What is an advantage of using Agile over Waterfall methodology in the network design lifecycle?
Organic growth or decline comes from a company ' s normal business activities, rather than through acquisitions or divestment. Changes in usage patterns can also cause organic change in network requirements Which tool is useful when designing and operationalizing a network that is in the process of change?
PaaS provides a cloud-based platform for developing, running, managing applications. Users access the PaaS through a GUI, where development or DevOps teams can collaborate on all their work across the entire application lifecycle including coding, integration, testing, delivery, deployment, and feedback. Which benefit does an organization get by using PaaS?
What are two advantages of the Agile project management methodology? (Choose two)
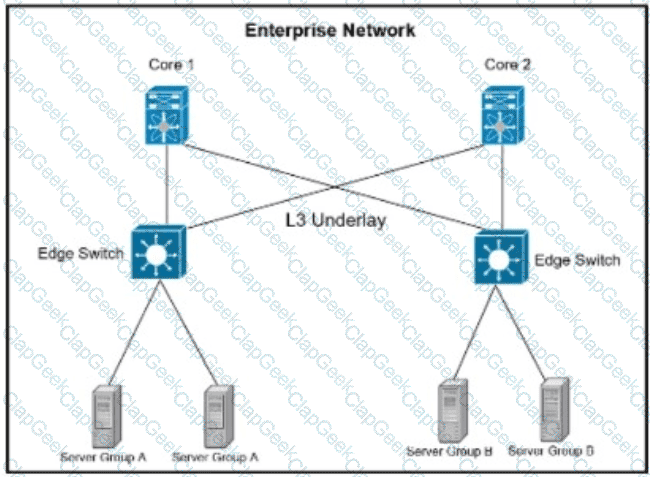
Refer to the exhibit. A company is running their data center based on VXLAN and BGP EVPN with stretched subnets for servers attaching to the edge devices being an important feature. The security team has defined a requirement where server group A must not be able to communicate with each other but is allowed to communicate with server group B. while servers in Group B must be able to communicate with all servers. Which scalable solution can be deployed to support these requirements?
A European government passport agency considers upgrading its IT systems to increase performance and workload flexibility in response to constantly changing requirements. The budget manager wants to reduce capital expenses and IT staff and must adopt the lowest-cost technology. Which technology choice is suitable?
Refer to the table. A customer investigates connectivity options for a DCI between two production data centers. The solution must provide dual 10G connections between locations with no single points of failure for Day 1 operations. It must also include an option to scale for up to 20 resilient connections in the second year to accommodate isolated SAN over IP and isolated, dedicated replication IP circuits. All connectivity methods are duplex 10 Gbps. Which transport technology costs the least over two years, in the scenario?
Company XYZ asks for design recommendations for Layer 2 redundancy. The company wants to prioritize fast convergence and resiliency elements In the design. Which two technologies are recommended? (Choose two.)
Refer to the exhibit. An engineer is designing the network for a multihomed customer running in AS 111 does not have any other Ass connected to it. Which technology is more comprehensive to use in the design to make sure that the AS is not being used as a transit AS?
Which three items do you recommend for control plane hardening of an infrastructure device? (Choose three.)
By monitoring the effects of the design variations, you can characterize the relative resilience of the design. Which method involves disturbing the network by removing an active interface and monitoring how the change is handled by the network?
Over the years, many solutions diveloped to limit control plane state which reduces the scope or the speed of control plane information propagation Which solution removes more specific information about a particular destination as topological distance is covered in the network?
When planning their cloud migration journey what is crucial for virtually all organizations to perform?
In the wake of a security compromise incident where the internal networks were breached by an outside attacker at the perimeter of the infrastructure, an enterprise is now evaluating potential measures that can help protect against the same type of incident in the future. What are two design options that can be employed? (Choose two)
An architect receives a business requirement from a CTO that states the RTO and RPO for a new system should be as close as possible to zero. Which replication method and data center technology should be used?
