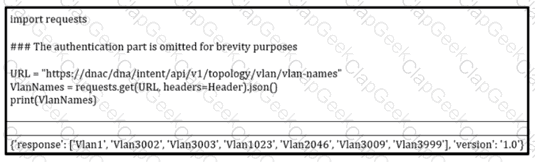
Refer to the exibit. How should the programmer access the list of VLANs that are recevied via the API call?
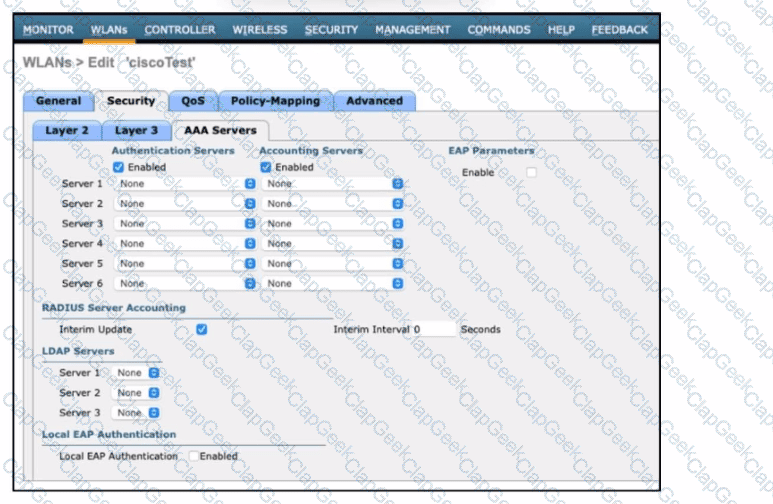
Refer to the exhibit. An engineer must configure a Cisco WLC with WPA2 Enterprise mode and avoid global server lists. Which action is required?
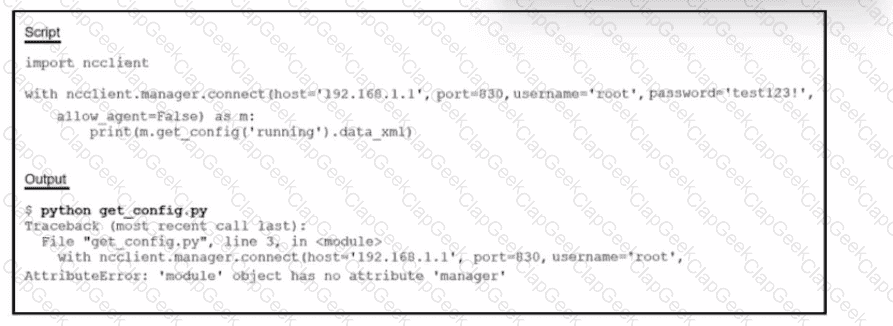
Refer to the exhibit. Running the script causes the output in the exhibit. What should be the first line of the script?
Which solution should be used in a high-density wireless environment to increase bandwidth for each user?
Which DNS record type is needed to allow a Cisco AP to discover a WLC when using IPv4?
When using a Cisco Catalyst 9800 Series WLC, which tag/profile can be applied to APs to change the mode to FlexConnect in a specific location?
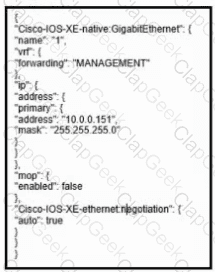
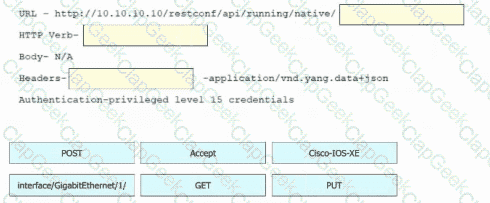
Refer to the exhibit. Drag and drop the snippets into the RESTCONF request to form the request that returns this response. Not all options are used.
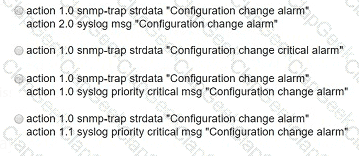
An engineer is implementing a new SSID on a Cisco Catalyst 9800 Series WLC that must be broadcast on 6 GHz radios. Users will be required to use EAP-TLS to authenticate. Which wireless Layer 2 security method is required?
