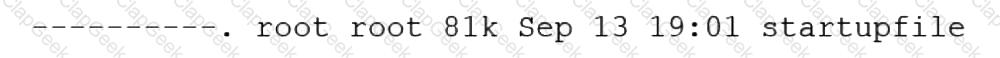
Employees in the finance department are having trouble accessing the file /opt/work/file. All IT employees can read and write the file. Systems administrator reviews the following output:
Which of the following commands would permanently fix the access issue while limiting access to IT and finance department employees?
A Linux administrator needs to analyze a failing application that is running inside a container. Which of the following commands allows the Linux administrator to enter the running container and analyze the logs that are stored inside?
A Linux administrator found many containers in an exited state. Which of the following commands will allow the administrator to clean up the containers in an exited state?
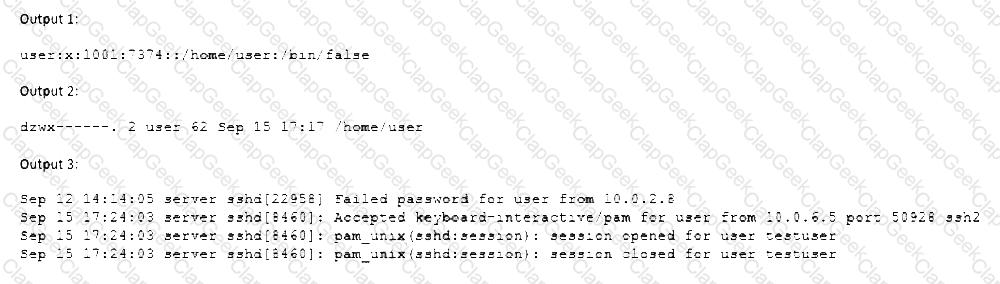
A Linux systems administrator receives reports from various users that an application hosted on a server has stopped responding at similar times for several days in a row. The administrator logs in to the system and obtains the following output:
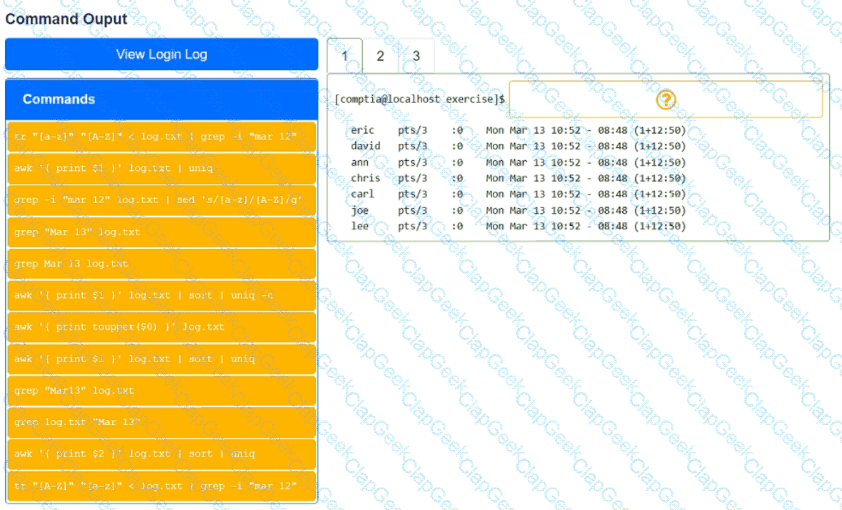
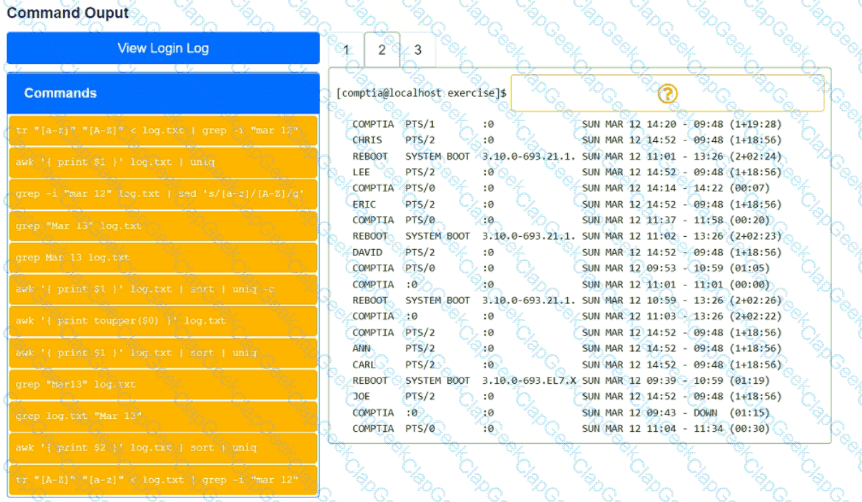
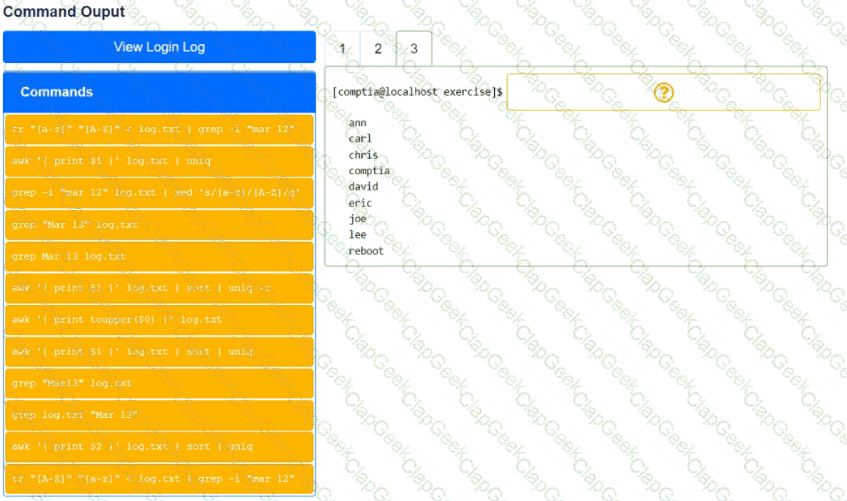
Output 1:
Output 2:
Output 3:
Which of the following should the administrator do to provide the BEST solution for the reported issue?
A senior Linux administrator has created several scripts that will be used to install common system applications. These scripts are published to a reposito-ry to share with the systems team. A junior Linux administrator needs to re-trieve the scripts and make them available on a local workstation. Which of the following Git commands should the junior Linux administrator use to accom-plish this task?
A Linux administrator has set up a new DNS forwarder and is configuring all internal servers to use the new forwarder to look up external DNS requests. The administrator needs to modify the firewall on the server for the DNS forwarder to allow the internal servers to communicate to it and make the changes persistent between server reboots. Which of the following commands should be run on the DNS forwarder server to accomplish this task?
