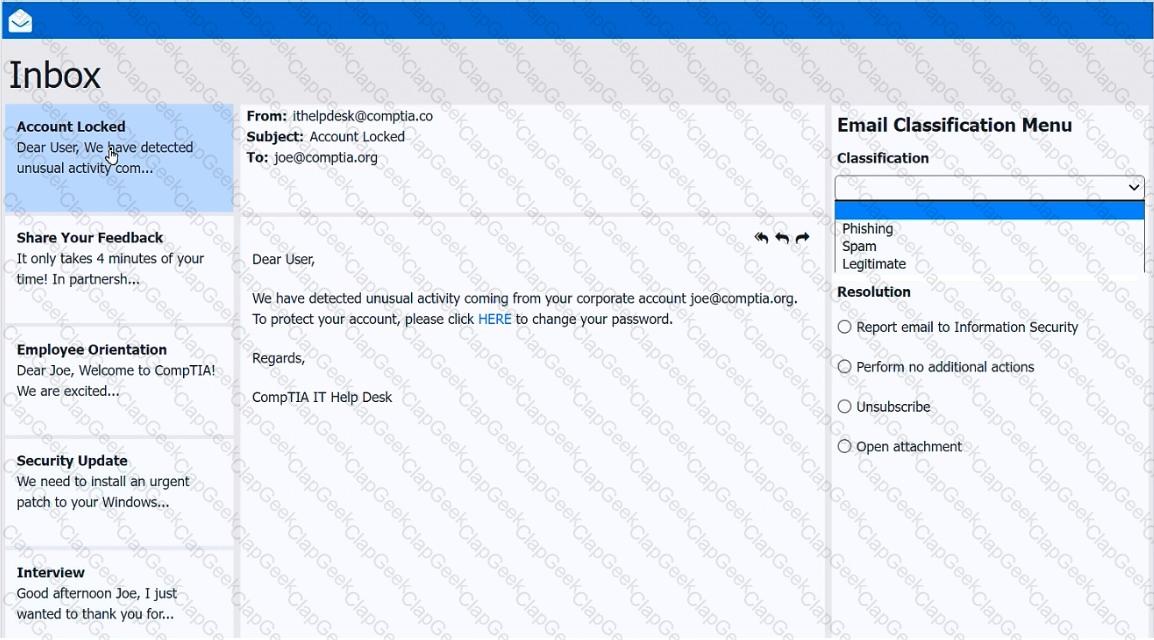
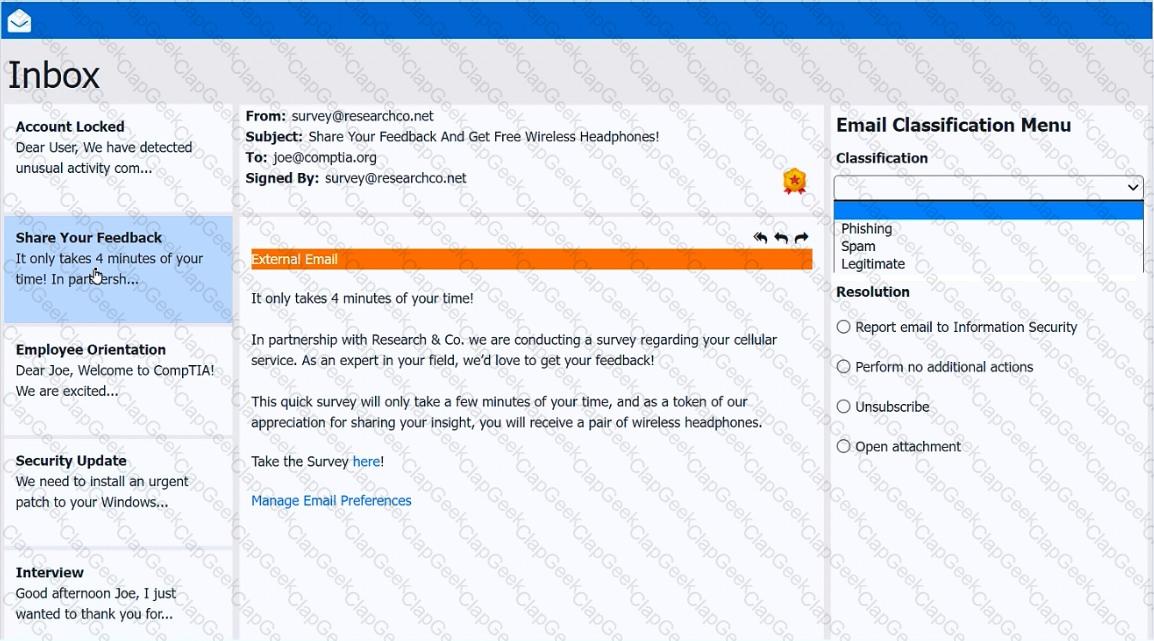
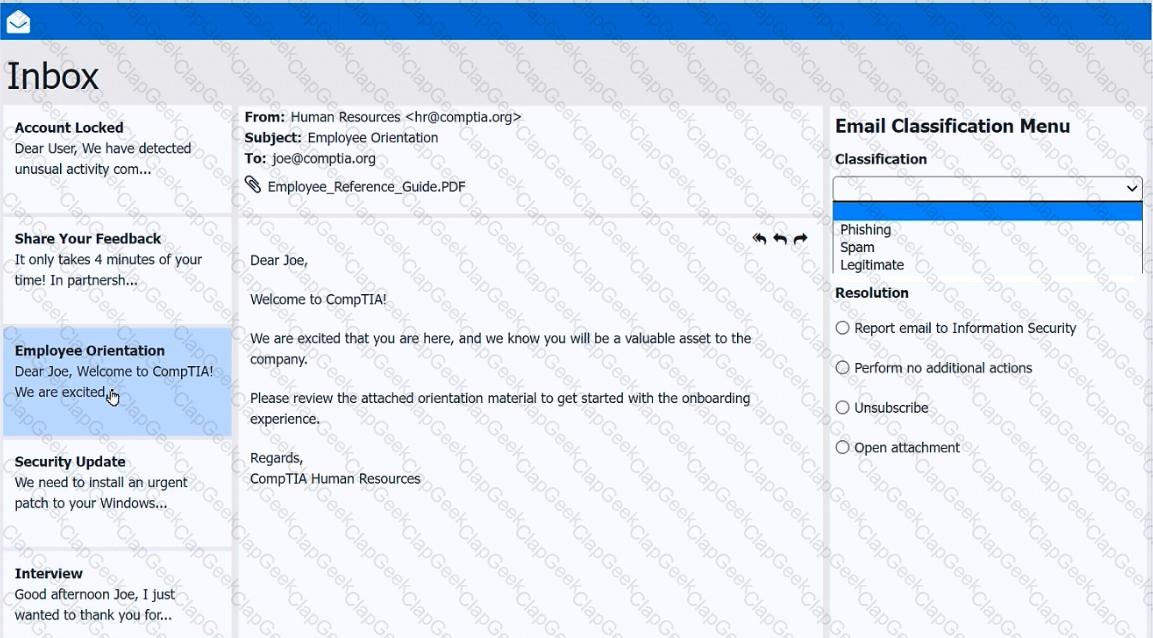
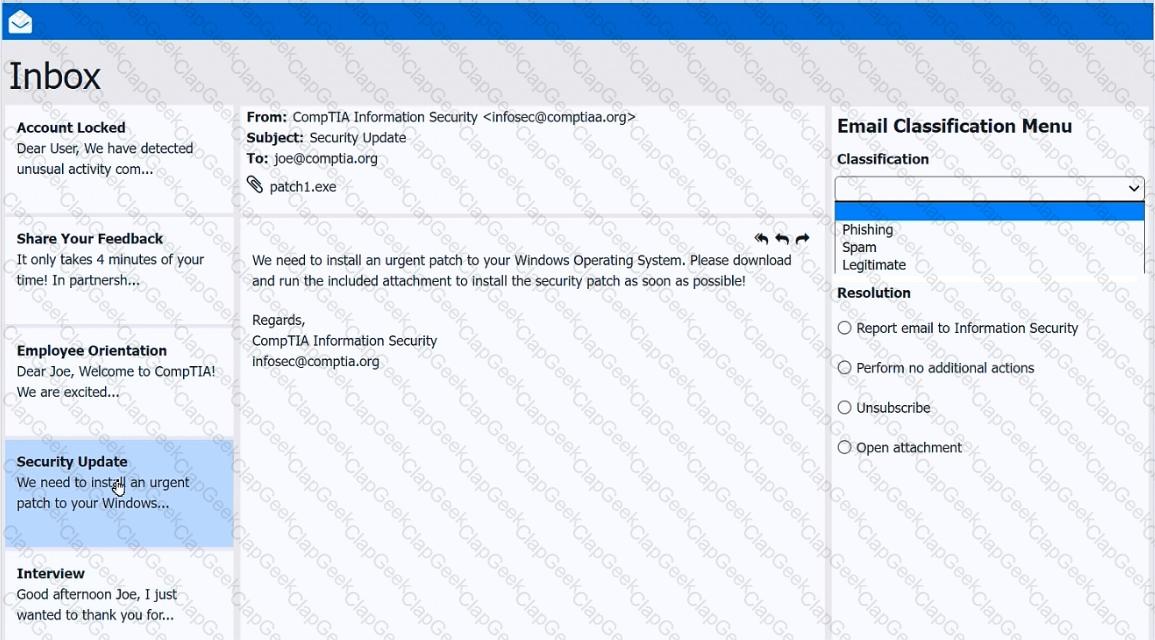
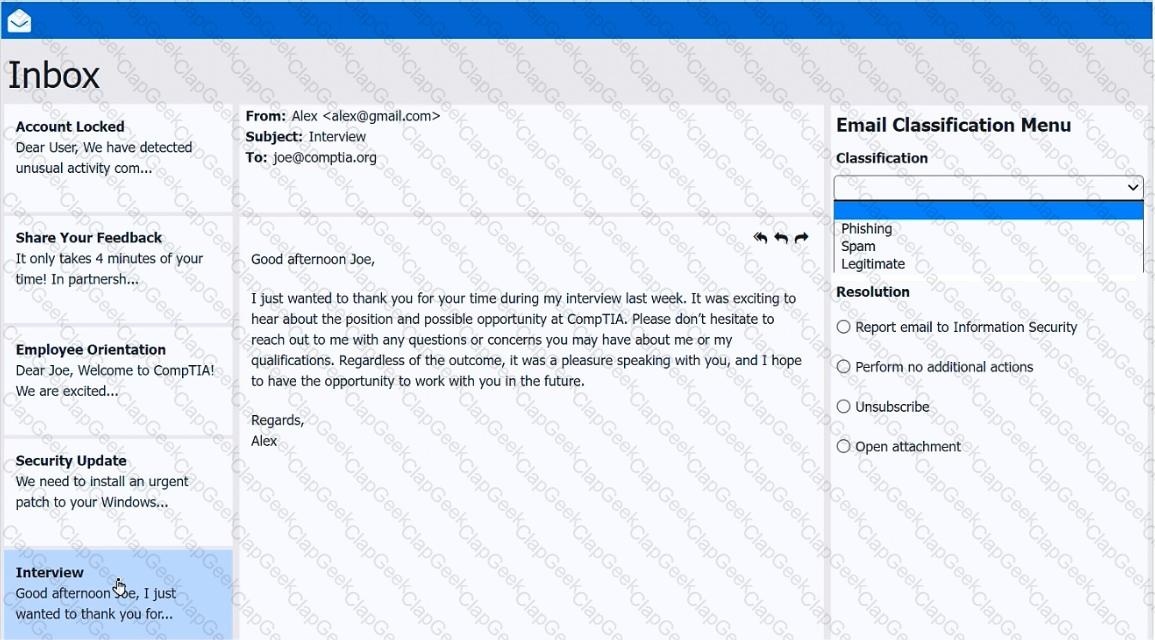
As a corporate technician, you are asked to evaluate several suspect email messages on a client ' s computer. Corporate policy requires the following:
> All phishing attempts must be reported.
