What must the maximum Round Trip Latency be less than between a Witness VM and Metro Availability PDs?
Two AHV clusters are 4 ms RTT apart. The business requires:
0 RPO
Automatic failover
No application performance degradation
Hybrid HCI nodes with 100 TB capacity
What storage configuration must be validated before enabling synchronous replication?
Recently, several new VMs were deployed as part of an application expansion. Within 24 hours, the administrator notices no recovery points are being created for the new VMs.
During investigation, the administrator observes:
Existing VMs in the Protection Policy continue to replicate successfully.
No replication task failures are reported.
Network connectivity between clusters is healthy.
Storage capacity at the remote site is sufficient.
The Protection Policy uses category-based entity selection.
The newly deployed VMs were provisioned by a separate team.
What is the most likely root cause of the issue?
An administrator performs these steps while configuring Nutanix Disaster Recovery:
Create VMs on Site A in a container named SalesA
Create a new container on Site B named SalesB
Create new Protection Policy name Async
Place all the new Sales VMs in the Protection Policy named Async
Set a schedule to begin taking hourly snapshots immediately
After performing the steps, replications begin without any errors. After two hours, the administrator checks on the progress on the remote site and finds that the SalesB container is showing 0 bytes.
What went wrong?
An administrator configures disaster recovery between an on-premises AZ and a Nutanix Cloud AZ. After enabling DR and assigning protection policies to several VMs with volume groups, the administrator initiates failover and notices the VMs do not have their volume groups attached. Investigation reveals:
The clusters are successfully paired in Prism Central.
Protection policies and replication schedules are configured correctly.
Recovery plan validation completes successfully.
Required firewall ports between sites are confirmed open.
Management IP addresses are reachable in both directions.
Despite this, the administrator observes the volume groups are still not attached. Which network-related prerequisite is most likely misconfigured?
An administrator migrates a guest VM from a legacy Protection Domain–based DR configuration to a Prism Central (PC)–based Protection Policy. Immediately after migration, the administrator considers deleting the legacy Protection Domain snapshots to reclaim storage. According to Nutanix guidance, when is it safe to delete the legacy Protection Domain snapshots?
An administrator plans to configure Cross Hypervisor Disaster Recovery (CHDR) to replicate VMs from an ESXi cluster to an AHV cluster using an Asynchronous replication schedule. Which component must be installed on the VMs to ensure successful migration and driver configuration during recovery?
An administrator notices that VM replication from ClusterA to ClusterB fails consistently at the same point during the replication job. The following observations are noted by the administrator:
The Prism dashboard shows the replication job failing during snapshot creation.
ClusterB storage pool and container usage is under 80%, well below capacity.
Network latency/Pings between ClusterA and ClusterB averages 3ms, with occasional spikes to 25ms.
VM event logs indicate frequent I/O timeout errors during the replication window.
Both clusters are running compatible AOS versions.
What is the most likely cause for the failing replications?
An administrator is preparing to configure DR between an on-prem AZ and Nutanix Cloud AZ. Replication fails immediately after configuration. Which prerequisite should be verified?
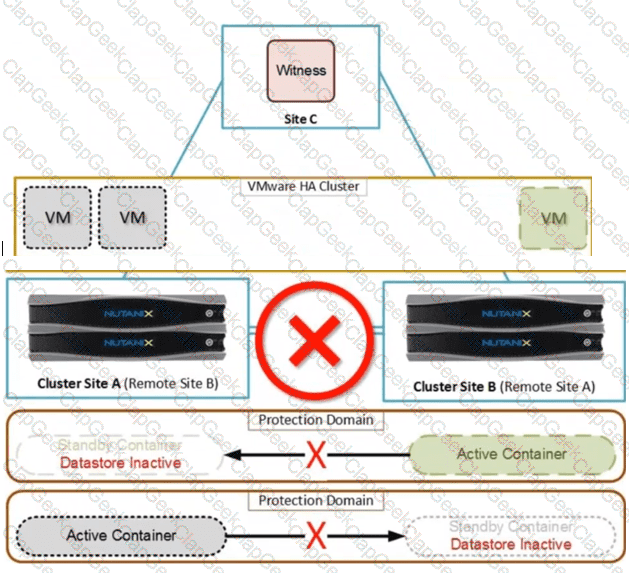
Exhibit:
An administrator wants to protect the snapshots created on the cluster. Only authorized users should be allowed to modify or delete the snapshots on the cluster. How can the administrator harden the security of the snapshots?