After starting an Apache web server, the administrator receives the following error:
Apr 23 localhost.localdomain httpd 4618] : (98) Address already in use: AH00072: make_sock: could not bind to address [: :]80
Which of the following commands should the administrator use to further trou-bleshoot this issue?
A Linux engineer is removing a previously created firewall rule. Which of the following commands will help the administrator accomplish this task?
A DevOps engineer needs to allow incoming traffic to ports in the range of 4000 to 5000 on a Linux server. Which of the following commands will enforce this rule?
An administrator is trying to diagnose a performance issue and is reviewing the following output:
System Properties:
CPU: 4 vCPU
Memory: 40GB
Disk maximum IOPS: 690
Disk maximum throughput: 44Mbps | 44000Kbps
Based on the above output, which of the following BEST describes the root cause?
An administrator accidentally deleted the /boot/vmlinuz file and must resolve the issue before the server is rebooted. Which of the following commands should the administrator use to identify the correct
version of this file?
A developer reported an incident involving the application configuration file /etc/httpd/conf/httpd.conf that is missing from the server. Which of the following identifies the RPM package that installed the configuration file?
A systems administrator made some changes in the ~/.bashrc file and added an alias command. When the administrator tried to use the alias command, it did not work. Which of the following should be executed FIRST?
A systems administrator has been tasked with disabling the nginx service from the environment to prevent it from being automatically and manually started. Which of the following commands will accomplish this task?
A cloud engineer needs to block the IP address 192.168.10.50 from accessing a Linux server. Which of the following commands will achieve this goal?
A Linux administrator has physically added a new RAID adapter to a system. Which of the following commands should the Linux administrator run to confirm that the device has been recognized? (Select TWO).
