A user notifies a network administrator about losing access to a remote file server. The network administrator is able to ping the server and verifies the current firewall rules do not block access to the network fileshare. Which of the following tools wold help identify which ports are open on the remote file server?
Which of the following protocols has a default administrative distance value of 90?
Which of the following steps of the troubleshooting methodology would most likely involve comparing current throughput tests to a baseline?
After changes were made to a firewall, users are no longer able to access a web server. A network administrator wants to ensure that ports 80 and 443 on the web server are still accessible from the user IP space. Which of the following commands is best suited to perfom this testing?
A network administrator is setting up two new firewalls for redundancy and needs to implement a redundant internet connection. Which of the following routing technologies will the administrator most likely use?
An employee in a corporate office clicks on a link in an email that was forwarded to them. The employee is redirected to a splash page that says the page is restricted. Which of the following security solutions is most likely in place?
A user ' s desk has a workstation and an IP phone. The user is unable to browse the internet on the workstation, but the phone works. Which of the following configurations is required?
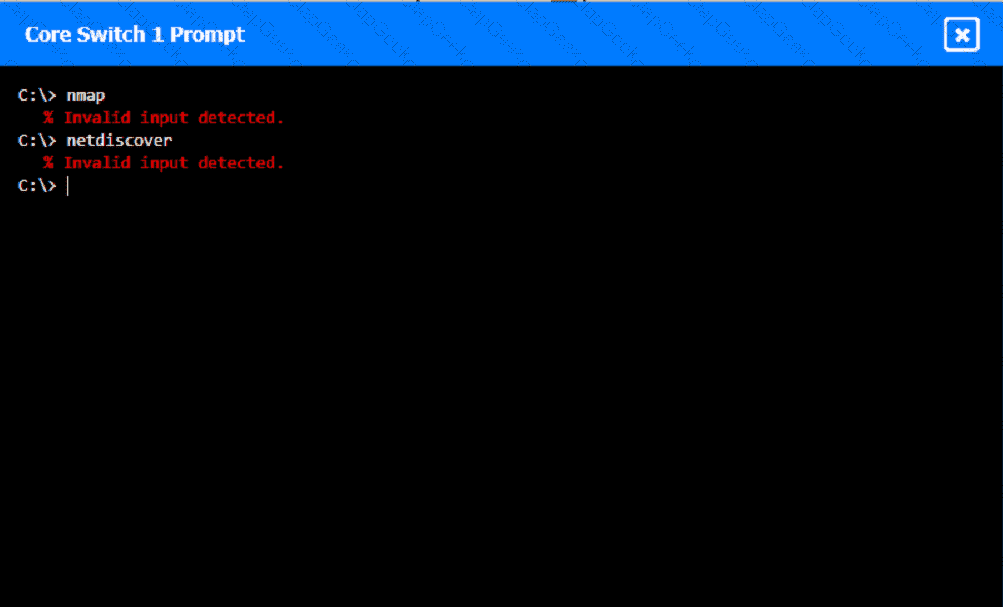
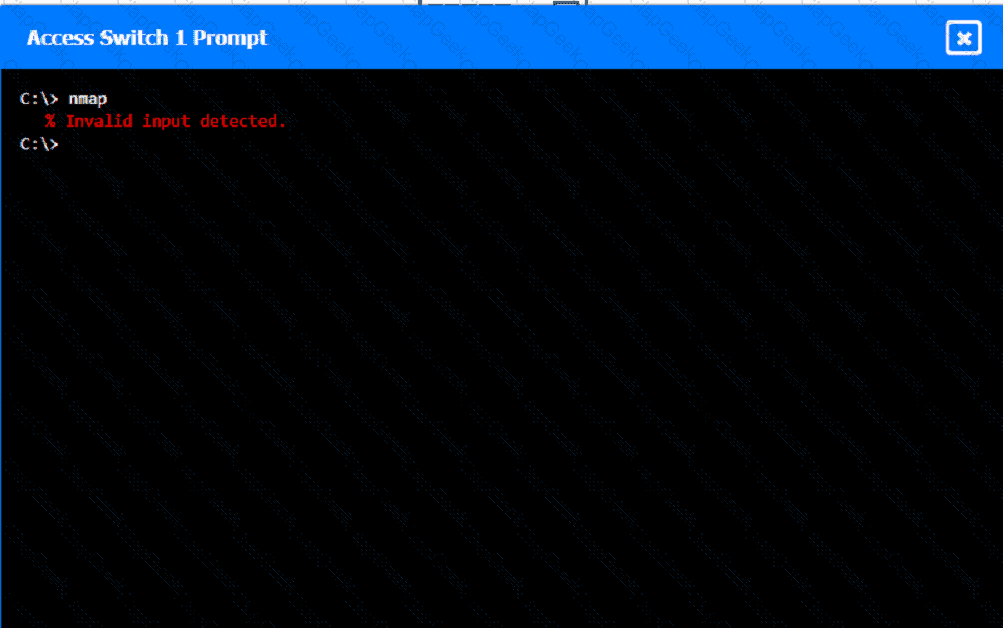
A network technician was recently onboarded to a company. A manager has
tasked the technician with documenting the network and has provided the technician With partial information from previous documentation.
