices.
You have a PowerShell script named Script Vps1 that is signed digitally.
You need to ensure that you can run Script1.psl in a live response session on one of the devices.
What should you do first from the live response session?
You have a Microsoft 365 E5 subscription that contains 500 Windows 11 devices.
You have a Microsoft Defender for Endpoint deployment that has the following settings:
Discovery mode: Basic
Live Response: Disabled
Enable EDR in block mode: Off
Tamper Protection: Off
You need to implement automatic attack disruption in Microsoft Defender XDR.
What should you do?
You have a Microsoft Sentinel workspace.
You have a query named Query1 as shown in the following exhibit.
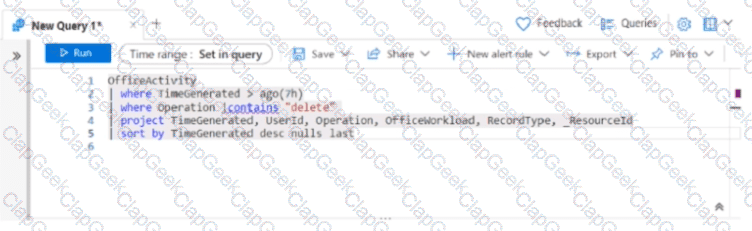
You plan to create a custom parser named Parser 1. You need to use Query1 in Parser1. What should you do first?
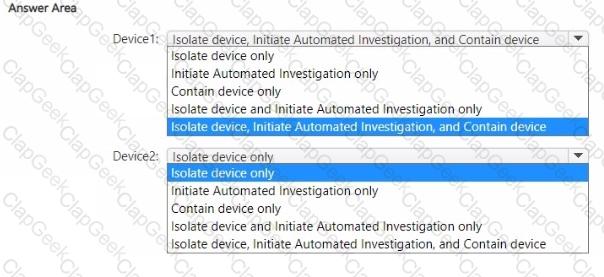
You have a Microsoft 365 E5 subscription that uses Microsoft Defender for Endpoint.
You have the on-premises devices shown in the following table.
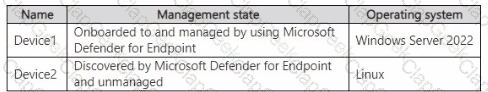
You are preparing an incident response plan for devices infected by malware. You need to recommend response actions that meet the following requirements:
• Block malware from communicating with and infecting managed devices.
• Do NOT affect the ability to control managed devices.
Which actions should you use for each device? To answer, select the appropriate options in the answer area. NOTE: Each correct selection is worth one point.
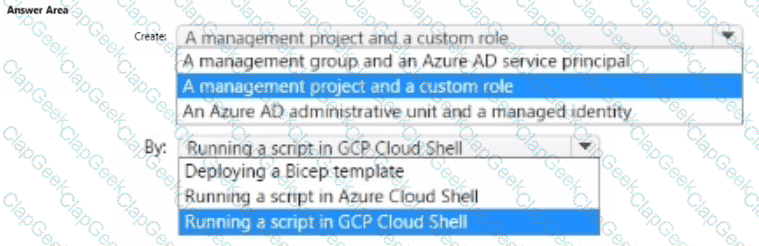
You have an Azure subscription that uses Microsoft Defender for Cloud.
You create a Google Cloud Platform (GCP) organization named GCP1.
You need to onboard GCP1 to Defender for Cloud by using the native cloud connector. The solution must ensure that all future GCP projects are onboarded automatically.
What should you include in the solution? To answer, select the appropriate options in the answer area.
NOTE: Each correct selection is worth one point.
You are responsible for responding to Azure Defender for Key Vault alerts.
During an investigation of an alert, you discover unauthorized atte mpts to access a key vault from a Tor exit node.
What should you configure to mitigate the threat?
