An administrator creates a new VPC in No NAT mode to allow VMs in a web tier to reach an external firewall. After deployment... none of the VMs can reach external IP addresses... Which action should the administrator take to restore routed north-south connectivity from the VPC?
An administrator is deploying a multi-tier (web, app, database) application on a Nutanix cluster using AHV. The administrator needs to allow internal communication between tiers and provide external access to the web tier. How should the administrator satisfy this requirement?
Which step is required to prepare an AHV cluster for Flow Network Security Next-Gen?
An administrator has deployed a VPC for a multi-tier application on Nutanix AHV. The Web tier requires public internet access, while the App and Database tiers must remain private and isolated. Which steps should the administrator take to configure the external network correctly?
An administrator plans to upgrade the Network Controller in a Flow Virtual Networking deployment. The environment includes multiple AHV clusters managed by Prism Central. Which prerequisite must be verified before upgrading the Network Controller?
An administrator has a requirement to capture application flow data for a policy in Monitor mode and export those events to an external SIEM for correlation with other logs. Which two actions are required to achieve this? (Choose two.)
Exhibit:
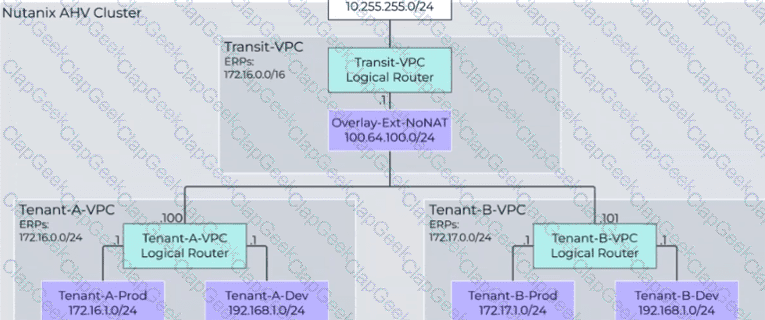
An administrator has just added a new VPC for Tenant-B... However, users are reporting that they are unable to access external resources from VMs created in the Tenant-B-Prod subnet. What should be done to correct the problem?
An administrator manages a four-node cluster Each node has a 4 available 10GB uplinks, and all four are configured as an Active/Active bundle. They want to use Flow Virtual Networking to provide networking to the VMs in the cluster with the following requirements: VMs should be in a single VPC. VMs should be reachable by their real IP addresses. The VPC should have access to the most north/south bandwidth possible. No changes can be made to the physical infrastructure. How can this best be achieved?
An administrator uses Nutanix Flow to secure a three-tier application (Web, App, and Database tiers). After observing the traffic, they find that: The Web tier communicates with the App tier over HTTP (port 80) The App tier communicates with the Database tier over TCP port 1433 The Database tier does not initiate connections The Web tier receives inbound HTTP traffic from the corporate DMZ on port 8080 No other traffic should be allowed What should the administrator do to document and then securely apply these flows in Nutanix Flow?
An administrator needs to delegate the management of security policies to a dedicated SecOps team. To enforce the principle of least privilege, the administrator assigns the predefined Flow Policy Author role to a user on the team. The user confirms they can create, monitor, and enforce security policies. However, when attempting to build a new application security policy for a set of newly deployed VMs, the user reports they are unable to create a new category to group these VMs. The option is not available in the Prism Central UI. Which statement explains this behavior?
Which two statements are true with respect to Flow Network Security Policies? (Choose two.)
A new multi-tier application is being deployed across several subnets in a Nutanix environment. The security team wants to create a Flow Network Security Policy to restrict traffic between the tiers, but the complete matrix of required network ports and protocols is not fully documented. Which strategy should the team employ first to accurately capture the necessary communication patterns without risking application outage?
An administrator has two user VPCs connected via a Transit VPC. Routing works for most subnets, but one overlay subnet cannot reach external networks. What is the most probable cause?
Which policy mode blocks all traffic that is not explicitly allowed by the policy?
An administrator configures a VPN gateway with eBGP for dynamic route exchange. After setup, routes are not advertised to the remote peer. Which configuration is most likely missing?
When creating a VPC, enabling the Transit VPC toggle changes the role of the VPC. What does the Transit VPC toggle do?