Instructions:
Click on each switch to perform a network discovery by entering commands into the terminal. Fill in the missing information using drop-down menus provided.
Which of the following OSI model layers can utilize a connectionless protocol for data transmission?
A support agent receives a report that a remote user’s wired devices are constantly disconnecting and have slow speeds. Upon inspection, the support agent sees that the user’s coaxial modern has a signal power of -97dB.
Which of the following is used to store and deliver content to clients in a geographically distributed manner using edge servers?
A company wants to implement a disaster recovery site or non-critical applicance, which can tolerance a short period of downltime. Which of the followig type of sites should the company impelement to achive this goal?
Which of the following cloud service models most likely requires the greatest up-front expense by the customer when migrating a data center to the cloud?
A network administrator needs to divide a Class B network into four equal subnets, each with a host range of 1,000 hosts. Which of the following subnet masks should the administrator use?
Which of the following routing protocols needs to have an autonomous system set in order to establish communication with neighbor devices?
A network administrator recently updated configurations on a Layer 3 switch. Following the updates, users report being unable to reach a specific file server. Which of the following is the most likely cause?
A network engineer is completing a wireless installation in a new building. A requirement is that all clients be able to automatically connect to the fastest supported network. Which of the following best supports this requirement?
Which of the following terms describes the capability in a public cloud to add or remove compute resources based on need?
Two companies successfully merged. Following the merger, a network administrator identified a connection bottleneck. The newly formed company plans to acquire a high-end 40GB switch and redesign the network from a three-tier model to a collapsed core. Which of the following should the administrator do until the new devices are acquired?
A network administrator performed upgrades on a server and installed a new NIC to improve performance. Following the upgrades, usera are unable to reach the server. Which of the following is the most likely reason.
Which of the following troubleshooting steps provides a change advisory board with the information needed to make a decision?
Which of the following is the best VPN to use for reducing data bandwidth requirements of the corporate network?
Which of the following types of network architecture typically uses leased lines to provide dedicated, private connections between multiple satellite offices and a head office?
A network engineer is troubleshooting connectivity for a newly installed server on an existing VLAN. The engineer reviews the following output:
C:\ > ipconfig
IP Address: 192.168.100.225
Mask: 255.255.255.224
Gateway: 192.168.100.254
Router# show ip route
C 192.168.100.0/24 is directly connected, GigabitEthernet0/0
Which of the following describes the issue?
A network administrator is configuring a wireless network with an ESSID. Which of the following is a user benefit of ESSID compared to SSID?
A client wants to increase overall security after a recent breach. Which of the following would be best to implement? (Select two.)
Three access points have Ethernet that runs through the ceiling. One of the access points cannot reach the internet. Which of the following tools can help identify the issue?
A network technician is attempting to harden a commercial switch that was recently purchased. Which of the following hardening techniques best mitigates the use of publicly available information?
Which of the following layers in the OSI model is responsible for establishing, maintaining, and terminating connections between nodes?
A network administrator needs to connect a department to a new network segment. They need to use a DHCP server located on another network. Which of the following can the administrator use to complete this task?
