You need to protect the U.S. PII data to meet the technical requirements.
What should you create?
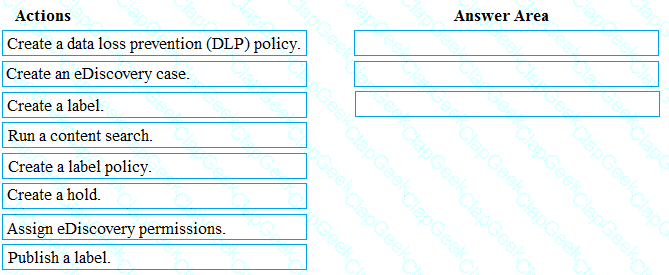
You need to meet the requirement for the legal department.
Which three actions should you perform in sequence from the Security & Compliance admin center? To answer, move the appropriate actions from the list of actions to the answer area and arrange them in the correct order.
You need to recommend a solution for the security administrator. The solution must meet the technical requirements.
What should you include in the recommendation?
You need to meet the technical requirement for the SharePoint administrator. What should you do? To answer, select the appropriate options in the answer area. NOTE: Each correct selection is worth one point.
You need to meet the technical requirement for the EU PII data.
What should you create?
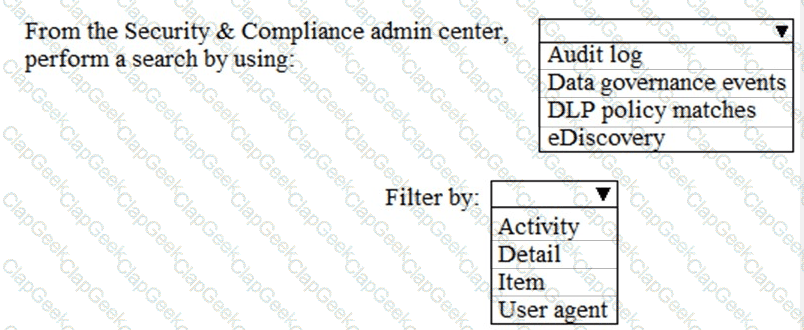
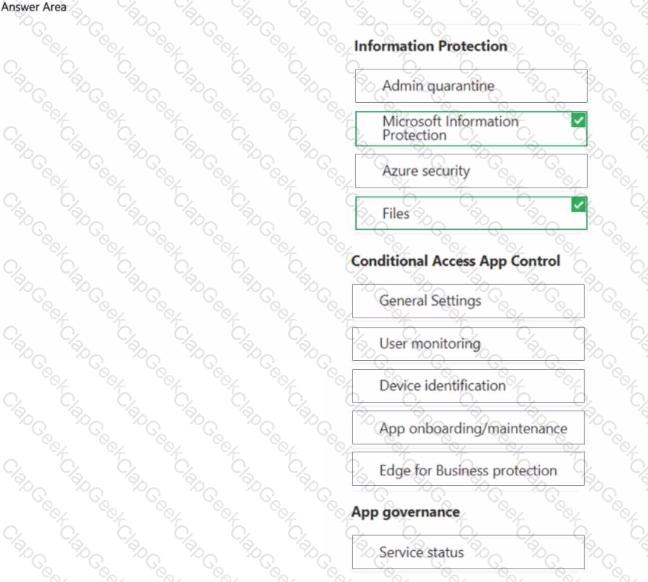
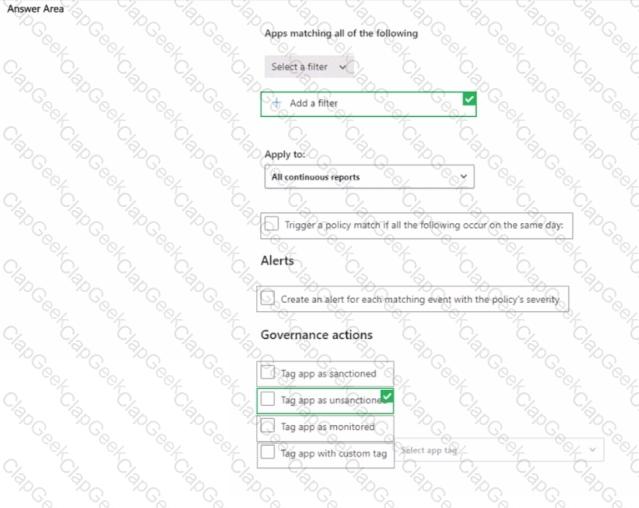
You have a Microsoft 365 E5 subscription and use Microsoft Defender for Cloud Apps. You need to create a file policy named Policy1 that meets the following requirements:
• Inspects files in connected software as a service (SaaS) apps
* Inspects protected files
Which two settings should you configure? To answer, select the appropriate settings in the answer area. NOTE: Each correct selection is worth one point.