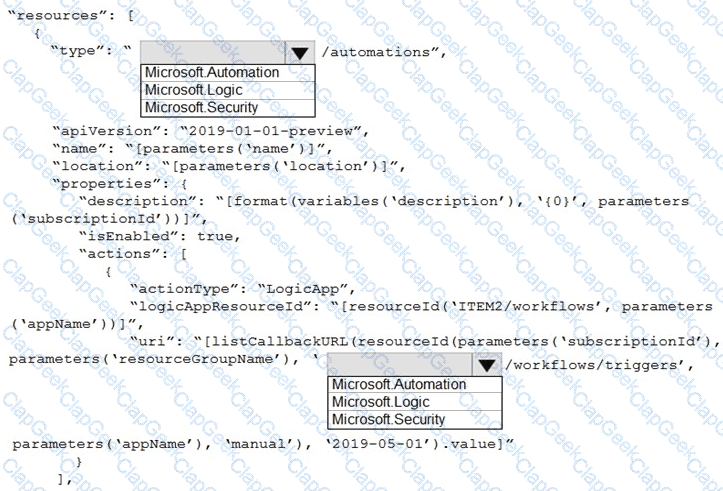
You need to use an Azure Resource Manager template to create a workflow automation that will trigger an automatic re mediation when specific security alerts are received by Azure Security Center.
How should you complete the portion of the template that will provision the required Azure resources? To answer, select the appropriate options in the answer area.
NOTE: Each correct selection is worth one point.
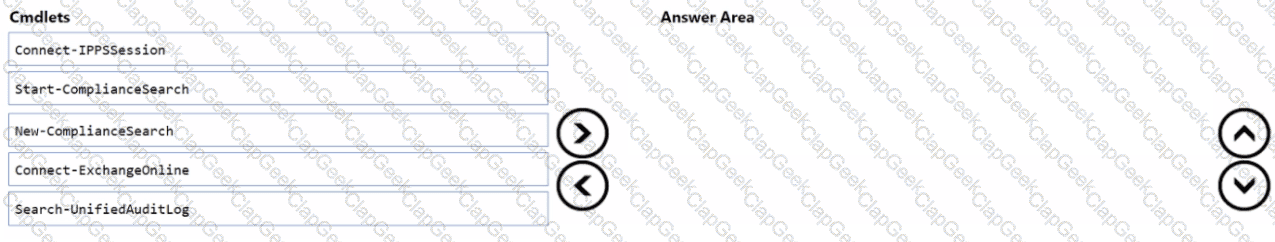
You have a Microsoft 365 E5 subscription that uses Microsoft Exchange Online.
You need to identify phishing email messages.
Which three cmdlets should you run in sequence? To answer, move the appropriate cmdlets from the list of cmdlets to the answer area and arrange them in the correct order.
Note: This question is part of a series of questions that present the same scenario. Each question in the series contains a unique solution that might meet the stated goals. Some question sets might have more than one correct solution, while others might not have a correct solution.
Aft er you answer a question in this section, you will NOT be able to return to it. As a result, these questions will not appear in the review screen.
You are configuring Microsoft Defender for Identity integration with Active Directory.
From the Microsoft D efender for identity portal, you need to configure several accounts for attackers to exploit.
Solution: You add the accounts to an Active Directory group and add the group as a Sensitive group.
Does this meet the goal?
You need to implement the Azure Information Protection requirements. What should you configure first?
You need to restrict cloud apps running on CUENT1 to meet the Microsoft Defender for Endpoint requirements. Which two configurations should you modify? Each correct answer presents part of the solution. NOTE: Each correct selection is worth one point.
You have a Microsoft 365 E5 subscription that uses Microsoft Exchange Online. You identify the suspicious emails shown in the following table.
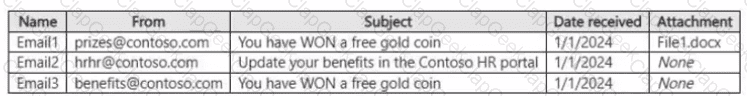
In the Microsoft Purview portal, you create the content searches shown in the following table.
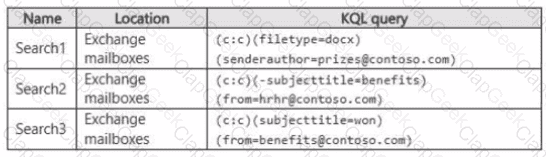
For each of the following statements, select Yes if the statement is true. Otherwise, select No. NOTE: Each correct selection is worth one point.