> Future spam emails to users must be prevented.
INSTRUCTIONS
Review each email and perform the following within the email:
> Classify the emails
> Identify suspicious items, if applicable, in each email
> Select the appropriate resolution
If at any time you would like to bring back the initial state of the simulation, please click the Reset All button.
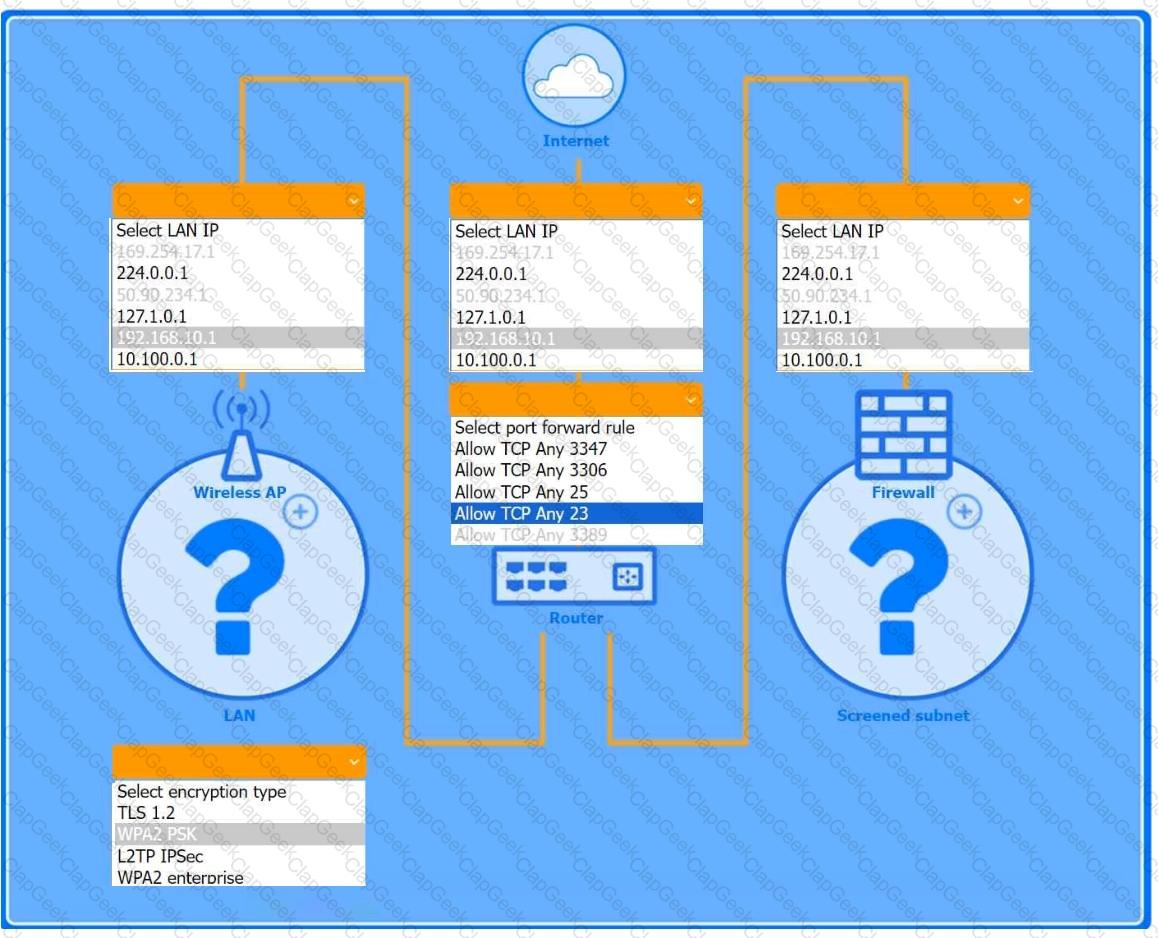
You are configuring a home network for a customer. The customer has requested the ability to access a Windows PC remotely, and needs all chat and optional functions to work in their game console.
INSTRUCTIONS
Use the drop-down menus to complete the network configuration for the customer. Each option may only be used once, and not all options will be used.
Then, click the + sign to place each device in its appropriate location.
If at any time you would like to bring back the initial state of the simulation, please click the Reset All button.