A network administrator wants to increase network security by preventing client devices from communicating directly with each other on the same subnet. Which of the following technologies should be implemented?
A network engineer configures the network settings in a new server as follows:
IP address = 192.163.1.15
Subnet mask = 255.255.255.0
Gateway = 192.163.1.255
The server can reach other hosts on the same subnet successfully, but it cannot reach hosts on different subnets. Which of the following is most likely configured incorrectly?
Which of the following is the best way to keep devices on during a loss of power?
A network technician is terminating a cable to a fiber patch panel in the MDF. Which of the following connector types is most likely in use?
A junior network administrator is auditing the company network and notices incrementing input errors on a long-range microwave interface. Which of the following is the most likely reason for the errors?
A government entity wants to implement technology that can block websites based on country code. Which of the following will best enable this requirement?
A group of users cannot connect to network resources. The technician runs ipconfig from one user ' s device and is able to ping the gateway shown from the command. Which of the following is most likely preventing the users from accessing network resources?
A company is implementing a wireless solution in a high-density environment. Which of the following 802.11 standards is used when a company is concerned about device saturation and converage?
A network engineer needs to order cabling to connect two buildings within the same city. Which of the following media types should the network engineer use?
A network administrator needs to create a way to redirect a network resource that has been on the local network but is now hosted as a SaaS solution. Which of the following records should be used to accomplish the task?
A medical clinic recently configured a guest wireless network on the existing router. Since then, guests have been changing the music on the speaker system. Which of the following actions should the clinic take to prevent unauthorized access? (Select two).
A newly opened retail shop uses a combination of new tablets, PCs, printers, and legacy card readers. Which of the following wireless encryption types is the most secure and compatible?
An IT department is considering implementing a SIEM solution to improve network security. The department wants to ensure that the SIEM system is able to ingest and analyze logs from all of the company’s core devices. Which of the following is the most important consideration when selecting a SIEM solution?
A network administrator receives complaints of intermittent network connectivity issues. The administrator investigates and finds that the network design contains potential loop scenarios. Which of the following should the administrator do?
Which of the following troubleshooting steps would provide a change advisory board with the information needed to make a decision?
A detective is investigating an identity theft case in which the target had an RFID-protected payment card issued and compromised in the same day. The only place the target claims to have used the card was at a local convenience store. The detective notices a video camera at the store is placed in such a way that customers ' credentials can be seen when they pay. Which of the following best explains this social engineering technique?
Ten new laptops are added to an existing network, and they can only communicate with one another. An administrator reviews documentation and sees the following:
Subnet: 10.8.100.1/24
Scope: 10.8.100.50 – 10.8.100.150
Reservation: 10.8.100.151 – 10.8.100.175
A technician scans the network and receives the following results:
IP addresses used: 10.8.100.45 – 10.8.100.175
Which of the following should be done to ensure connectivity on all laptops?
Which of the following best describes the amount of time between a disruptive event and the point that affected resources need to be back to fully functional status?
A company ' s marketing team created a new application and would like to create a DNS record for newapplication.comptia.org that always resolves to the same address as www.comptia.org. Which of the following records should the administrator use?
While troubleshooting a VoIP handset connection, a technician ' s laptop is able to successfully connect to network resources using the same port. The technician needs to identify the port on the switch. Which of the following should the technician use to determine the switch and port?
A network administrator notices interference with industrial equipment in the 2.4GHz range. Which of the following technologies would most likely mitigate this issue? (Select two).
A network administrator is trying to troubleshoot an issue with a newly installed switch that is not connecting to the network. The administrator logs on to the switch and observes collisions on the interface. Which of the following is most likely the issue?
After installing a series of Cat 8 keystones, a data center architect notices higher than normal interference during tests. Which of the following steps should the architect take to troubleshoot the issue?
Due to concerns around single points of failure, a company decided to add an additional WAN to the network. The company added a second MPLS vendor to the current MPLS WAN and deployed an additional WAN router at each site. Both MPLS providers use OSPF on the WAN network, and EIGRP is run internally. The first site to go live with the new WAN is successful, but when the second site is activated, significant network issues occur. Which of the following is the most likely cause for the WAN instability?