You have a Microsoft 365 E5 subscription.
From the Microsoft 365 Defender portal, you plan to export a detailed report of compromised users.
What is the longest time range that can be included in the report?
You have a Microsoft 365 subscription.
You integrate Microsoft Defender for Cloud Apps with Microsoft Defender for Endpoint.
You need to create a policy to block users from accessing discovered apps that have a risk score of 4 or lower.
Which two settings should you configure? To answer, select the appropriate settings in the answer area.
NOTE: Each correct selection is worth one point.
You have a Microsoft 365 E5 tenant.
You need to evaluate compliance with European Union privacy regulations for customer data.
What should you do in the Microsoft 365 compliance center?
You have a Microsoft 365 subscription.
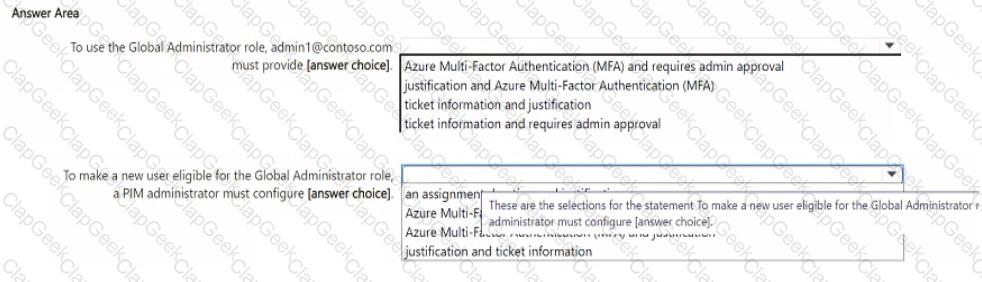
From Microsoft Entra Privileged Identity Management (PIM), you configure Role settings for the Global Administrator role as shown in the following exhibit.
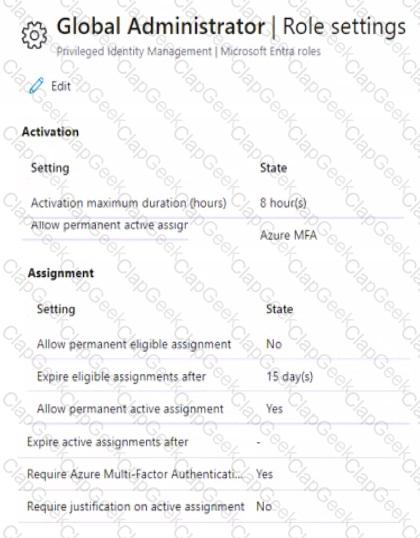
You make a user named admin1@contoso.com eligible for the Global Administrator role.
Use the drop-down menus to select the answer choice that completes each statement based on the information presented in the
You have a Microsoft 365 subscription.
All uses are assigned Microsoft 365 Apps for enterprise licenses.
You need to ensure that reports display the names of users that have activated Microsoft 365 apps and on how many devices. What should you modify in the Microsoft 365 admin center?