Wireless AP LAN
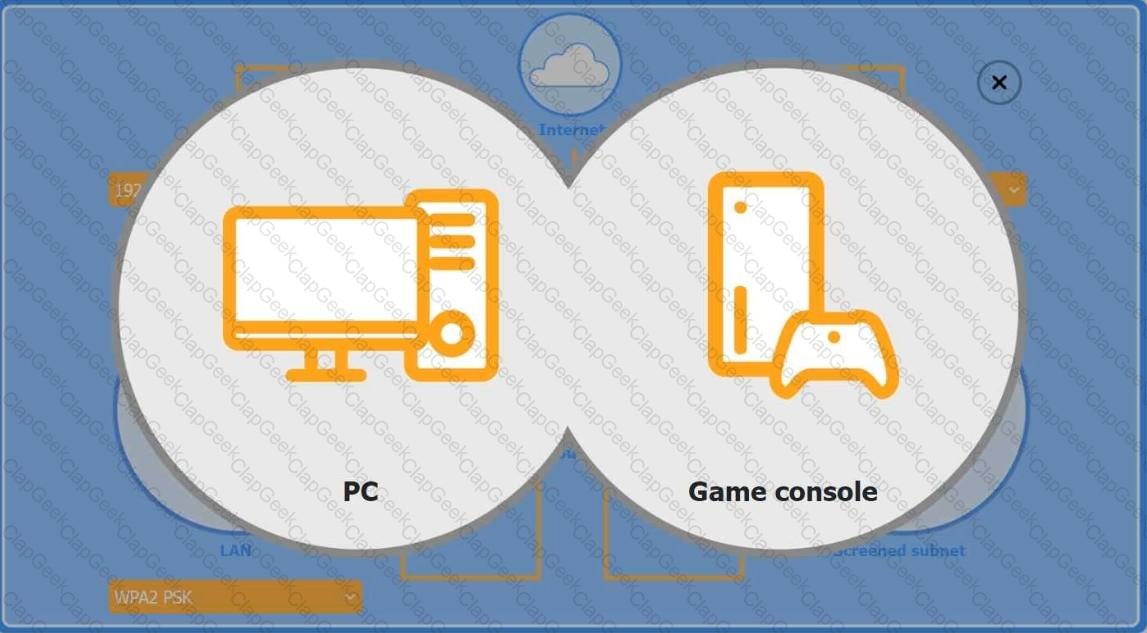
Firewall Screened Subnet
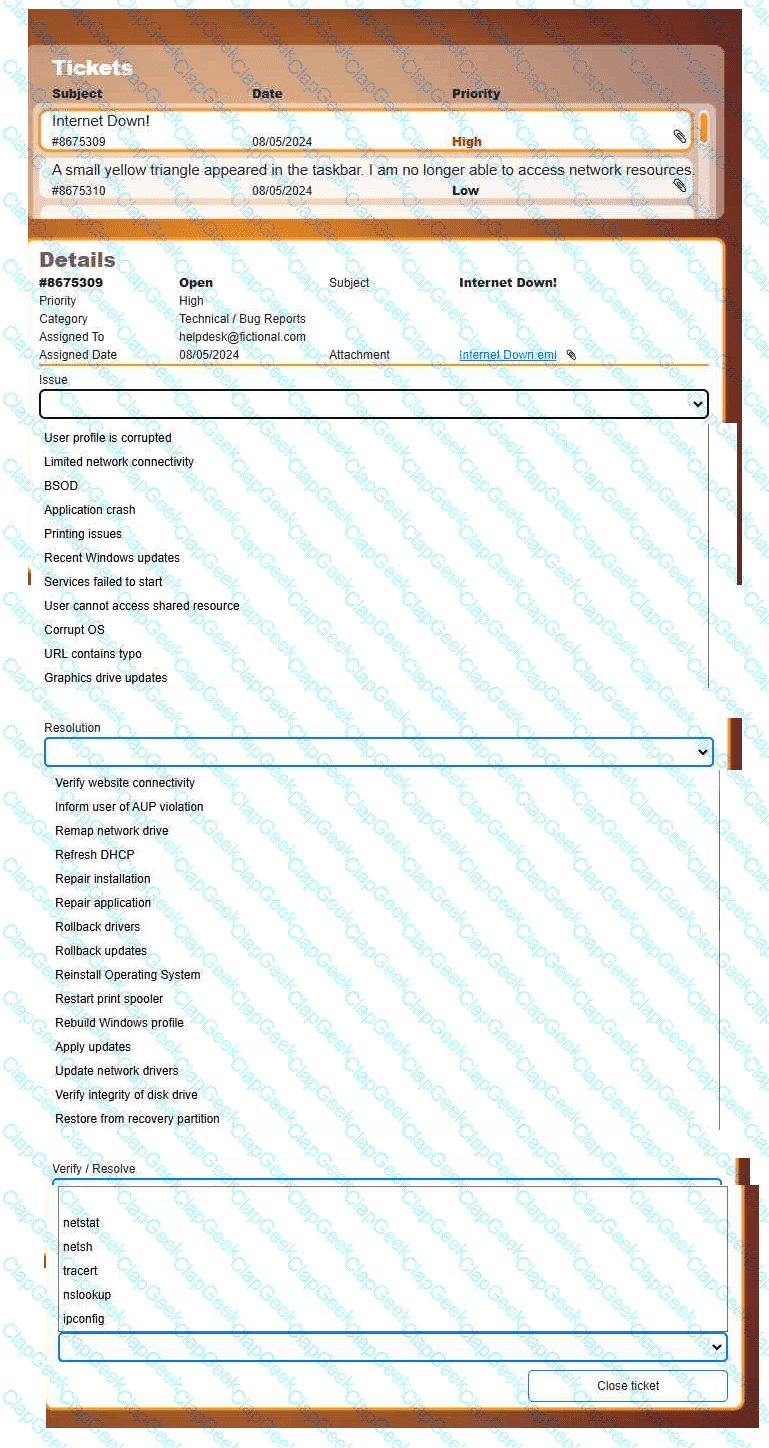
Welcome to your first day as a Fictional Company, LLC helpdesk employee. Please work the tickets in your helpdesk ticket queue.
INSTRUCTIONS
Click on individual tickets to see the ticket details, and view applicable attachments to
determine the problem.
Select the appropriate issue from the ' Issue ' drop-down menu. Then, select the most
efficient resolution from the ' Resolution ' drop-down menu. Finally, select the proper
command or verification to remediate or confirm your fix of the issue from the
' Verify/Resolve ' drop-down menu.