Which of the following is a type of NAC that uses a set of policies to allow or deny access to the network based on the user’s identity?
A company experiences an incident involving a user who connects an unmanaged switch to the network. Which of the following technologies should the company implement to help avoid similar incidents without conducting an asset inventory?
A small business is deploying new phones, and some of the phones have full HD videoconferencing features. The Chief Information Officer (CIO) is concerned that the network might not be able to handle the traffic if it reaches a certain threshold. Which of the following can the network engineer configure to help ease these concerns?
A network administrator needs to configure the core switches where multiple connections between data centers are used. Given the following requirements:
• Fault tolerance and redundancy
• Vendor interoperability
• Increased bandwidth
• Cost effectiveness
• Simplified management
Which of the following should the administrator configure?
A user called the help desk after business hours to complain that files on a device are inaccessible and the wallpaper was changed. The network administrator thinks that this issue is an isolated incident, but the security analyst thinks the issue might be a ransomware attack. Which of the following troubleshooting steps should be taken first?
A customer migrates its phone system from analog to a new hosted VoIP/software application solution with integrated video. After installation, some users notice issues with dropped calls, broken video, and slow internet access. The issues start in the mid-morning and continue into the afternoon. However, remote users do not report the same issues. Which of the following is the most likely cause of the issues?
Which of the following connection methods allows a network engineer to automate configuration deployment for network devices across the environment?
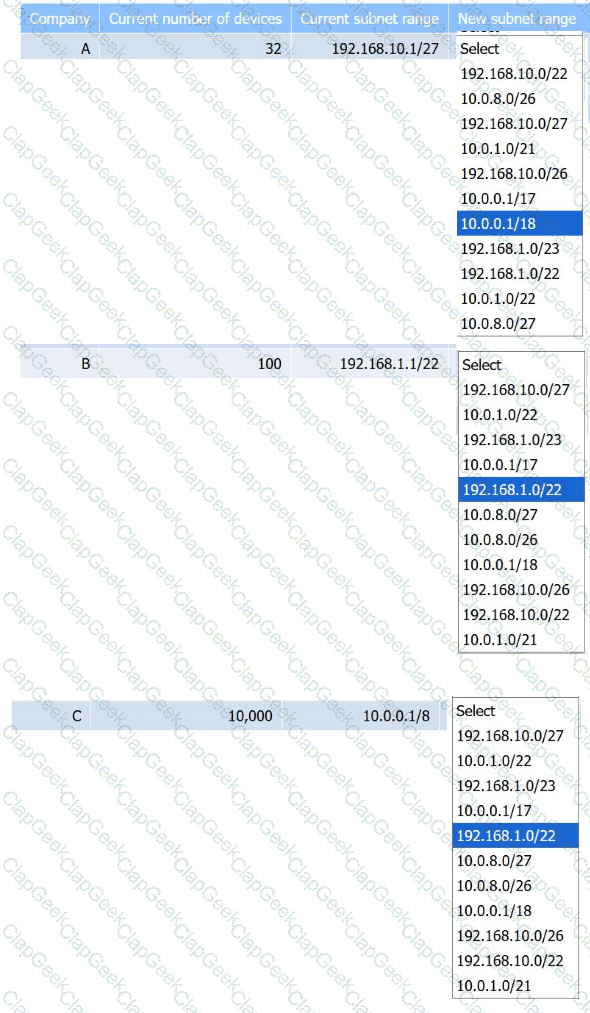
Company C is acquiring Company A and Company B. Company C needs to merge all
three networks into one Class B network. Additionally, the network capacity of each company needs to grow by 20%. Company C also requires segmentation of Company A and Company B to account for unknown security vulnerabilities within each.
Instructions:
Select the correct subnet range to meet Company C ' s requirements.
After a company installed a new IPS, the network is experiencing speed degradation. A network administrator is troubleshooting the issue and runs a speed test. The results from the different network locations are as follows:
LocationSpeed DownSpeed Up
Wireless laptop4.8 Mbps47.1 Mbps
Wired desktop5.2 Mbps49.3 Mbps
Firewall48.8 Mbps49.5 Mbps
Which of the following is the most likely issue?