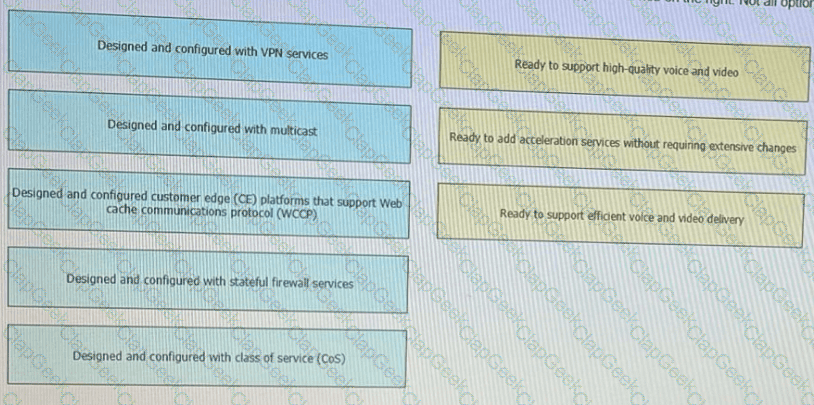
Flexibility, scalability, resiliency, and security are all chrematistics of a services-ready network An architecture featuring a modular design enables technologies and services to be added when the organization is ready to deploy. Drag and drop the design considerations on the left to the to type of service on the right Not all options are used
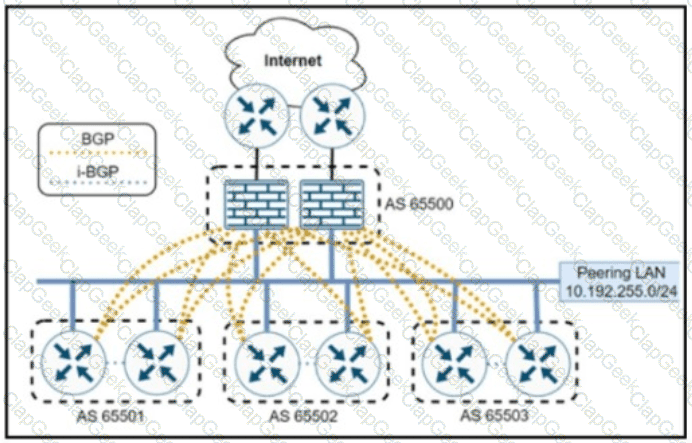
Refer to the exhibit in the topology, each router has a BGP session to each firewall in a hub-and-spoke BGP design The peering LAN implements an Ethernet Virtual Private LAN service from a service provider that offers carrier Ethernet services from its MPLS-enabled network Each router has an IP address in the 10.192 255.0/24 subnet. Spoke BGP routers must communicate with each other directly without traffic passing through the firewall AS PATH is used for policy enforcement.
How can BGP sessions be established between the routers and the firewalls?
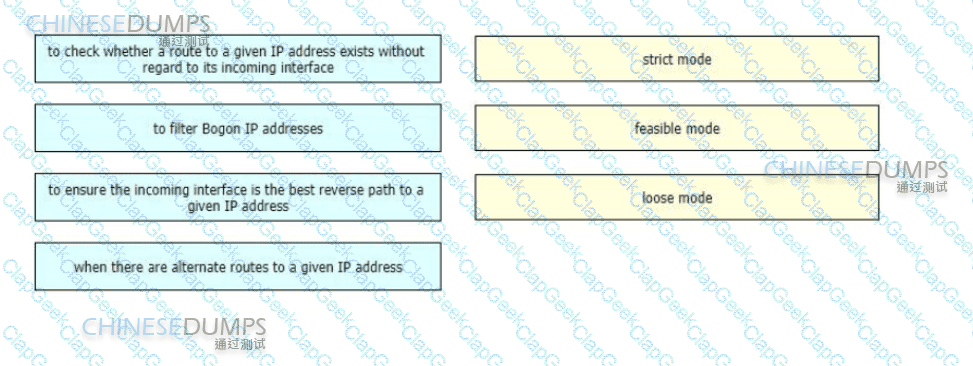
A networking team needs to prevent spoofing attacks They are describing the different uRPF design use cases so they can identify and deploy the optimal mode in various parts of their network
Drag and drop the use cases from the left onto the corresponding uRPF technique on the right Not all options are used
Company XYZ has 30 sites using MPLS L3 VPN and the company is now concerned about data integrity. The company wants to redesign the security aspect of their network based on these requirements:
Securely transfer the corporate data over the private WAN
Use a centralized configuration model.