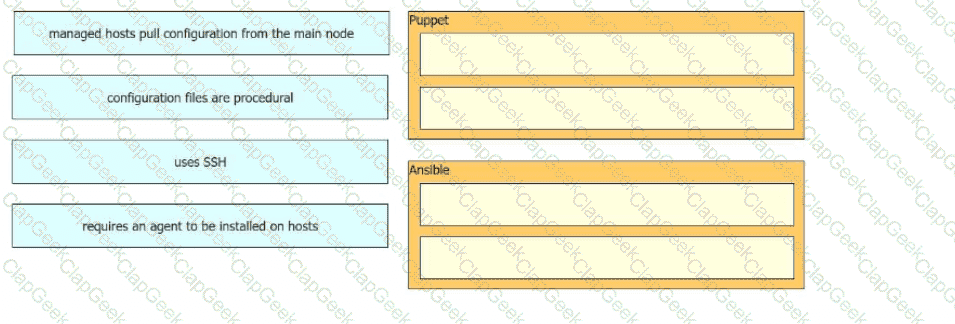
Drag and drop the characteristics from the left onto the orchestration tools that they describe on the right.
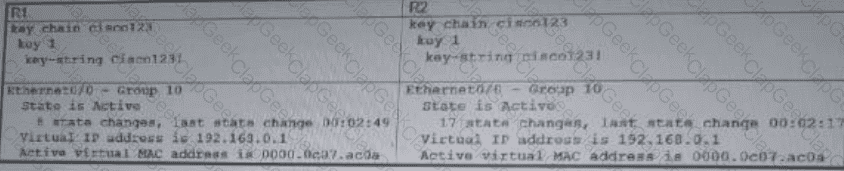
Refer to the exhibit.
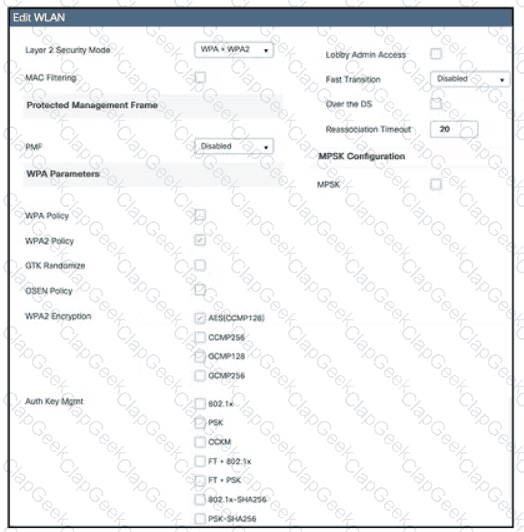
Which action must be taken to configure a WLAN for WPA2-AES with PSK and allow only 802.11r-capable clients to connect?
A customer has two Cisco WLCs that manage separate APs throughout a building. Each WLC advertises the same SSID but terminates on different interfaces. Users report that they drop their connections and change IP addresses when roaming. Which action resolves this issue?
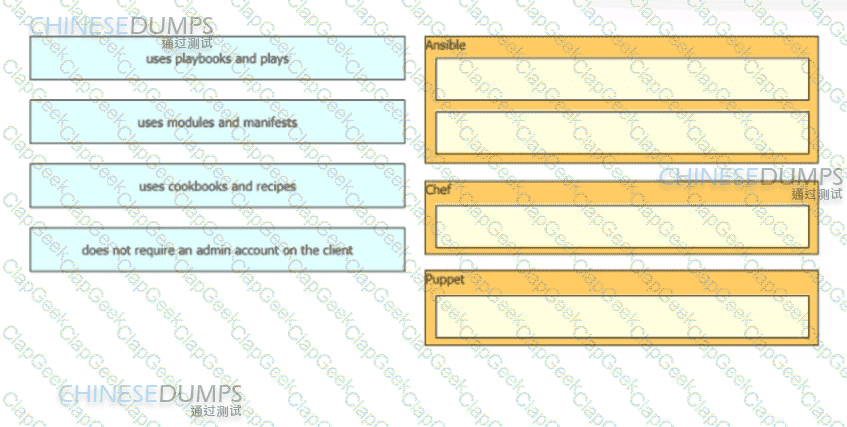
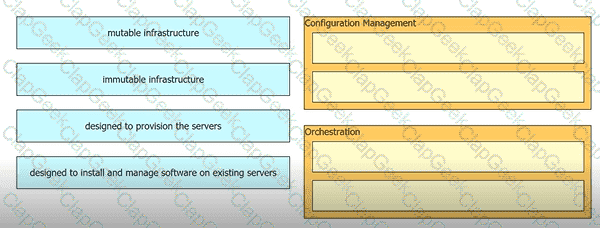
Drag and drop the automation characteristics from the left to the corresponding tools on the right.