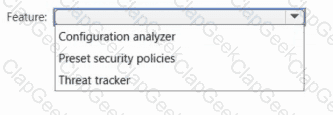
You have a Microsoft 365 subscription that uses Microsoft Defender for Office 365.
You need to identify the settings that are configured less secure than the Standard protection profile settings in the preset security policies.
What should you use? To answer, select the appropriate options in the answer area.
NOTE: Each correct selection is worth one point.
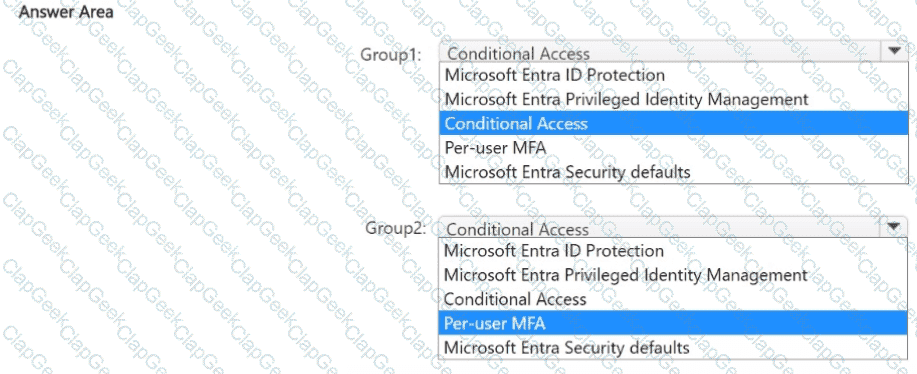
You have a Microsoft 365 E5 subscription that contains two security groups named Group1 and Group2.
You need to enable multi-factor authentication (MFA) for the members of Group1 and Group2. The solution must meet the following requirements:
• The Group1 members must be prompted for MFA only when authenticating to Microsoft Entra ID from Android devices.
• The Group2 members must be prompted for MFA only when accessing Microsoft Exchange Online from outside the corporate network.
• Administrative effort must be minimized.
What should you configure for each group? To answer, select the appropriate options in the answer area.
NOTE: Each correct selection is worth one point.
: 223
Your company has digitally signed applications.
You need to ensure that Microsoft Defender Advanced Threat Protection (Microsoft Defender ATP) considers the digitally signed applications safe and never analyzes them.
What should you create in the Microsoft Defender Security Center?
You have a Microsoft 365 subscription that uses Microsoft 365 Defender.
You need to compare your company ' s security configurations to Microsoft best practices and review improvement actions to increase the security posture.
What should you use?
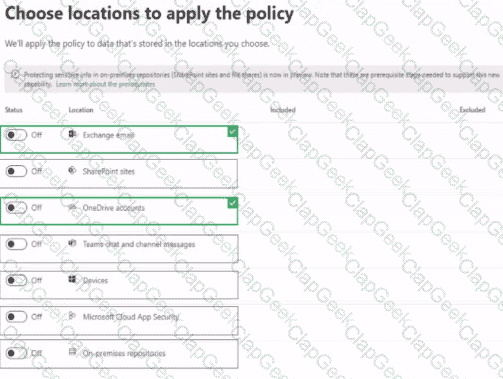
You have a Microsoft 365 E5 tenant
You create a data toss prevention (DLP) policy to prevent users from using Microsoft Teams to share internal documents with external users.
To which two locations should you apply the policy? To answer, select the appropriate locations in the answer area.
NOTE: Each correct selection is worth one point.
You have a Microsoft 365 E5 tenant that contains the devices shown in the following table.
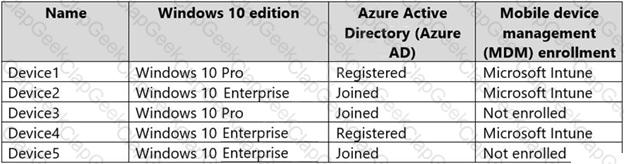
You add custom apps to the private store in Microsoft Store Business.