Newly crimped 26ft (8m) STP Cat 6 patch cables were recently installed in one room to replace cables that were damaged by a vacuum cleaner. Now, users in that room are unable to connect to the network. A network technician tests the existing cables first. The 177ft (54m) cable that runs from the core switch to the access switch on the floor is working, as is the 115ft (35m) cable run from the access switch to the wall jack in the office. Which of the following is the most likely reason the users cannot connect to the network?
A technician needs to quickly set up a network with five wireless devices. Which of the following network types should the technician configure to accomplish this task?
A network administrator wants users to be able to authenticate to the corporate network using a port-based authentication framework when accessing both wired and wireless devices. Which of the following is the best security feature to accomplish this task?
Which of the following attacks forces a switch to send all traffic out of all ports?
A network administrator is configuring a new switch and wants to ensure that only assigned devices can connect to the switch. Which of the following should the administrator do?
Which of the following VPN types provides secure remote access to the network resources through a web portal?
A company reports that their facsimile machine no longer has a dial tone when trying to send a fax. The phone cable is damaged on one end. Which of the following types of connectors should a technician replace?
A laptop user gets an error when trying to access the company ' s intranet site. A technician runs ipconfig /all with the following results:
Autoconfiguration IPv4 Address: 169.254.0.5 (Preferred)
Subnet Mask . . . . . . . . . . . : 255.255.0.0
Default Gateway . . . . . . . . . :
DHCP Server . . . . . . . . . . . :
Which of the following is most likely causing the issue?
A data center administrator is evaluating the use of jumbo frames within a storage environment. Which of the following describes the best reason to use jumbo frames in the storage environment?
Which of the following is most likely responsible for the security and handling of personal data in Europe?
A customer calls the help desk to report that resources are no longer reachable. The resources were available before network changes were made. The technician verifies the report, investigates, and discovers that a new logical layout is segmenting the network using tagging. Which of the following appliances most likely needs to be reviewed to restore the connections?
A network administrator is responding to a request to configure a new IP phone. Which of the following should the network administrator do to allow data and voice traffic to be properly prioritized?
A user tries to visit a website, but instead of the intended site, the page displays vmw.cba.com. Which of the following should be done to reach the correct website?
Which of the following physical installation factors is the most important when a network switch is installed in a sealed enclosure?
Which of the following network traffic type is sent to all nodes on the network?
Which of the following protocols uses the Dijkstra ' s Link State Algorithm to establish routes inside its routing table?
A network technician needs to connect a new user to the company’s Wi-Fi network called SSID: business. When attempting to connect, two networks are listed as possible choices: SSID: business and SSID: myaccess. Which of the following attacks is occurring?
A user tries to visit www.abc.com, but the website that displays is www.cba.com. Which of the following should be done in order to reach the correct website?
A network technician is troubleshooting a faulty NIC and tests the theory. Which of the following should the technician do next?
Which of the following is the best networking appliance for interconnecting multiple logical networks and forwarding data packets between them while minimizing latency?
Users at an organization report that the wireless network is not working in some areas of the building. Users report that other wireless network SSIDs are visible when searching for the network, but the organization ' s network is not displayed. Which of the following is the most likely cause?
Which of the following can be used when a server at a remote site is physically unreachable?
Which of the following layers of the OSI model is responsible for end-to-end encryption?
A company is upgrading its wireless network. Currently, each AP broadcasts a wireless LAN name depending on the location in the building. Which of the following configurations allows a single wireless LAN name to be broadcast across the entire building?
Users are reporting issues with mobile phone connectivity after a cellular repeater was recently installed. Users also note that the phones are rapidly losing battery charge. Which of the following should the technician check first to troubleshoot the issue?
A systems administrator is looking for operating system information, running services, and network ports that are available on a server. Which of the following software tools should the administrator use to accomplish this task?
Which of the following is the part of a disaster recovery (DR) plan that identifies the critical systems that should be recovered first after an incident?
Which of the following is an XML-based security concept that works by passing sensitve information about users, such as log-in information and attributes, to providers.