Minimize overhead on the tunneled traffic.
Which technology can be used in the new design to meet the company’s requirements?
A centralized control plane generally means one or more controllers gather the reachability and topology information from each switching device and calculate some part of the forwarding information at some place. How can a centralized control plane be defined or described?
multinational corporation with offices in various regions worldwide are looking for a network architecture that provides a balance between low- latency and cost-effectiveness for connecting their offices to the cloud. Which cloud connectivity option is the best fit for this corporation?
A network uses an SDN architecture with switches and a centralized controller What should be on the switches but not on the controller?
A lead network architect is tasked with designing the optimal cloud-based solution for a rapidty growing e-commerce company that heavily relies on its online platform for sales and customer interactions The company’s business critical operations induce real time inventory management, order processing, and payment processing The executive team has decided to migrate their infrastructure to the cloud to improve scalability and recoce operational costs Which cloud service model(s) needs to considered?
Refer to the exhibit Which impact of using three or more ABRs between the backbone area and area 1 is true?
The advantages of a hybrid SDN/OSPF control plane are broadly recognized in the networking community, as it promises the best of two worlds: programmability and agility of SDN and the reliability and fault tolerance of OSPF, but there are tradeoffs. Which two challenges of a hybrid SDN control plane exist in an operational network? (Choose two.)
Which three tools are used for ongoing monitoring and maintenance of a voice and video environment? (Choose three.)
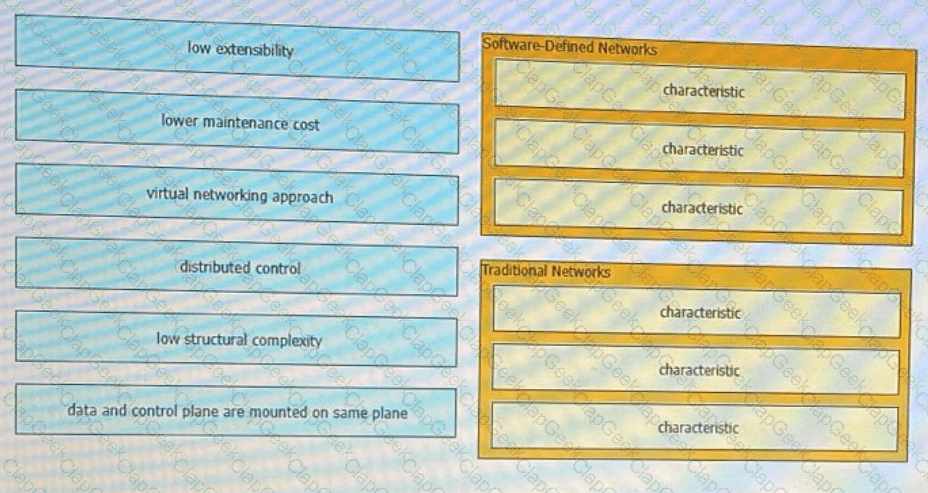
Software-defined network and traditional networks might appear the same to the end-user, but behind the scenes, each has unique sets of characteristics. Drag and drop these characteristic found on the left to the corresponding category on the right in no particular order?
A multinational corporation intends to deploy Al/ML-driven analytics for consumer data The company operates in multiple locations, including the EU, where data protection regulations are rigorous The organization must guarantee that its Al/ML solution adheres to local regulations, especially with data storage and processing
Which cloud environment will most effectively meet the company’s data sovereignty needs while assuring adherence to regional data protection regulations?
Which two advantages of using DWDM over traditional optical networks are true? (Choose two.)
Refer to the exhibit. This network is running legacy STP 802.1 d. Assuming " hello_timer " is fixed to 2 seconds, which parameters can be modified to speed up convergence times after single link/node failure?
Company XYZ is designing the network for IPv6 security and they have these design
requirements:
A switch or router must deny access to traffic from sources with addresses that are correct, but are topologically incorrect
Devices must block Neighbor Discovery Protocol resolution for destination addresses that are not found in the binding table.
Which two IPv4 security features are recommended for this company? (Choose two)
Which component of the SDN architecture automatically ensures that application traffic is routed according to policies established by network administrators?