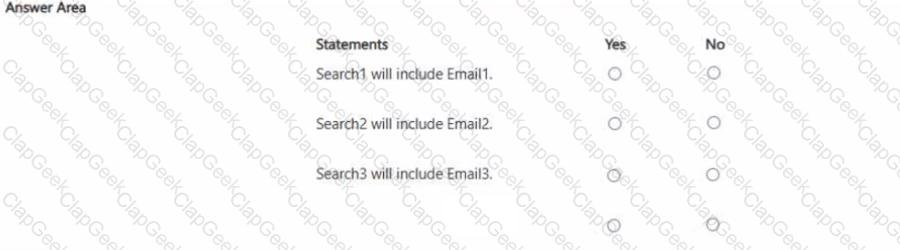
You need to recommend remediation actions for the Azure Defender alerts for Fabrikam.
What should you recommend for each threat? To answer, select the appropriate options in the answer area.
NOTE: Each correct selection is worth one point.
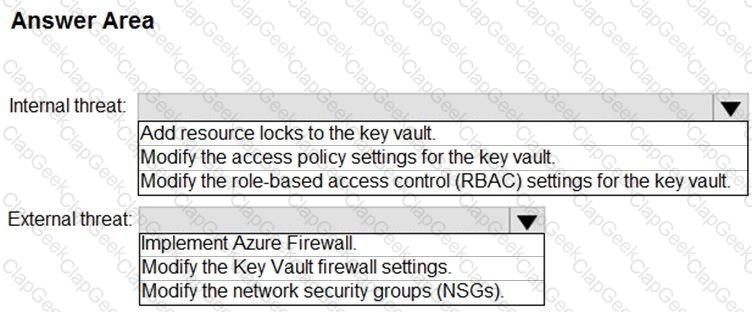
You need to create an advanced hunting query to i nvestigate the executive team issue.
How should you complete the query? To answer, select the appropriate options in the answer area.
NOTE: Each correct selection is worth one point.
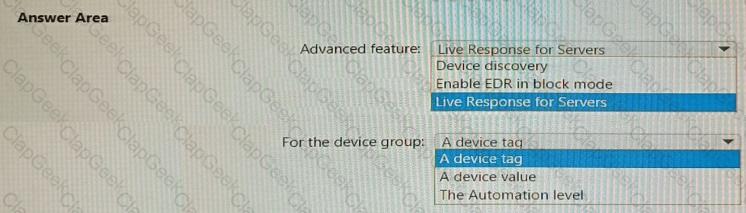
You have a Microsoft 365 E5 subscription that uses Microsoft 365 Defender for Endpoint.
You need to ensure that you can initiate remote shell connections to Windows servers by using the Microsoft 365 Defender portal.
What should you configure? To answer, select the appropriate options in the answer area.
NOTE: Each correct selection is worth one point.
Which rule setting should you configure to meet the Microsoft Sentinel requirements?
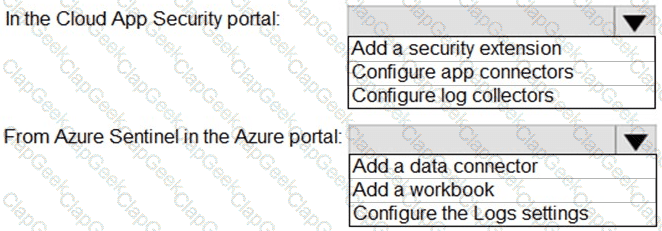
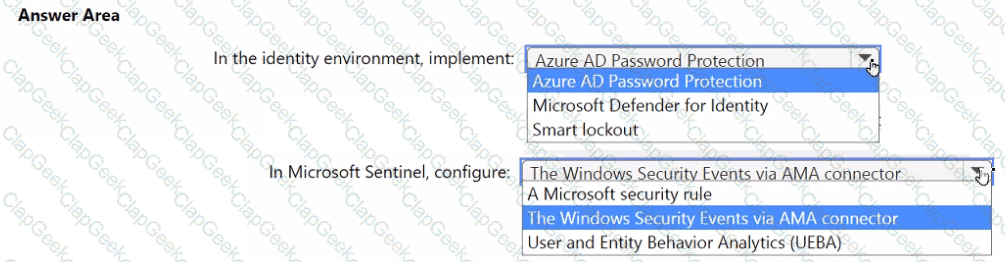
You need to configure the Microsoft Sentinel integration to meet the Microsoft Sentinel requirements. What should you do? To answer, select the appropriate options in the answer area. NOTE: Each correct selection is worth one point.