You plan to create a policy to show only the private store in Microsoft Store for Business.
To which devices can the policy be applied?
You have a Microsoft 365 E5 subscription.
You plan to create an anti-malware policy named Policy1.
You need to ensure that Policy1 can detect malicious email messages that were already delivered to a user ' s mailbox.
What should you do in the Microsoft Defender portal?
You have a Microsoft 365 E5 subscription. The subscription contains users that have the following types of devices:
• Windows 11
• Android
• iOS
To which devices can you apply Endpoint DLP policies?
: 235
You have a Microsoft 365 tenant that is signed up for Microsoft Store for Business and contains a user named User1. You need to ensure that User1 can perform the following tasks in Microsoft Store for Business:
• Assign licenses to users.
• Procure apps from Microsoft Store.
• Manage private store availability for all items.
The solution must use the principle of least privilege.
Which Microsoft Store for Business role should you assign to User1?
Note: This section contains one or more sets of questions with the same scenario and problem. Each question presents a unique solution to the problem. You must determine whether the solution meets the stated goals. More than one solution in the set might solve the problem. It is also possible that none of the solutions in the set solve the problem.
After you answer a question in this section, you will NOT be able to return. As a result, these questions do not appear on the Review Screen.
You have a Microsoft 365 E5 subscription and use Microsoft Defender for Office 365.
You need to implement a threat policy that will apply a balanced baseline protection profile to protect against spam, phishing, and malware.
Solution: You create an anti-phishing policy.
Does this meet the goal?
You plan to use Azure Sentinel and Microsoft Cloud App Security. You need to connect Cloud App Security to Azure Sentinel.
What should you do in the Cloud App Security admin center?
You are reviewing alerts in the Microsoft 365 Defender portal.
How long are the alerts retained in the portal?
You have a Microsoft 365 E5 tenant.
The Microsoft Secure Score for the tenant is shown in the following exhibit.
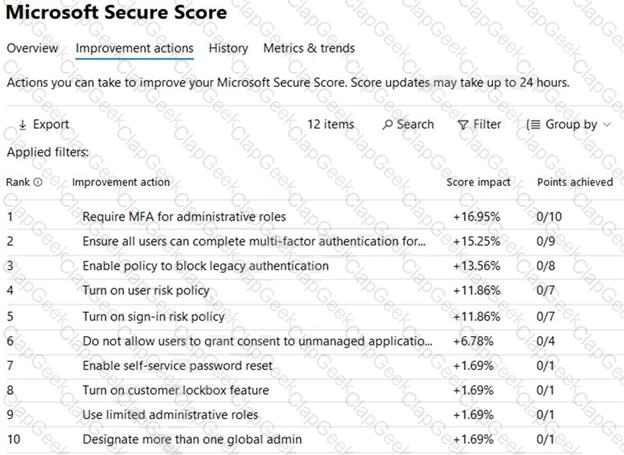
You plan to enable Security defaults for Azure Active Directory (Azure AD).
Which three improvement actions will this affect?
Your network contains an Active Directory forest named Contoso. Local.
You have a Microsoft 365 subscription.
You plan to implement a directory synchronization solution that will use password hash synchronization.
From the Microsoft 365 admin center, you successfully verify the contoso.com domain name.
You need to prepare the environment for the planned directory synchronization solution.
What should you do first?
Your network contains an on-premises Active Directory domain named contoso.com. The domain contains 1,000 Windows 10 devices.
You perform a proof of concept (PoC) deployment of Microsoft Defender for Endpoint for 10 test devices. During the onboarding process, you configure Microsoft Defender for Endpoint-related data to be stored in the United States.
You plan to onboard all the devices to Microsoft Defender for Endpoint.
You need to store the Microsoft Defender for Endpoint data in Europe.
What should you do first?