A technician is troubleshooting wireless connectivity near a break room. Whenever a user turns on the microwave, connectivity to the user ' s laptop is lost. Which of the following frequency bands is the laptop most likely using?
Which of the following is the best example of a networking appliance that connects different network segments and directs allowed traffic between specific segments?
While troubleshooting connectivity issues, a junior network administrator is given explicit instructions to test the host ' s TCP/IP stack first. Which of the following commands should the network administrator run?
A systems administrator needs to connect two laptops to a printer via Wi-Fi. The office does not have access points and cannot purchase any. Which of the following wireless network types best fulfills this requirement?
Which of the following allows an organization to map multiple internal devices to a single external-facing IP address?
A small business is choosing between static and dynamic routing for its network. Which of the following is the best reason to use dynamic routing in a growing network?
A network engineer receives a vendor alert regarding a vulnerability in a router CPU. Which of the following should the engineer do to resolve the issue?
Which of the following best describes the purpose of a UPS and PDU in a network installation?
In the troubleshooting methodology, which of the following actions comes after verifying that the initial problem has been resolved?
Which of the following is associated with avoidance, acceptance, mitigation, and transfer?
Which of the following actions should be taken as part of the first step of the troubleshooting methodology?
Which of the following allows a user to connect to an isolated device on a stand-alone network?
A network administrator needs to limit devices that can connect to a small wireless network. The network consists of less than ten unique laptops, and no network changes are anticipated. Which of the following is the simplest way to accomplish this task?
A user ' s home mesh wireless network is experiencing latency issues. A technician has:
•Performed a speed test.
•Rebooted the devices.
•Performed a site survey.
•Performed a wireless packet capture.
The technician reviews the following information:
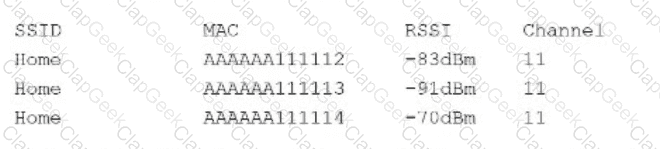
The technician notices in the packet capture that frames were retransmitted. Which of the following is the most likely cause of the user ' s network issue?
A virtual machine has the following configuration:
•IPv4 address: 169.254.10.10
•Subnet mask: 255.255.0.0
The virtual machine can reach colocated systems but cannot reach external addresses on the Internet. Which of the following Is most likely the root cause?
A company wants to implement data loss prevention by restricting user access to social media platforms and personal cloud storage on workstations. Which of the following types of filtering should the company deploy to achieve these goals?
A network manager connects two switches together and uses two connecting links. Which of the following configurations will prevent Layer 2 loops?
A network technician is examining the configuration on an access port and notices more than one VLAN has been set. Which of the following best describes how the port is configured?
Which of the following attacks can cause users who are attempting to access a company website to be directed to an entirely different website?
A customer purchases a new UTM device and wants the development team to integrate some of the device’s data-reporting capabilities into the company’s custom internal support software. Which of the following features should the development team use to obtain the device’s data?
Which of the following is the most secure way to provide site-to-site connectivity?
Which of the following, in addition to a password, can be asked of a user for MFA?
After a recent merger, a large number of alerts are coming in regarding extremely high utilization. Which of the following should be generated to help inform new alerting requirements?
A network engineer needs to add a boundary network to isolate and separate the internal network from the public-facing internet. Which of the following security defense solutions would best accomplish this task?
Which of the following is the most closely associated with segmenting compute resources within a single cloud account?
A junior network technician at a large company needs to create networks from a Class C address with 14 hosts per subnet. Which of the following numbers of host bits is required?
A systems administrator is configuring a new device to be added to the network. The administrator is planning to perform device hardening prior to connecting the device. Which of the following should the administrator do first?
A network administrator is creating a subnet that will include 45 separate hosts on a small private network within a large network architecture. Which of the following options is the most efficient use of network addresses when assigning this network?
Which of the following ports should a network administrator enable for encrypted login to a network switch?
Which of the following VPN configurations forces a remote user to access internet resources through the corporate network?
A new SQL server is identified as allowing FTP access to all users. Which of the following would a systems administrator most likely do to ensure only the required services are allowed?