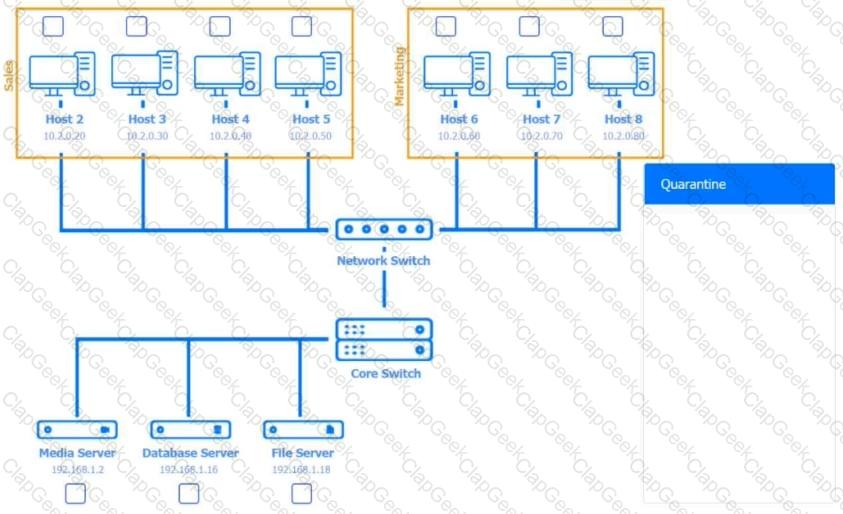
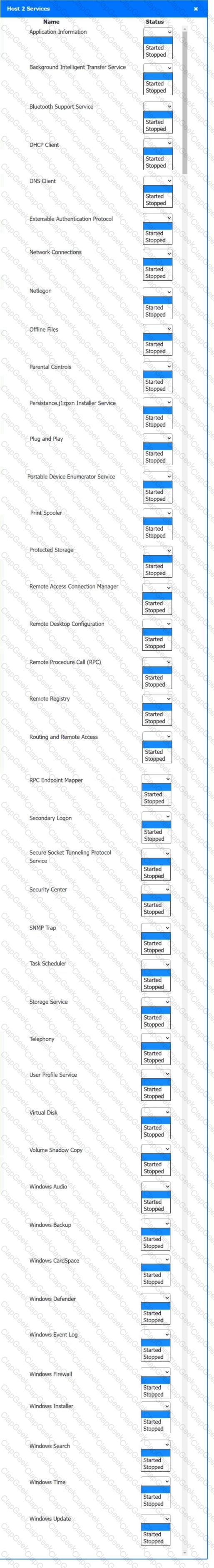
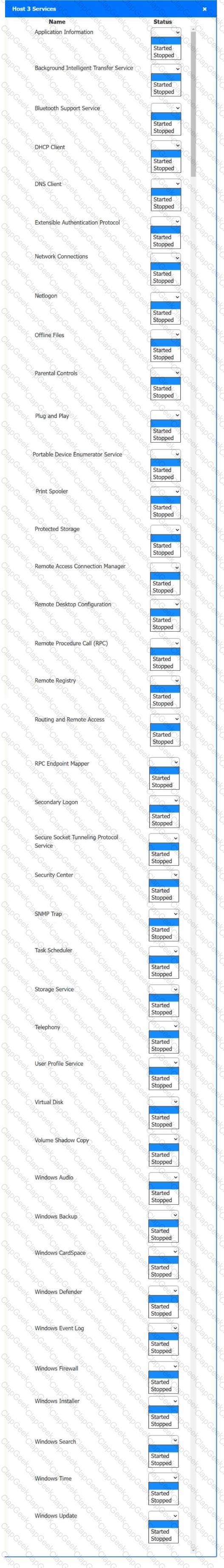
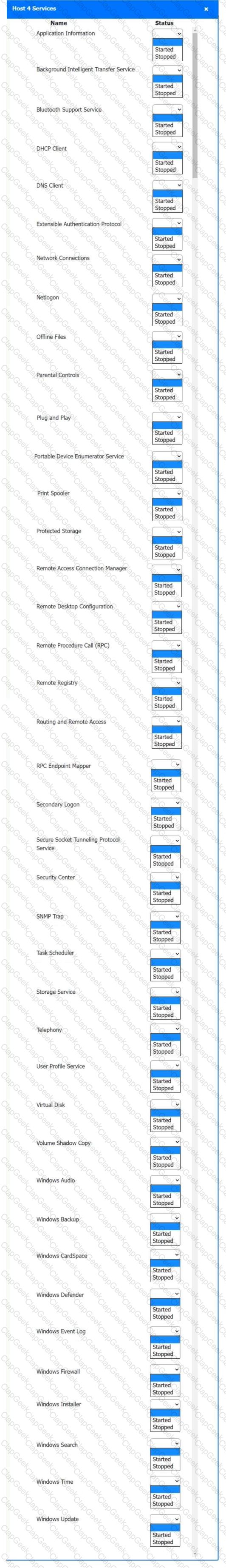
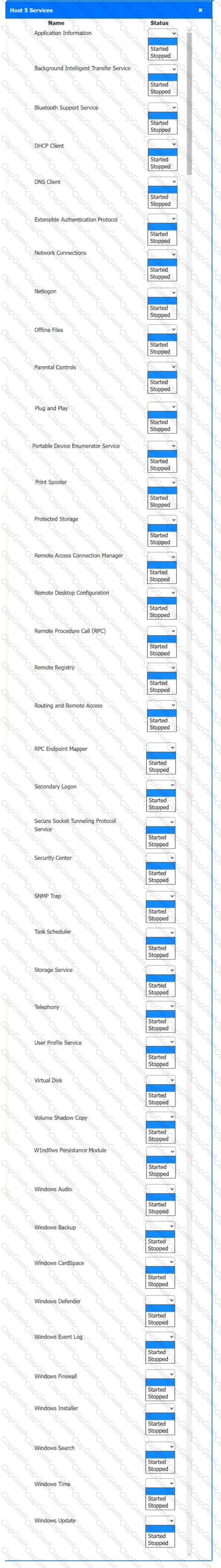
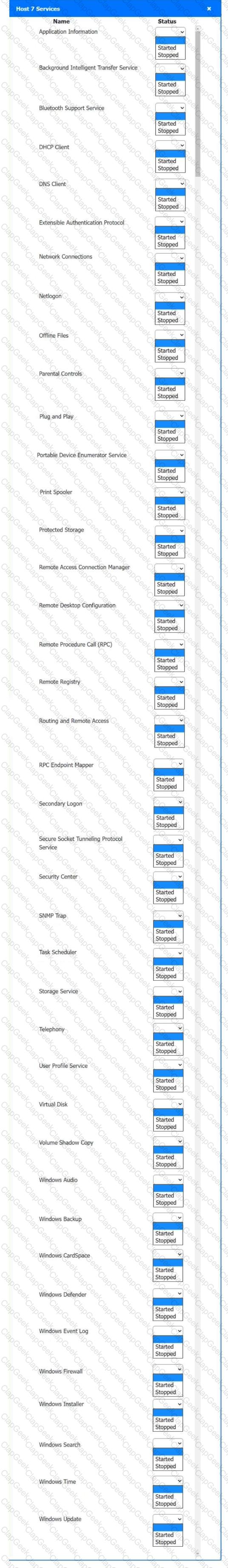
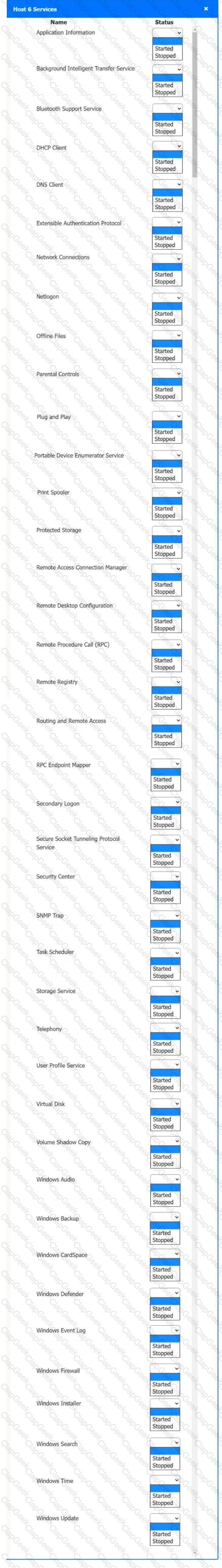
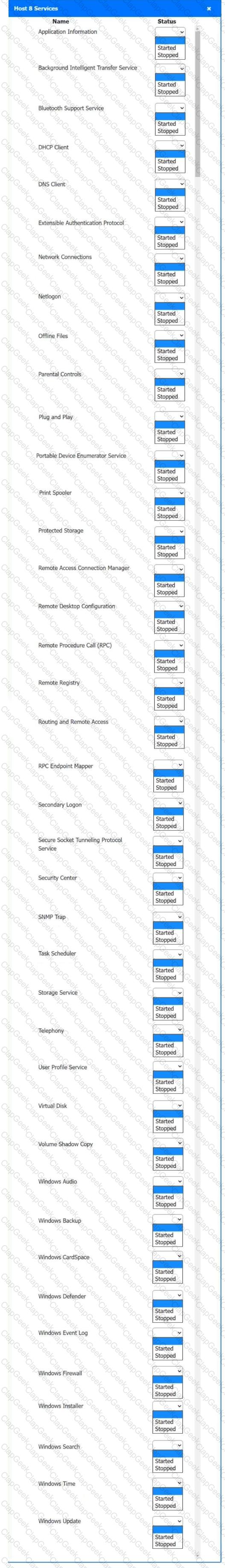