Which two mechanisms are used with OAuth 2.0 for enhanced validation? (Choose two.)
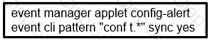
Refer to the exhibit. A network engineer must be notified when a user switches to configuration mode. Which script should be applied to receive an SNMP trap and a critical-level log message?
Refer to the exhibit.
A client requests a new SSID that will use web-based authentication and external RADIUS servers. Which Layer 2 security mode must be selected?
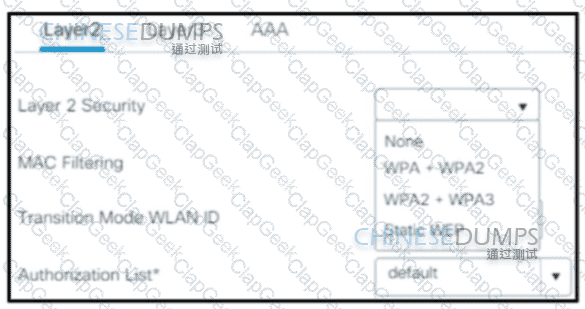
Refer to the exhibit. An engineer must adjust the configuration so that Router A becomes the active router. Which commands should be applied to router A? (Choose two)
Drag and drop the characteristics from the left onto the corresponding orchestration tool on the right.
Which language defines the structure or modeling of data for NETCONF and RESTCONF?
Which First Hop Redundancy Protocol should be used to meet a design requirements for more efficient default bandwidth usage across multiple devices?
Refer to the exhibit.
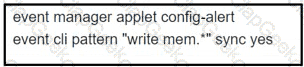
Which EEM script generates a critical-level syslog message and saves a copy of the running configuration to the bootflash when an administrator saves the running configuration to the startup configuration?
Which task Is mandatory when provisioning a device through the plug-and-play workflow in Cisco DNA Center?
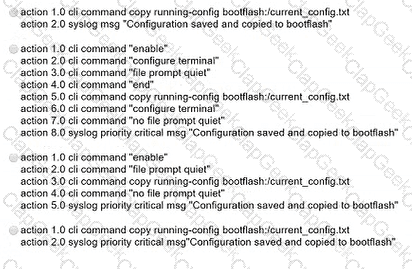
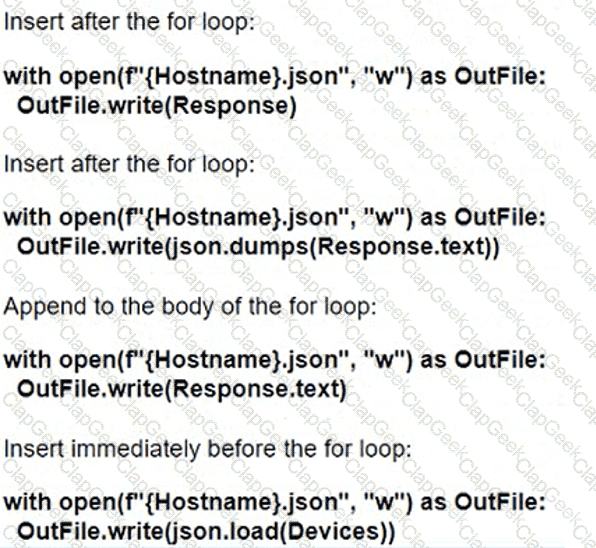
Refer to the exhibit. How should the script be completed so that each device configuration is saved into a JSON-formatted file under the device name?
In a high-density AP environment, which feature can be used to reduce the RF cell size and not demodulate radio packets above a given threshold?
Which devices does Cisco DNA Center configure when deploying an IP-based access control policy?
What is the name of the numerical relationship of the wireless signal compared to the noise floor?
Which technology collects location information through data packets received by the APs instead of using mobile device probes?