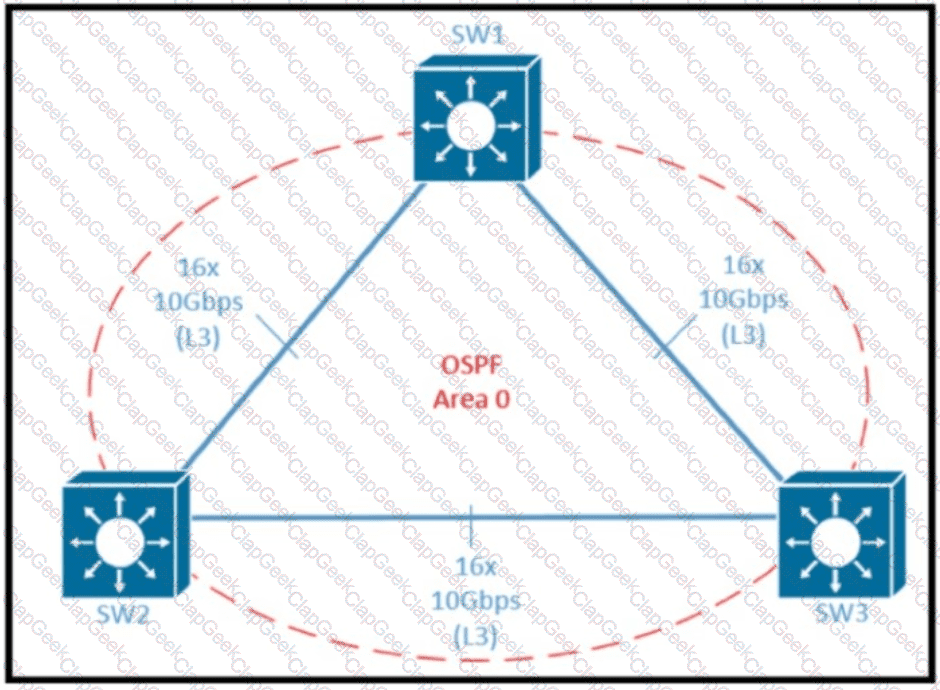
Refer to the exhibit Which two design options reduce the size of OSPF database in the shown topology? (Choose two.)
A multinational enterprise integrates a cloud solution with these objectives
Achieve seamless connectivity across different countries and regions
Extend data center and private clouds into public clouds and provider-hosted clouds
What are two outcomes of deploying data centers and fabrics that interconnect different cloud networks? (Choose two)
A bank recently had their security compromised during an initial key exchange between devices using a symmetric cryptography algorithm, and as a result the key was revealed/leaked. Going forward, they want to ensure that key exchanges are performed using asymmetric cryptography algorithms. Which algorithm offers the desired functionality?
With virtualization being applied in many parts of the network, every physical link is likely to carry one or more virtual links, but what is a drawback in cases like this?
A well-executed network design provides improved performance and efficiency, increased security, and reduced downtime and support costs Which feature helps to achieve resilience in the network?
A company with an existing multivendor network is moving from 1 G dark fiber to an ISP virtual leased-line solution The company ' s internal security policy states that any traffic traversing a network that is not owned by the company must be encrypted What must be used to meet the requirements?
A network architect is working on the baseline policies dealing with the use of Infrastructure-as-Code within an IT department, and has been requested to present the plan at the monthly management board meeting. What are two examples of operational aspects of Infrastructure-as-Code that can be highlighted during the presentation? (Choose two.)
Most security monitoring systems use a signature-based approach to detect threats. In which two instances are systems based on Network Behavior Anomaly Detection better than signature-based systems when it comes to detecting security threat vectors? (Choose two.)
Virtualization pose a special challenges for NAC because virtual servers can move around a data center, and the VLAN can change as the servers move. What is an option that can be used to improve security in this condition?
In a multi-cloud environment, which two practices should be implemented to safeguard the integrity of Al-driven network decisions? (Choose two.)
An engineer is designing a DMVPN network where OSPF has been chosen as the routing protocol A spoke-to-spoke data propagation model must be set up Which two design considerations must be taken into account ? (Choose two)
A large defense organization is planning their cloud migration journey, but they have high data sovereignty concerns, major regulation or compliance requirements, and very restrictive SLAs. Which cloud architecture model can be adopted?