A network engineer is designing an internal network that needs to support both IPv4 and IPv6 routing. Which of the following routing protocols is capable of supporting both IPv4 and IPv6?
A network administrator is managing network traffic so that classified services and applications are prioritized. Which of the following technologies should the network administrator use?
Three new employees report that they are unable to access company resources, but they can connect to each other’s devices. Which of the following would most likely need to be modified to resolve the issue?
After installing a new 6E wireless router in a small office, a technician notices that some wireless devices are not able to achieve the rated speeds.
Which of the following should the technician check to troubleshoot the issue? (Select two)
During a VoIP call, a user notices inconsistent audio and logs an incident ticket. A network administrator notices inconsistent delays in arrival of the RTP packets. Which of the following troubleshooting tools should the network administrator use to determine the issue?
An organization recently connected a new computer to the LAN. The user is unable to ping the default gateway. The technician examines the configuration and sees a self-assigned IP address. Which of the following is the most likely cause?
A network administrator wants to restrict inbound traffic to allow only HTTPS to the company website, denying all other inbound traffic from the internet. Which of the following would best accomplish this goal?
Users at a satellite office are experiencing issues when using videoconferencing. Which of the following should a technician focus on first to rectify these issues?
A client with a 2.4GHz wireless network has stated that the entire office is experiencing intermittent issues with laptops after the WAP was moved. Which of the following is the most likely reason for these issues?
Employees report that the network is slow. The network engineer thinks the performance issue is with an upstream router. Which of the following tools should the engineer use to determine the location of the issue?
A network administrator manages multiple computers and notices that three computers are no longer communicating with the network. Which of the following commands best identifies whether other devices are restricting packet traffic?
Which of the following connector types would most likely be used to connect to an external antenna?
A network administrator is extending a network beyond the primary equipment location. Which of the following is where the administrator should install additional network switches?
A customer recently moved into a new office and notices that some wall plates are not working and are not properly labeled Which of the following tools would be best to identify the proper wiring in the IDF?
A network administrator wants to implement security zones in the corporate network to control access to only individuals inside of the corporation. Which of the following security zones is the best solution?
A network engineer configures a NIC that has an IP address of 192.168.123.232. Which of the following classes is this address an example of?
Which of the following is the greatest advantage of maintaining a cold DR site compared to other DR sites?
A network administrator installs a node that requires a media converter to connect Ethernet to fiber but sees no link light on the node. The administrator notices the following:
Both terminating points are properly seated.
Both the fiber and Ethernet cables have been successfully tested.
The media converter is turned on.
The switchport is configured as half duplex.
Which of the following is the reason the link light is not on?
A company recently rearranged some users ' workspaces and moved several users to previously used workspaces. The network administrator receives a report that all of the users who were moved are having connectivity issues. Which of the following is the MOST likely reason?
Which of the following steps in the troubleshooting methodology comes after using a top-to-top buttom examination of the OSI model to determine cause?
A network administrator upgraded the wireless access points and wants to implement a configuration that will give users higher speed and less channel overlap based on device compatibility. Which of the following will accomplish this goal?
Which of the following helps a network administrator understand security risk from external malicious actors and offers insights on which threats to mitigate?
An organization wants better network visibility. The organization ' s requirements include:
Multivendor/OS-monitoring capabilities
Real-time collection
Data correlation
Which of the following meets these requirements?
A Chief Executive Officer (CEO) of a company purchases a new phone that will be used while traveling to different countries. The CEO needs to be able to place outgoing calls and receive incoming calls on the phone using a SIM card. Which of the following cellular technologies does the CEO ' s phone need?
A public library wants to implement a solution in which users need to connect to the wireless network and then authenticate via HTTPS with provided credentials. Which of the following technologies fulfills this requirement?
Which of the following ports is used to transfer data between mail exchange servers?
A network engineer adds a tunnel for a new branch network. Which of the following ensures that all data is encrypted inside the tunnel?
A technician is designing a cloud service solution that will accommodate the company ' s current size, compute capacity, and storage capacity. Which of the following cloud deployment models will fulfill these requirements?