A Linux administrator is installing a web server and needs to check whether web traffic has already been allowed through the firewall. Which of the following commands should the administrator use to accomplish this task?
A systems administrator is notified that the mysqld process stopped unexpectedly. The systems administrator issues the following command:
sudo grep –i -r ‘out of memory’ /var/log
The output of the command shows the following:
kernel: Out of memory: Kill process 9112 (mysqld) score 511 or sacrifice child.
Which of the following commands should the systems administrator execute NEXT to troubleshoot this issue? (Select two).
A Linux administrator is troubleshooting a memory-related issue. Based on the output of the commands:
Which of the following commands would address the issue?
A systems administrator requires that all files that are created by the user named web have read-only permissions by the owner. Which of the following commands will satisfy this requirement?
A database administrator requested the installation of a custom database on one of the servers. Which of the following should the Linux administrator configure so the requested packages can be installed?
A cloud engineer needs to check the link status of a network interface named eth1 in a Linux server. Which of the following commands can help to achieve the goal?
A Linux administrator needs to connect securely to a remote server in order to install application software. Which of the following commands would allow this connection?
User1 is a member of the accounting group. Members of this group need to be able to execute but not make changes to a script maintained by User2. The script should not be accessible to other users or groups. Which of the following will give proper access to the script?
A Linux administrator wants to find out whether files from the wget package have been altered since they were installed. Which of the following commands will provide the correct information?
A junior administrator is trying to set up a passwordless SSH connection to one of the servers. The administrator follows the instructions and puts the key in the authorized_key file at the server, but the administrator is still asked to provide a password during the connection.
Given the following output:
Which of the following commands would resolve the issue and allow an SSH connection to be established without a password?
A Linux administrator needs to create a new user named user02. However, user02 must be in a different home directory, which is under /comptia/projects. Which of the following commands will accomplish this task?
Which of the following actions are considered good security practices when hardening a Linux server? (Select two).
A Linux engineer needs to create a custom script, cleanup.sh, to run at boot as part of the system services. Which of the following processes would accomplish this task?
A Linux administrator reviews a set of log output files and needs to identify files that contain any occurrence of the word denied. All log files containing entries in uppercase or lowercase letters should be included in the list. Which of the following commands should the administrator use to accomplish this task?
An administrator recently updated the BIND software package and would like to review the default configuration that shipped with this version. Which of the following files should the administrator review?
A Linux system is failing to boot. The following error is displayed in the serial console:
[[1;33mDEPEND[Om] Dependency failed for /data.
[[1;33mDEPEND[Om] Dependency failed for Local File Systems
...
Welcome to emergency mode! After logging in, type "journalctl -xb" to viewsystem logs, "systemct1 reboot" to reboot, "systemct1 default" to try again to boot into default mode.
Give root password for maintenance
(or type Control-D to continue}
Which of the following files will need to be modified for this server to be able to boot again?
Which of the following can be used as a secure way to access a remote termi-nal?
A Linux system is getting an error indicating the root filesystem is full. Which of the following commands should be used by the systems administrator to resolve this issue? (Choose three.)
A Linux engineer receives reports that files created within a certain group are being modified by users who are not group members. The engineer wants to reconfigure the server so that only file owners and group members can modify new files by default. Which of the following commands would accomplish this task?
A systems administrator is compiling a report containing information about processes that are listening on the network ports of a Linux server. Which of the following commands will allow the administrator to obtain the needed information?
A systems administrator has been unable to terminate a process. Which of the following should the administrator use to forcibly stop the process?
A systems administrator is tasked with setting up key-based SSH authentication. In which of the following locations should the administrator place the public keys for the server?
A Linux administrator modified the SSH configuration file. Which of the following commands should be used to apply the configuration changes?
A systems technician is working on deploying several microservices to various RPM-based systems, some of which could run up to two hours. Which of the following commands will allow the technician to execute those services and continue deploying other microservices within the same terminal section?
A server is experiencing intermittent connection issues. Some connections to the Internet work as intended, but some fail as if there is no connectivity. The systems administrator inspects the server configuration:
Which of the following is MOST likely the cause of the issue?
A systems administrator is encountering performance issues. The administrator runs 3 commands with the following output
The Linux server has the following system properties
CPU: 4 vCPU
Memory: 50GB
Which of the following accurately describes this situation?