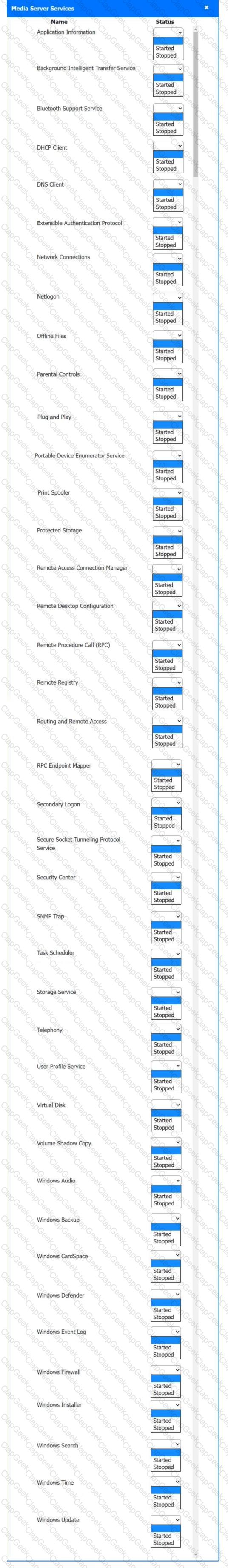
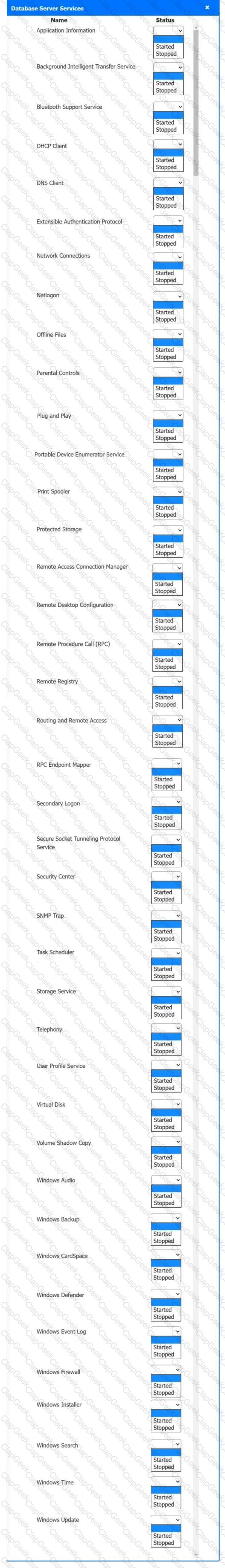
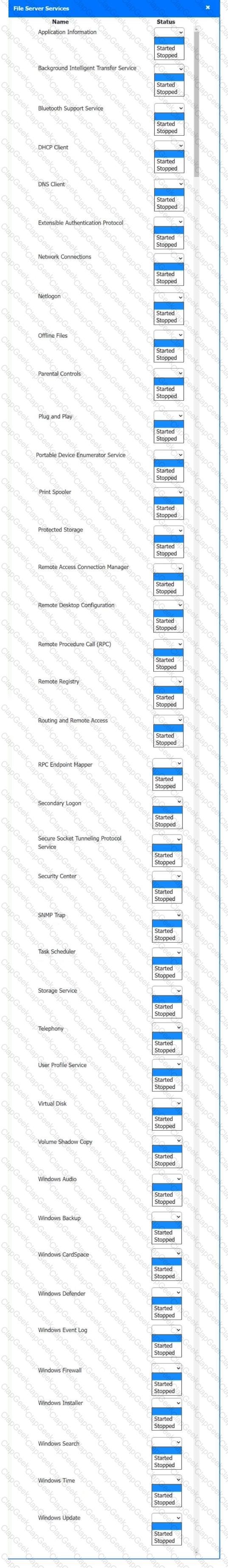
Multiple users are reporting audio issues as well as performance issues after downloading unauthorized software. You have been dispatched to identify and resolve any issues on the network using best practice procedures.