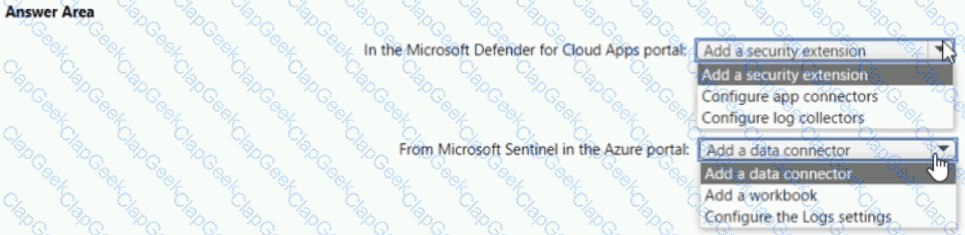
You need to configure the Azure Sentinel integration to meet the Azure Senti nel requirements.
What should you do? To answer, select the appropriate options in the answer area.
NOTE: Each correct selection is worth one point.
You need to complete the query for failed sign-ins to meet the technical requirements.
Where can you find the column name to complete the where clause?
You need to remediate ac tive attacks to meet the technical requirements.
What should you include in the solution?
You need to recommend a solution to meet the technical requirements for the Azure virtual machines. What should you include in the recommendation?
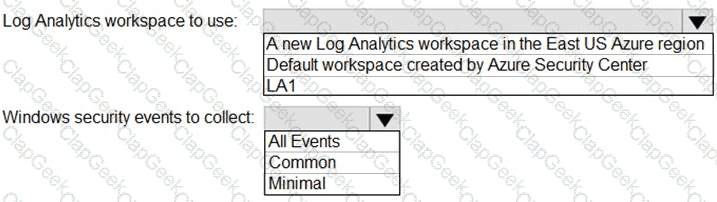
You need to implement Azure Defender to meet the Azure Defender requirements and the business requirements.
What should you include in the solution? To answer, select the appropriate options in the answer area.
NOTE: Each correct selection is worth one point.
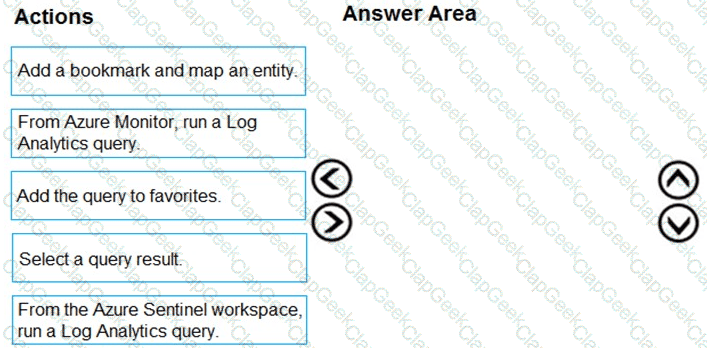
You need to add notes to the events to meet the Azure Sentinel requirements.
Which three actions should you perform in sequence? To answer, move the appropriate actions from the list of action to the answer area and arrange them in the correct order.
You need to create the test rule to meet the Azure Sentinel requirements. What should you do when you create the rule?
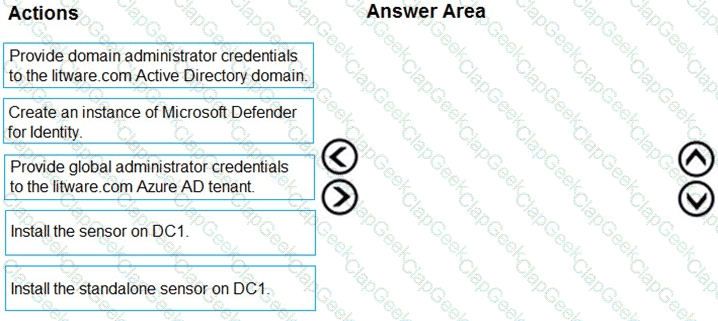
You need to configure DC1 to meet the business requirements.