A user created the following script file:
# ! /bin/bash
# FILENAME: /home/user/ script . sh
echo "hello world"
exit 1
However, when the user tried to run the script file using the command "script . sh, an error returned indicating permission was denied. Which of the follow-ing should the user execute in
order for the script to run properly?
A Linux engineer needs to download a ZIP file and wants to set the nice of value to -10 for this new process. Which of the following commands will help to accomplish the task?
A developer needs to launch an Nginx image container, name it Web001, and ex-pose port 8080 externally while mapping to port 80 inside the container. Which of the following commands will accomplish this task?
To harden one of the servers, an administrator needs to remove the possibility of remote administrative login via the SSH service. Which of the following should the administrator do?
A systems administrator received a notification that a system is performing slowly. When running the top command, the systems administrator can see the following values:
Which of the following commands will the administrator most likely run NEXT?
A DevOps engineer is working on a local copy of a Git repository. The engineer would like to switch from the main branch to the staging branch but notices the staging branch does not exist. Which of the following Git commands should the engineer use to perform this task?
A Linux systems administrator is setting up a new web server and getting 404 - NOT FOUND errors while trying to access the web server pages from the browser. While working on the diagnosis of this issue, the Linux systems administrator executes the following commands:
Which of the following commands will BEST resolve this issue?
A Linux administrator was tasked with deleting all files and directories with names that are contained in the sobelete.txt file. Which of the following commands will accomplish this task?
A Linux administrator is troubleshooting the root cause of a high CPU load and average.
Which of the following commands will permanently resolve the issue?
A systems administrator is troubleshooting a connectivity issue pertaining to access to a system named db.example.com. The system IP address should be 192.168.20.88. The administrator issues the dig command and receives the following output:
The administrator runs grep db.example.com /etc/hosts and receives the following output:
Given this scenario, which of the following should the administrator do to address this issue?
A systems administrator is checking the system logs. The administrator wants to look at the last 20 lines of a log. Which of the following will execute the command?
A systems administrator is deploying three identical, cloud-based servers. The administrator is using the following code to complete the task:
Which of the following technologies is the administrator using?
Rugged appliances are small appliances with ruggedized hardware and like Quantum Spark appliance they use which operating system?
A systems administrator made some unapproved changes prior to leaving the company. The newly hired administrator has been tasked with revealing the system to a compliant state. Which of the following commands will list and remove the correspondent packages?
Using AD Query, the security gateway connections to the Active Directory Domain Controllers using what protocol?
An administrator is investigating the reason a Linux workstation is not resolving the website http://www.comptia.org. The administrator executes some commands and receives the following output:
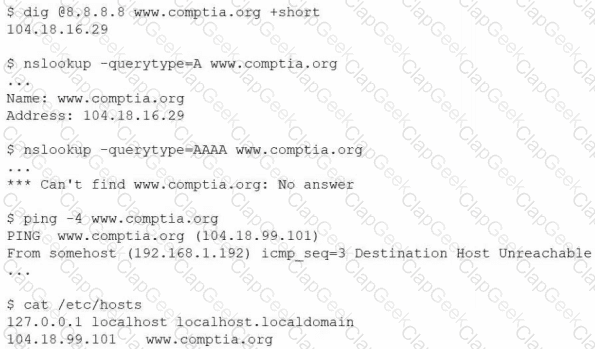
Which of the following is the most likely cause?
A new application container was built with an incorrect version number. Which of the following commands should be used to rename the image to match the correct version 2.1.2?
A systems administrator is installing various software packages using a pack-age manager. Which of the following commands would the administrator use on the Linux server to install the package?
A developer has been unable to remove a particular data folder that a team no longer uses. The developer escalated the issue to the systems administrator. The following output was received:
Which of the following commands can be used to resolve this issue?
NO: 55:
An administrator made a change to a system's network configuration. Which of the following best represents what the administrator should do to have the new configuration take effect?
A Linux administrator needs to run a web application on a server that requires the use of a desktop web browser to enter the final configuration information. The administrator determines the server is running in multi-user mode. The administrator verifies that a web browser is installed on the server and that it has a display manager installed. Which of the following commands will best allow the administrator to temporarily use the web browser on the server?
Users are reporting that a Linux server is responding slowly. A systems administrator troubleshooting the server issue sees the following iostat output, with %iowait at 50.38. Which of the following is most likely the issue?
A Linux administrator is tasked with moving files in a database server. The administrator must not overwrite any existing files. Which of the following commands would indicate that the file already exists?