INSTRUCTIONS
Quarantine and configure the appropriate device(s) so that the users’ audio issues are resolved using best practice procedures.
Multiple devices may be selected for quarantine.
Click on a host or server to configure services.
If at any time you would like to bring back the initial state of the simulation, please click the Reset All button.
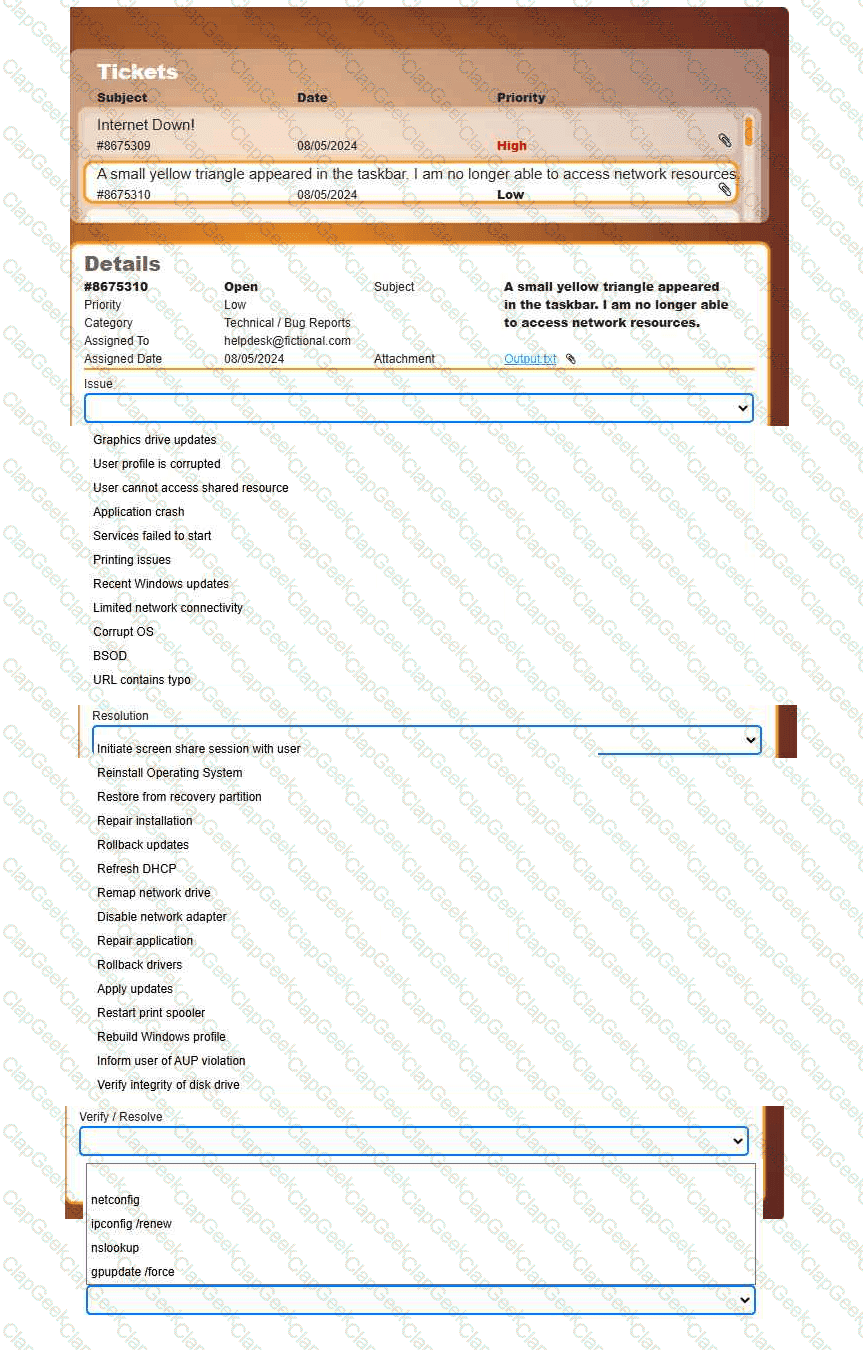
Welcome to your first day as a Fictional Company, LLC helpdesk employee. Please work the tickets in your helpdesk ticket queue.
INSTRUCTIONS
Click on individual tickets to see the ticket details, and view applicable attachments to
determine the problem.
Select the appropriate issue from the ' Issue ' drop-down menu. Then, select the most
efficient resolution from the ' Resolution ' drop-down menu. Finally, select the proper
command or verification to remediate or confirm your fix of the issue from the
' Verify/Resolve ' drop-down menu.
Which of the following is a Linux command that is used for administrative purposes?
A security administrator teaches all of an organization ' s staff members to use BitLocker To Go. Which of the following best describes the reason for this training?