Note: This question is part of a series of questions that present the same scenario. Each question in the series contains a unique solution that might meet the stated goals. Some question sets might have more than one correct solution, while others might not have a correct solution.
After you answer a question in this section, you will NOT be able to return to it. As a result, these questions will not appear in the review screen.
Your network contains an on-premises Active Directory domain. The domain contains domain controllers that run Windows Server 2019. The functional level of the forest and the domain is Windows Server 2012 R2.
The domain contains 100 computers that run Windows 10 and a member server named Server1 that runs Windows Server 2012 R2.
You plan to use Server1 to manage the domain and to configure Windows 10 Group Policy settings.
You install the Group Policy Management Console (GPMC) on Server1.
You need to configure the Windows Update for Business Group Policy settings on Server1.
Solution: You upgrade Server1 to Windows Server 2019.
Does this meet the goal?
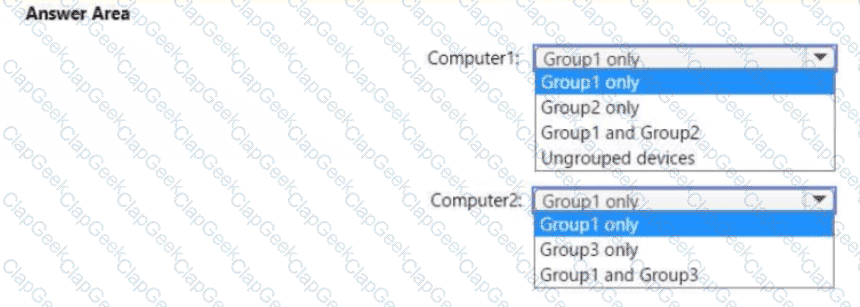
Your company uses Microsoft Defender for Endpoint. Microsoft Defender for Endpoint contains the device groups shown in the following table.
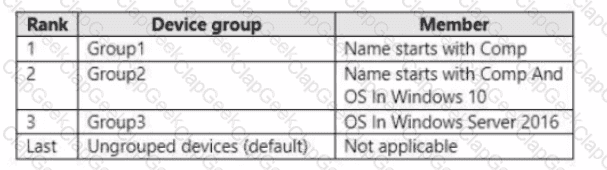
You onboard computers to Microsoft Defender for Endpoint as shown in the following table.
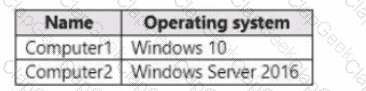
Of which groups are Computer! and Computed members? To answer, select the appropriate options in The answer area.
NOTE: Each correct selection is worth one point.
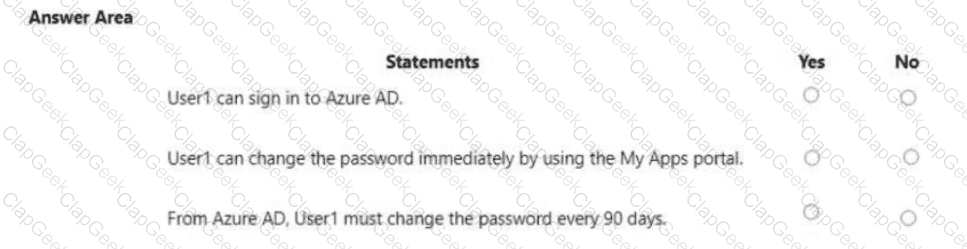
Your network contains an on-premises Active Directory domain named adatum.com that syncs to Azure AD by using the Azure AD Connect Express Settings. Password write back is disabled.
You create a user named User1 and enter Pass in the Password field as shown in the following exhibit.