An administrator is troubleshooting a database service outage that was reported by a monitoring system. Given the following output:
$ systemctl status mariadb
Oct 20 16:40:45 comptia systemd[1]: mariadb.service: Main process exited, code=killed, status=9/KILL
Oct 20 16:40:45 comptia systemd[1]: mariadb.service: Failed with result 'signal'.
Oct 20 16:40:50 comptia systemd[1]: Stopped MariaDB 10.3 database server.
$ dmesg
[ 1061.491433] oom-kill:constraint=CONSTRAINT_NONE,nodemask=(null),cpuset=/,mems_allowed=0,global_oom, task_memcg=/system.slice/mariadb.service, task=mysqld,pid=1981,uid=27
[ 1061.491453] Out of memory: Killed process 1981 (mysqld) total-vm:330668kB, anon-rss:31316kB, file-rss:OkB, shmem-rss:OkB, UID:27 pgtables:324kB oom_score_adj:0
Which of the following is the reason for the outage?
A systems administrator needs to integrate a new storage array into the company's existing storage pool. The administrator wants to ensure that the server is able to detect the new storage array. Which of the following commands should the administrator use to ensure that the new storage array is presented to the systems?
The journald entries have filled a Linux machine's /var volume. Which of the following is the best command for a systems administrator to use to free up the disk space occupied by these entries?
A user (userA) has reported issues while logging in to the system. The following output has been provided:
bash
Could not chdir to home directory /home/userA: Permission denied
-bash: /home/userA/.bash_profile: Permission denied
# cat /etc/passwd | grep userA
userA:x:1234:3400:userA account:/home/userA/:/bin/bash
# passwd -S userA
userA PS 2022-10-17 1 99999 0 (Password set. SHA512 crypt.)
# groups userA
admin dev usergrp
# ls -lth /home/
drwx------ 7 root admin 9 Jan 17 2019 userA
drwxr-xr-x 4 userC app 9 Jan 23 2020 userC
Which of the following describes the issue userA is having?
While troubleshooting server issues, a Linux systems administrator obtains the following output:
[rootGhost ~]# totalfree -m usedfreesharedbuf f/cache available
Mem:373635988824829
Swap:20471824223
Which of the following best describes the state of the system?
After trying to install an RPM package unsuccessfully, a systems administrator verifies the integrity of the package's database. The administrator discovers that the database is corrupted and needs to be recreated. Which of the following commands will help accomplish this task?
A systems administrator configured firewall rules using firewalld. However, after the system is rebooted, the firewall rules are not present:
The systems administrator makes additional checks:
Which of the following is the reason the firewall rules are not active?
Users connecting to a MySQL database on a Linux system report frequent errors. An administrator reviews the following partial output of the /proc/meminfo and free commands:
total used free
Mem: 1011966 151930 860036
Swap: 1191972 1181716 10256
MemTotal: 1011966 kB
MemFree:
SwapTotal: 1191972 kB
SwapFree: 10256 kB
Which of the following should the administrator do to ensure that the MySQL service will continue to run even if the system runs out of swap space? (Select two.)
A junior administrator updated the PostgreSQL service unit file per the data-base administrator's recommendation. The service has been restarted, but changes have not been applied. Which of the following should the administrator run for the changes to take effect?
A junior developer is unable to access an application server and receives the following output:
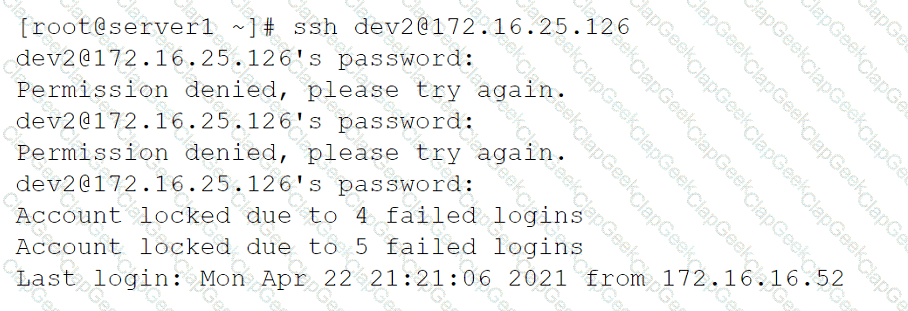
The systems administrator investigates the issue and receives the following output:
Which of the following commands will help unlock the account?