Which four actions should you perform in sequence? To answer, move the appropriate actions from the list of actions to the answer area and arrange them in the correct order.
The issue for which team can be resolved by using Microsoft Defender for Office 365?
The issue for which team can be resolved by using Microsoft Defender for Endpoint?
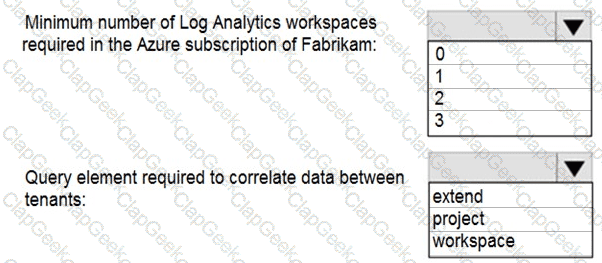
You need to implement Azure Sentinel queries for Contoso and Fabrikam to meet the technical requirements.
What should you include in the solution? To answer, select the appropriate options in the answer area .
NOTE: Each correct selection is worth one point.
You need to ensure that the configuration of HuntingQuery1 meets the Microsoft Sentinel requirements.
What should you do?
You need to configure event monitoring for Server1. The solution must meet the Microsoft Sentinel requirements. What should you create first?
You need to monitor the password resets. The solution must meet the Microsoft Sentinel requirements.
What should you do? To answer, select the appropriate options in the answer area.
NOTE: Each correct selection is worth one point.
You need to ensure that the Group1 members can meet the Microsoft Sentinel requirements.
Which role should you assign to Group1?
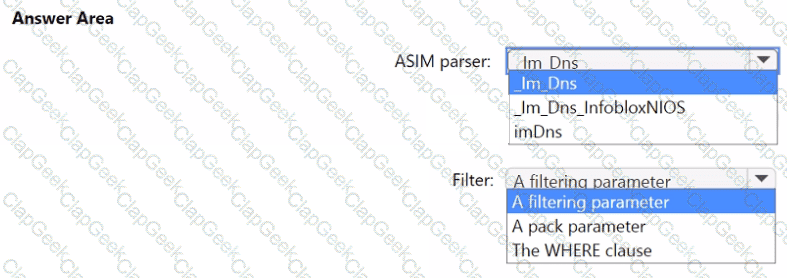
You need to implement the ASIM query for DNS requests. The solution must meet the Microsoft Sentinel requirements. How should you configure the query? To answer, select the appropriate options in the answer area. NOTE: Each correct selection is worth one point.
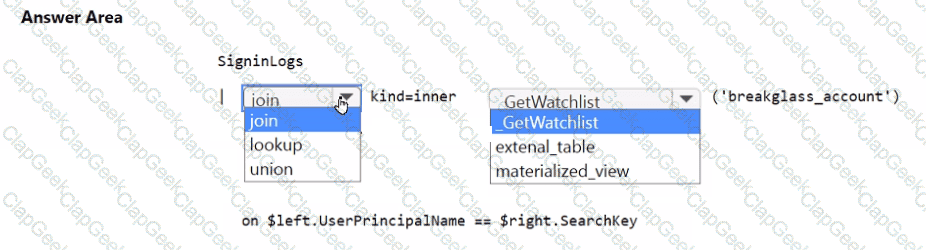
You need to implement the Microsoft Sentinel NRT rule for monitoring the designated break glass account. The solution must meet the Microsoft Sentinel requirements.
How should you complete the query? To answer, select the appropriate options in the answer area.
NOTE: Each correct selection is worth one point.
You need to implement the Defender for Cloud requirements.
What should you configure for Server2?
You need to implement the Defender for Cloud requirements.
Which subscription-level role should you assign to Group1?
You need to ensure that the processing of incidents generated by rulequery1 meets the Microsoft Sentinel requirements.
What should you create first?
You need to implement the scheduled rule for incident generation based on rulequery1.
What should you configure first?