While positive feedback loops generally don ' t last long enough to bring down a network completely, they can still last long enough to disrupt traffic flows or to cause the network to converge more slowly than it should.
What are two examples of cases where a positive feedback loop can be long-lived and devastating to the network ' s control plane? (Choose two)
Which two factors must be considered while calculating the RTO? (Choose two . )
What are the two benefits of using northbound APIs in SDN architecture? (Choose two.)
Company XYZ plans to run OSPF on a DMVPN network They want to use spoke-to-spoke tunnels in the design What is a drawback or concern in this type of design?
which two actions must be taken when assessing an existing wireless network implementation for its readliness to support voice traffic? (choose two)
Two routers R1 and R2 are directly connected through an Ethernet link Both routers are running OSPF. OSPF has been registered with BFD and BFD is running in asynchronous mode with the echo function enabled Which two actions occur that are related to the echo function? (Choose two)
The SD-WAN architecture is composed of separate orchestration management, control, and data planes Which activity happens at the orchestration plane?
An enterprise wants to provide low-cost delivery of network systems that can be scaled on business demand, followed by an initiative to reduce capital expenses for new IT equipment Which technology meets these goals?
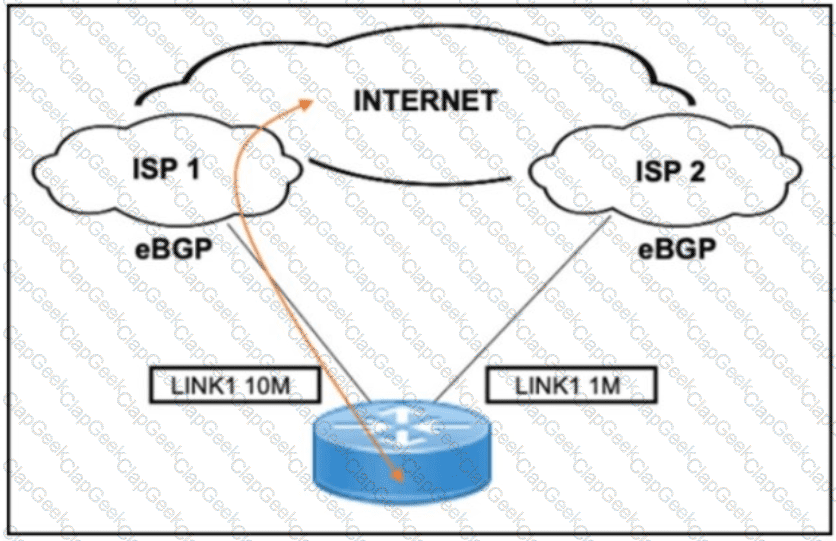
Refer to the exhibit. A customer needs to implement a connectivity model by using one active link for inbound and outbound traffic and a second link for backup. The backup link is low speed and is required only during outages of the primary link. Which design solution should be implemented?
A communication network failure is usually defined as a situation where the network is unable to deliver communication services Thus a failure can be viewed as a disruption of service rather than degradation due to congestion One of the survivability techniques for improving network resilience is traffic management Which network-level traffic management and restoration technique can be used to achieve this?
If the desire is to connect virtual network functions together to accommodate different types of
network service connectivity, what must be deployed?
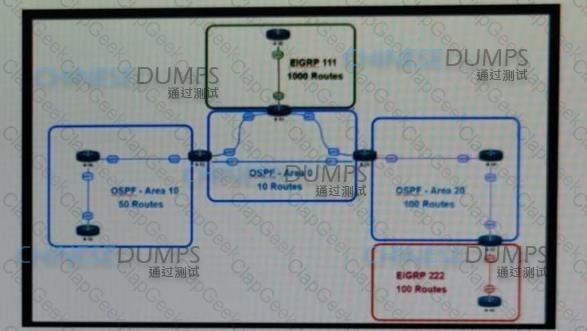
Reter to the exhibit This network is running OSPF and EIGRP as the routing protocols Mutual redistribution of the routing protocols has been contoured on the appropriate ASBRs The OSPF network must be designed so that flapping routes m EIGRP domains do not affect the SPF runs within OSPF The design solution must not affect the way EIGRP routes are propagated into the EIGRP domains Which technique accomplishes the requirement?