Which feature is offered by the Cisco Advanced Malware Protection for Endpoints solution?
Which IEEE standard provides the capability to permit or deny network connectivity based on the user or device identity?
Which HTTP status code is the correct response for a request with an incorrect password applied to a REST API session?
Refer to the exhibit.

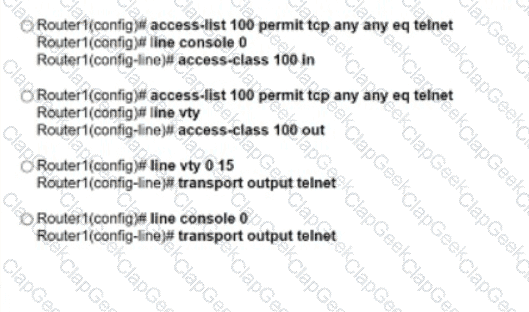
An engineer attempts to connect to another device from Route1’s console port. Which configuration is needed to allow telnet connections?
Which feature works with SSO to continue forwarding packets after a route processor failure until the control plane recovers?
An engineer must configure a new WLAN that supports 802.11r and requires users to enter a passphrase. What must be configured to support this requirement?
An engineer is installing a new pair of routers in a redundant configuration. Which protocol ensures that traffic is not disrupted in the event of a hardware failure?
What is the role of the vSmart controller in a Cisco Catalyst SD-WAN environment?
Which multicast operational mode sends a prune message to the source when there are no connected members or downstream neighbors?
Which two namespaces does the LISP network architecture and protocol use? (Choose two.)
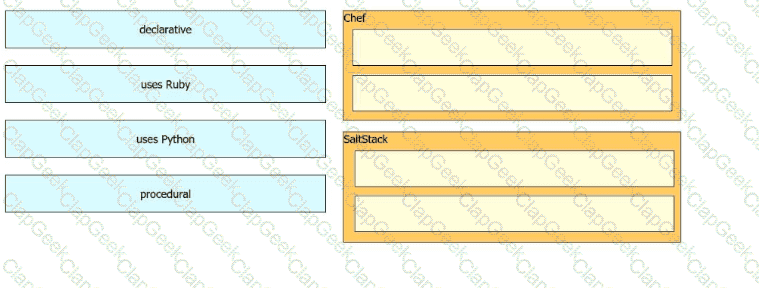
Drag and drop the characteristics from the left onto the orchestration tool classifications on the right.
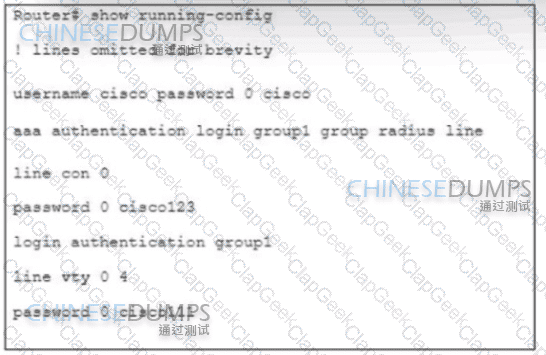
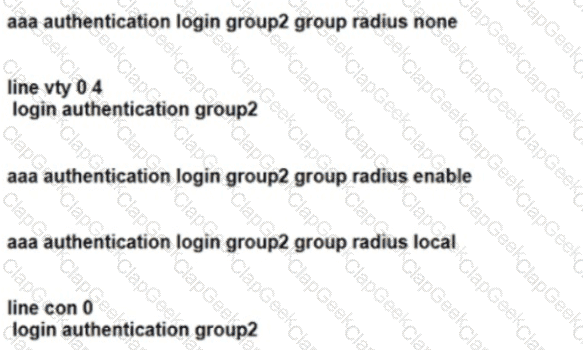
Refer to the exhibit. Authentication for users must first use RADIUS, and fall back to the local database on the router if the RADIUS server is unavailable Which two configuration sets are needed to achieve this result? (Choose two.)
Which two operational modes enable an AP to scan one or more wireless channels for rogue access points and at the same time provide wireless services to clients? (Choose two.)
How can an engineer prevent basic replay attacks from people who try to brute force a system via REST API?
Which function is performed by vSmart in the Cisco Catalyst SD-WAN architecture?