A Linux administrator wants a permission bit on a shared folder that allows only the owner of the file within that directory or the root user to delete or rename the file. Which of the following commands will help achieve this goal?
A systems administrator needs to check the size of the filesystem on the current application servers and ensure that the following filesystems are mounted:
/var
/var/log/audit
/tmp
/home/application
Which of the following commands should the administrator use for these tasks?
When trying to log in remotely to a server, a user receives the following message:
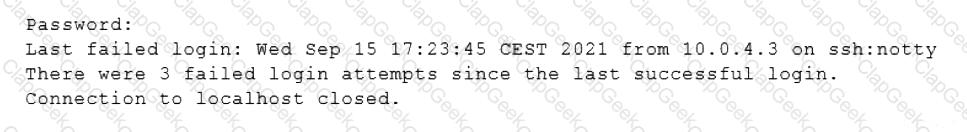
The server administrator is investigating the issue on the server and receives the following outputs:
Which of the following is causing the issue?
An administrator created an initial Git repository and uploaded the first files. The administrator sees the following when listing the repository:
The administrator notices the file . DS STORE should not be included and deletes it from the online repository. Which of the following should the administrator run from the root of the local repository before the next commit to ensure the file is not uploaded again in future commits?
A DevOps engineer is working on a local copy of a Git repository. The engineer would like to switch from the main branch to the staging branch but notices the staging branch does not exist. Which of the following Git commands should the engineer use to perform this task?
A cloud engineer needs to change the secure remote login port from 22 to 49000. Which of the following files should the engineer modify to change the port number to the desired value?
A DevOps engineer wants to allow the same Kubernetes container configurations to be deployed in development, testing, and production environments. A key requirement is that the containers should be configured so that developers do not have to statically configure custom, environment-specific locations. Which of the following should the engineer use to meet this requirement?
An administrator would like to securely connect to a server and forward port 8080 on a local machine to port 80 on the server. Which of the following commands should the administrator use to satisfy both requirements?
A systems administrator installed a new software program on a Linux server. When the systems administrator tries to run the program, the following message appears on the screen.
Which of the following commands will allow the systems administrator to check whether the system supports virtualization?
You have been asked to parse a log file of logins to determine various information about who is logging in and when.
INSTRUCTIONS
Open and inspect the Login log file.
Drag and drop the correct commands onto the output that was generated from that command.
Tokens can be used only once and not all will be used.
If at any time you would like to bring back the initial state of the simulation, please click the Reset All button.
Linux system users report that over the past few months, a server has stopped responding at least twice each day. Every time this happens, the users have to restart the server to recover it. A systems administrator diagnosing the issue collects the following outputs:
csharp
Output 1
[Tue Aug 31 16:36:42 2021] oom-killer invoked by java: gfp_mask=0x280da2 order=0, oom_score_adj=0
[Tue Aug 31 16:36:42 2021] java cpuset=/ mems_allowed=0
Output 2
[root@server]# free -m
total used free shared buff/cache available
Mem: 15819 15026 174 92 619 134
Swap: 0 0 0
Which of the following is the best permanent resolution for the system?
A Linux administrator is configuring a log collector agent to monitor logs in /var/log/collector. The agent is reporting that it cannot write to the directory. The agent runs as the logger user account. The administrator runs a few commands and reviews the following output:
Output 1:
drwxr-xr-x. 1 root root 0 Oct 20:13 collector
Output 2:
file: /var/log/collector
owner: root
group: root
user::rwx
group::r-x
mask::rwx
other::r-x
Output 3:
uid=1010(logger) gid=1010(monitor) groups=1010(monitor)
Which of the following is the best way to resolve the issue?
While troubleshooting server issues, a Linux systems administrator obtains the following output:
yaml
total used free shared buff/cache available
Mem: 3736 3538 33 2 48 25
Swap: 2047 1824 223
Which of the following best describes the state of the system?
Following the migration from a disaster recovery site, a systems administrator wants a server to require a user to change credentials at initial login. Which of the following commands should
be used to ensure the aging attribute?
Several users reported that they were unable to write data to the /oracle1 directory. The following output has been provided:
Which of the following commands should the administrator use to diagnose the issue?
A Linux administrator wants to set the SUID of a file named dev_team.text with 744 access rights. Which of the following commands will achieve this goal?