An administrator is creating a recovery plan between two availability zones. The production VMs use a subnet that does not exist at the recovery AZ. To ensure the VMs can successfully connect after a failover, what must be configured?
An administrator plans on performing a failover of a VM from a source cluster to a DR cluster. The administrator needs the VM ' s IP address preserved after failover. In what scenario is the VM ' s IP address preserved?
What is the bandwidth limit of a single Nutanix Cloud Gateway for IPSec traffic?
An administrator managing critical VMs has been tasked with designing a Disaster Recovery solution where the VMs are brought up on the target cluster if the source cluster experience any issues. The failover needs to be triggered without any user intervention and with minimal downtime. What automatic failure execution solution is best suited?
An administrator initiates an unplanned failover due to a primary AZ outage. What is the worst-case scenario for data loss and which recovery point will be used by default?
An administrator configures a VM-VM Anti-Affinity policy for a web application cluster to ensure high availability. The application is protected by a Protection Policy in Prism Central. A failover occurs, moving the VMs to the recovery site.
What determines whether the VM-VM Anti-Affinity rules are active on the recovery site?
An administrator executes a Recovery Plan for a set of high-performance VMs configured with SR-IOV network adapters. The VMs failover successfully to the Recovery Cluster.
What is the state of these VMs immediately after the planned failover completes?
While attempting to execute a Commvault backup plan, an administrator received the following error for several VMs: " Virtual Machine not found " . After confirming the VMs exist, the administrator finds the following related error message: " Event Code 91:4 Virtual machine [Nutanix-Web-Server] was not found. Please verify that the virtual machine still exists and that the host is in the connected state. " Which action should the administrator take to enable successful backups?
When designing a Disaster Recovery strategy to an NC2 cluster using MST, which technical limitation impacts the Recovery Plan and workload compatibility?
Which two Data Protection technologies are compatible with Self-Service Restore? (Choose two.)
A financial institution is designing a disaster recovery solution for a business-critical application that requires a zero recovery point objective (RPO). The infrastructure team decides to implement Nutanix Metro Availability between two physical data centers (DC-Alpha and DC-Beta) interconnected by a dedicated dark fiber. What is the maximum possible network latency on this link for this configuration to function correctly?
Which native Nutanix tool is used to determine connectivity between two sites during disaster recovery testing?
An organization requires strict control over data destruction. An administrator configures an Approval Policy for DR snapshots to prevent accidental deletion. A user attempts to delete a recovery point protected by this policy. What is the immediate outcome of this deletion attempt within the Prism Central interface?
An administrator recently expanded a Nutanix cluster by adding several new nodes. Shortly after, multiple backup jobs began failing. The following error is consistently reported: " Failed to perform backup: Cannot complete process ' iscsiadm --mode discovery --type sendtargets --portal X.X.X.X ' within timeout " . What is the most likely cause of the failure?
An administrator performed an unplanned failover from AZ1 (primary) to AZ2 (recovery). Later, AZ1 is restored and the administrator wants to fail back the entities to AZ1. Which two statements are correct? (Choose two.)
An administrator intends to configure a NearSync replication schedule with a 15-minute Recovery Point Objective (RPO) on a hybrid 3-node cluster. The current nodes in the cluster are configured with one SSD and four HDDs each. Which cost-effective modification is required to support this specific replication schedule?
An administrator wants to protect the snapshots created on the cluster. Only authorized users should be allowed to modify or delete the snapshots on the cluster. How can the administrator harden the security of the snapshots?
An administrator enables network segmentation for Disaster Recovery on a primary cluster to isolate replication traffic. The primary and recovery clusters are in a " brownfield " configuration, meaning the recovery cluster does not yet have network segmentation enabled.
How is the configuration of the recovery cluster handled in this scenario?
How does the system behave if the network cannot sustain the data change rate required to maintain a 1-minute RPO between the primary and recovery AZs?