Refer to Exhibit:
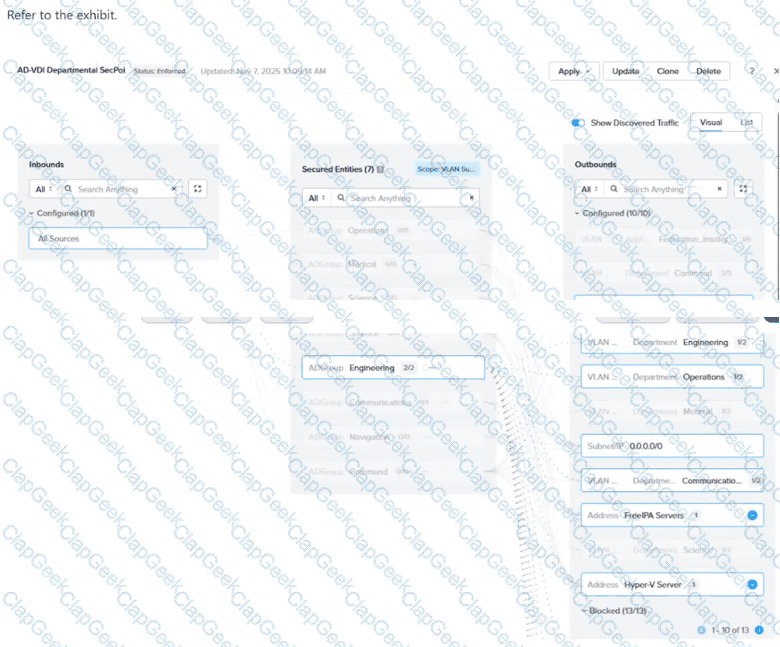
In the AD-VDI Departmental SecPol policy shown in the exhibit, ADGroup: Engineering is configured as a secured entity in a VDI Security Policy. Prism Central shows 2 / 2 active sessions under this group, but the administrator confirms that three Engineering users are currently logged in to persistent VDI desktops. The third user's VM shows no ADGroup assignment in its VM details in Prism Central, even after the user has successfully logged in. All three users are members of the same AD group, and the Domain Controller event logs confirm a successful interactive login for the third user. Which condition explains why the third user's VM is not being assigned the ADGroup: Engineering category?
Refer to Exhibit:
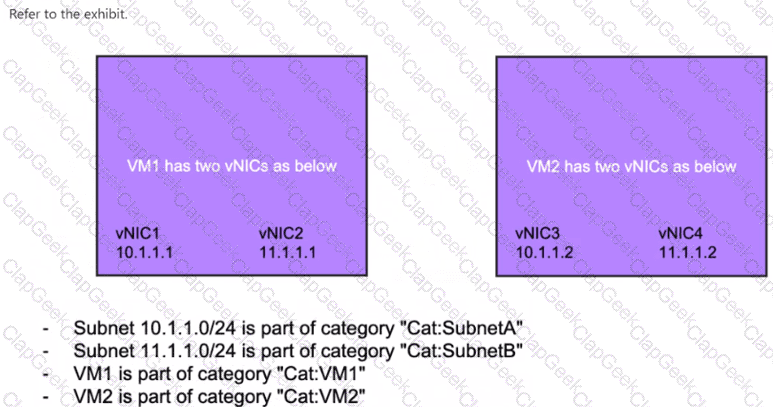
How should an Application Policy be created whose rules apply only to vNIC1 of VM1?
What entity is automatically created on the cluster hosting Prism Central when Microsegmentation is enabled?
An administrator has a VPC with multiple overlay subnets and a VPN gateway configured for site-to-site connectivity. During testing, the administrator noticed fragmented packets and poor performance. Which configuration change resolves this issue without disabling VPN?
An administrator needs to use Prism Central to identify a subnet belonging to a VPC. How can the administrator identify networks associated with a VPC within Prism Central?
An administrator has a VPC with a single active gateway node that successfully peers with an external router using a single BGP GW and session. To eliminate a single point of failure, the administrator deploys a second BGP gateway to the VPC. After the second gateway is added and shows a healthy state, the external router still only sees a single BGP session. What is the most likely reason for the second session not being established on the external router?
Which statement best describes the function of an External Network in Flow Virtual Networking?
An organization plans to apply security controls based on user group membership in Active Directory. What configuration is required in Prism Central before VDI policies can be used?
During a security review, the administrator confirms that the existing security policy does not explicitly allow traffic from Environment: Development to Environment: Production. A VM in the Development category was still able to reach a Production VM over IPv6. What is the most likely cause of this behavior?
An administrator has been tasked with upgrading the Nutanix cluster to a newer version of AOS. The cluster is running a mix of different versions across nodes... What is the recommended first step when upgrading a Nutanix cluster with different AOS versions across nodes?