A Linux administrator needs to remove software from the server. Which of the following RPM options should be used?
A Linux administrator needs to create an image named sda.img from the sda disk and store it in the /tmp directory. Which of the following commands should be used to accomplish this task?
A systems administrator needs to clone the partition /dev/sdc1 to /dev/sdd1. Which of the following commands will accomplish this task?
A systems administrator wants to test the route between IP address 10.0.2.15 and IP address 192.168.1.40. Which of the following commands will accomplish this task?
Which of the following files holds the system configuration for journal when running systemd?
A Linux administrator would like to use systemd to schedule a job to run every two hours. The administrator creates timer and service definitions and restarts the server to load these new configurations. After the restart, the administrator checks the log file and notices that the job is only running daily. Which of the following is MOST likely causing the issue?
A Linux systems administrator needs to persistently enable IPv4 forwarding in one of the Linux systems. Which of the following commands can be used together to accomplish this task? (Choose two.)
A systems administrator needs to validate that the dm_multipath driver was loaded in a Linux system. Which of the following commands should the administrator use?
A user is cleaning up a directory because it has more than 100,000 files that were generated from an experiment. When the user tries to remove the unneeded experiment files, the user receives an error:
arduino
cannot execute [Argument list too long]
Which of the following should the user execute to remove these files?
An administrator logs in to a Linux server and notices the clock is 37 minutes fast. Which of the following commands will fix the issue?
A junior systems administrator recently installed an HBA card in one of the servers that is deployed for a production environment. Which of the following
commands can the administrator use to confirm on which server the card was installed?
An administrator would like to mirror the website files on the primary web server, www1, to the backup web server, www2. Which of the following commands
should the administrator use to most efficiently accomplish this task?
An administrator needs to install an Apache web server on an Ubuntu server. Which of the following commands should the administrator use?
An organization's business office needs to collaborate on quarterly reports and asks the systems administrator to create a finance group. The administrator creates the following directory: drwxrwxr-x Business Business |j096 Oct 15 16:40 Q1
Which of the following commands will allow all members of the finance group to have group ownership of all files created in the Q1 directory while ensuring that members of the business group preserve access? (Select two).
A systems administrator needs to compress log files using the .tar.bz2 format. Which of the following commands should the administrator use?
An administrator started a long-running process in the foreground that needs to continue without interruption. Which of the following keystrokes should the administrator use to continue running the process in the background?
A new drive was recently added to a Linux system. Using the environment and tokens provided, complete the following tasks:
• Create an appropriate device label.
• Format and create an ext4 file system on the new partition.
The current working directory is /.
A Linux user is trying to execute commands with sudo but is receiving the following error:
$ sudo visudo
>>> /etc/sudoers: syntax error near line 28 <<<
sudo: parse error in /etc/sudoers near line 28
sudo: no valid sudoers sources found, quitting
The following output is provided:
# grep root /etc/shadow
root :* LOCK *: 14600 ::::::
Which of the following actions will resolve this issue?
NO: 12:
A network administrator issues the dig www.comptia.org command and receives an NXDOMAIN response. Which of the following files should the administrator check first?
An administrator is unable to sync servers to the new NTP server IP address given by the service provider despite several attempts. Looking at the below output
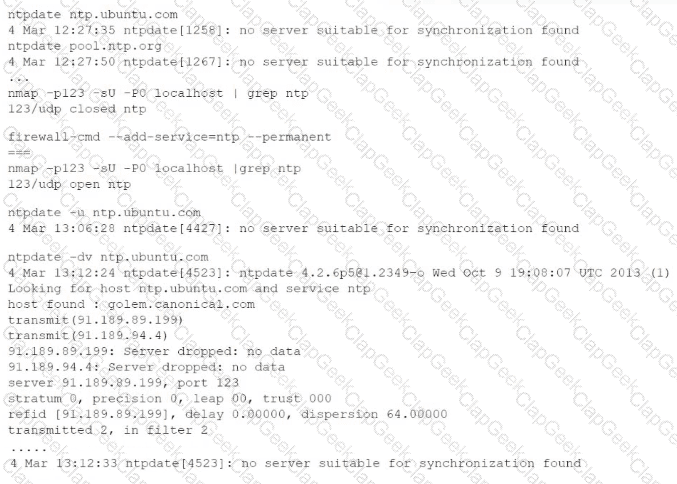
Which of the following commands will help resolve the issue?