A user reports a critical application issue. The user tells the technician that a former IT employee previously resolved this same issue. Which of the following steps should the technician take first?
A government client asks a technician to expunge several drives that contain confidential information. The technician must follow regulatory compliance. Which of the following is the best option?
Which of the following file types allows macOS users to uninstall software completely by placing the file in the trash?
A user is trying to install 3-D rendering software on a new Windows computer, but the installation fails. An error states that the system does not meet the minimum hardware configuration. Which of the following features should the user check first?
A technician is assigned to offboard a user. Which of the following are common tasks on an offboarding checklist? (Choose two.)
Which of the following types of malware would most likely be detected when observing unusually high CPU usage?
A technician is replacing a rack-mounted UPS. Which of the following should the technician consider?
A technician is reviewing an organization ' s current incident management policy. The organization uses a third-party vendor to protect the organization ' s assets with multiple tools. Which of the following service types is the organization using?
Which of the following methods would make data unrecoverable but allow the drive to be repurposed?
A technician is using a credential manager to safeguard a large number of credentials. Which of the following is important for using this application?
Various alerts on a user ' s Windows 11 laptop are continually interrupting videoconference calls. Which of the following should a support technician recommend to best solve the issue?
A user reports that their computer is running extremely slowly. They are also often redirected to unknown websites when attempting to access internal applications. The computer ' s antivirus software is outdated, and the user cannot access certain security-related settings. A network administrator confirms that all other workstations are operating normally, and network diagnostics show no issues. Which of the following should the administrator do next to troubleshoot these issues?
A user reports getting a BSOD (Blue Screen of Death) error on their computer at least twice a day. Which of the following should the technician use to determine the cause?
The Chief Information Officer (CIO) is overseeing a project to integrate existing business processes to an enterprise resource planning system. The CIO identifies the scope of the change and provides it to the IT department. Which of the following is the first change management procedure to perform before measuring the impact to the systems?
A user cannot upload files to corporate servers from their mobile device when outside the office, but uploads work fine in-office. What should a technician do to determine the root cause?
Which of the following concepts should a technician consider when discussing confidential work projects with individuals outside the company?
A technician is attempting to join a workstation to a domain but is receiving an error message stating the domain cannot be found. However, the technician is able to ping the server and access the internet. Given the following information:
IP Address – 192.168.1.210
Subnet Mask – 255.255.255.0
Gateway – 192.168.1.1
DNS1 – 8.8.8.8
DNS2 – 1.1.1.1
Server – 192.168.1.10
Which of the following should the technician do to fix the issue?
A client reports that their browser ' s home page changed. Every time they run an internet search, the results are returned from unfamiliar websites. Which of the following actions should a technician take first to resolve the issue? (Select two)
A new software installation requires administrative privileges for deployment. Which of the following is the best way to provide the necessary permissions to install the software?
A technician needs to disable guest log-ins on domain-joined desktop machines. Which of the following should the technician use?
A user’s computer is running slowly. Task Manager shows:
Disk: 2%
Network: 12%
GPU: 15%
CPU: 70%
Memory: 97%
Which of the following would a technician most likely do to resolve the issue?
An end user is unable to access the intranet. A technician needs to confirm whether the Windows web server is online and functioning. Which of the following default remote access technologies would the technician most likely use to remotely connect to the server?
The battery on a user’s smartphone discharges quickly during travel. The phone was replaced two weeks ago. What should the technician do first?
A customer calls the help desk to report issues with internet connectivity. The customer is frustrated after speaking with multiple representatives who were unable to resolve the issue. A technician reviews the customer’s file and sees several unresolved tickets. Which of the following actions should the technician take to communicate properly and professionally?
Which of the following must be followed during incident response to ensure the collected evidence is properly handled and accounted for?
Which of the following allows users to prevent malware installation and the disclosure of sensitive information?
An end user ' s computer is unable to start. A technician examines the machine and does not hear any unusual noises but determines that no OS is found. Which of the following is most likely corrupt?
Thousands of compromised machines are attempting to make fake purchases from an online store. Which of the following is taking place?
When a corporate laptop is connected to the company network, it can reach external websites. However, it cannot reach any internal websites, displaying the error message “Cannot reach this page.” Which of the following should a technician configure?
An administrator requires information about a server to identify the product owner and whether it has any business-critical services. Which of the following can the administrator refer to in order to find this information?
An IT technician is attempting to install a video-rendering application for a client when the installation program halts. The technician sees an error message about the system not meeting the VRAM requirement. The system has a popular, integrated video solution and twice the required DRAM. Which of the following should the technician access to meet the VRAM requirement?
A technician needs to disable guest log-ins on domain-joined desktop machines. Which of the following should be used?
A user installed a free application from an unofficial application store. Now, their smartphone displays random pop-ups and shows increased data usage. Additionally, the user cannot perform certain actions such as opening banking applications or updating their OS. Which of the following should the user do first to address the security issues on their smartphone?
A user ' s application only works with a legacy version of the OS. The OS is reaching its end-of-life date. For security reasons, the company is migrating to the current version of the OS. Which of the following is the most efficient way to complete the migration while maintaining accessibility to the application?
A user receives a new personal computer but is unable to run an application. An error displays saying that .NET Framework 3.5 is required and not found. Which of the following actions is the best way to resolve this issue?
A technician is installing a cloud-based productivity suite and gets an error saying the installation is unavailable. What should be tried first?
A company’s Windows 10 devices have been infected with ransomware, and all files are now encrypted. The executives have decided against paying the ransom. Which of the following actions will achieve full operation without any trace of the ransomware?
A user reports some single sign-on errors to a help desk technician. Currently, the user is able to sign in to the company ' s application portal but cannot access a specific SaaS-based tool. Which of the following would the technician most likely suggest as a next step?
An application ' s performance is degrading over time. The application is slowing, but it never gives an error and does not crash. Which of the following tools should a technician use to start troubleshooting?
A technician verifies that a malware incident occurred on some computers in a small office. Which of the following should the technician do next?