A systems administrator identifies multiple processes in a zombie state. Which of the following signals would be best for the administrator to send to the PPID?
An administrator added a new disk to expand the current storage. Which of the following commands should the administrator run first to add the new disk to the LVM?
A Linux administrator intends to start using KVM on a Linux server. Which of the following commands will allow the administrator to load the KVM module as
well as any related dependencies?
A Linux administrator is trying to start the database service on a Linux server but is not able to run it. The administrator executes a few commands and receives the following output:
Which of the following should the administrator run to resolve this issue? (Select two).
Users are experiencing high latency when accessing a web application served by a Linux machine. A systems administrator checks the network interface counters and sees the following:
Which of the following is the most probable cause of the observed latency?
NO: 11:
Users report that they cannot access some files located in the /opt/finapp directory after a power outage caused an unexpected server restart. A Linux administrator examines the following filesystem details and system logs:
# mount | grep finapp
/dev/mapper/rhel-opt_finapp on /opt/finapp type xfs (rw,relatime,seclabel,attr2,inode64,logbufs=8,logbsize=32k,noquota)
# lsblk
NAME MAJ:MIN RM SIZE RO TYPE MOUNTPOINT
sda 8:0 0 931.5G 0 disk
|-sda1 8:1 0 1G 0 part /boot
|-sda2 8:2 0 930.5G 0 part
|-rhel-root 253:0 0 30.5G 0 lvm /
|-rhel-opt_finapp 253:1 0 900G 0 lvm /opt/finapp
# grep opt_finapp /var/log/messages
XFS (opt_finapp): Corruption detected in inode 3645, extent tree
Which of the following commands should the administrator run in an attempt to fix the filesystem?
A Linux administrator needs to replace the content of the test1.sh file with the content of the test2.sh file. Which of the following commands will help accomplish this task?
A Linux administrator receives a ticket stating that end users are unable to access the company’s internal cloud server. The administrator executes the following command:
bash
ping usl.com
Result:
ping: cannot resolve usl.com: Unknown Host
Which of the following files needs to be modified to allow end users to access usl.com?
A Linux administrator is configuring crontab and needs to schedule a task to run only on Saturday and Sunday at 9:00 a.m. every week of the year. Which of the following should the administrator use?
Due to low disk space, a Linux administrator finding and removing all log files that were modified more than 180 days ago. Which of the following commands will accomplish this task?
A Linux administrator created the directory /project/access2all. By creating this directory, the administrator is trying to avoid the deletion or modification of files from non-owners. Which of the following will accomplish this goal?
A systems administrator needs to reconfigure a Linux server to allow persistent IPv4 packet forwarding. Which of the following commands is the correct way to accomplish this task?
An administrator needs to make some changes in the IaC declaration templates. Which of the following commands would maintain version control?
A Linux administrator needs to resolve a service that has failed to start. The administrator runs the following command:
The following output is returned
Which of the following is MOST likely the issue?
Which of the following technologies can be used as a central repository of Linux users and groups?
A Linux administrator is tasked with adding users to the system. However, the administrator wants to ensure the users’ access will be disabled once the project is over. The expiration date should be 2021-09-30. Which of the following commands will accomplish this task?
A Linux administrator is troubleshooting SSH connection issues from one of the workstations.
When users attempt to log in from the workstation to a server with the IP address 104.21.75.76, they receive the following message:
The administrator reviews the information below:
Which of the following is causing the connectivity issue?
A systems engineer is adding a new 1GB XFS filesystem that should be temporarily mounted under /ops/app. Which of the following is the correct list of commands to achieve this goal?
A systems administrator wants to be sure the sudo rules just added to /etc/sudoers are valid. Which of the following commands can be used for this task?
A junior Linux administrator is tasked with installing an application. The installation guide states the application should only be installed in a run level 5 environment.
Which of the following commands would ensure the server is set to runlevel 5?
A cloud engineer is installing packages during VM provisioning. Which of the following should the engineer use to accomplish this task?
A Linux administrator is adding a new configuration file to a Git repository. Which of the following describes the correct order of Git commands to accomplish the task successfully?
Which of the following technologies provides load balancing, encryption, and observability in containerized environments?
A Linux administrator has been tasked with installing the most recent versions of packages on a RPM-based OS. Which of the following commands will accomplish this task?