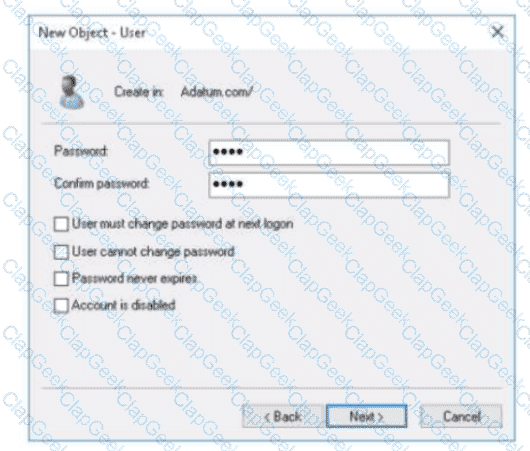
The Azure AD password policy is configured as shown in the following exhibit.
Password policy
Set the password policy for all users in your organization.
Days before passwords expire 90
Days before a user is notified about 14
expiration
You confirm that User1 is synced to Azure AD.
For each of the following statements, select Yes if the statement is true. Otherwise, select No.
NOTE: Each correct selection is worth one point.
You have a Microsoft 365 E5 subscription that contains a user named User1.
User1 exceeds the default daily limit of allowed email messages and is on the Restricted entities list.
You need to remove User1 from the Restricted entities list.
What should you use?
You have a Microsoft 365 E5 subscription. The subscription contains a Microsoft SharePoint Online site named Site1. Site1 contains the following files:
• File.docx
• ImportantFile.docx
• Filejmportant.docx
From Microsoft Defender Cloud Apps, you create a file policy named Policy1 that has the filter shown in the following exhibit.
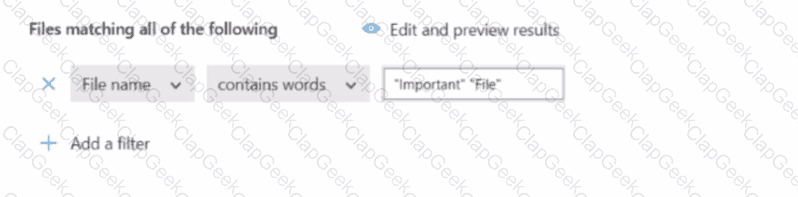
To which files will Policy1 apply?
Note: This question is part of a series of questions that present the same scenario. Each question in the series contains a unique solution that might meet the stated goals. Some question sets might have more than one correct solution, while others might not have a correct solution.
After you answer a question in this section, you will NOT be able to return to it. As a result, these questions will not appear in the review screen.
You have a computer that runs Windows 10.
You need to verify which version of Windows 10 is installed.
Solution: From the Settings app, you select Update & Security to view the update history.
Does this meet the goal?
You need to ensure that the support technicians can meet the technical requirement for the Montreal office mobile devices.
What is the minimum of dedicated support technicians required?
Note: This question is part of a series of questions that present the same scenario. Each question in the series contains a unique solution that might meet the stated goals. Some question sets might have more than one correct solution, while others might not have a correct solution.
After you answer a question in this section, you will NOT be able to return to it. As a result, these questions will not appear in the review screen.
Your network contains an Active Directory domain named contoso.com that is synced to Microsoft Azure Active Directory (Azure AD).
You manage Windows 10 devices by using Microsoft System Center Configuration Manager (Current Branch).
You configure a pilot for co-management.
You add a new device named Device1 to the domain. You install the Configuration Manager client on Device1.
You need to ensure that you can manage Device1 by using Microsoft Intune and Configuration Manager.
Solution: Define a Configuration Manager device collection as the pilot collection. Add Device1 to the collection.
Does this meet the goal?
You need to create the Microsoft Store for Business. Which user can create the store?
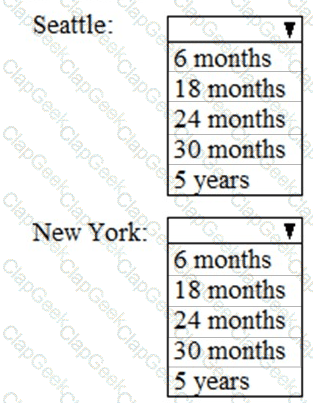
As of March, how long will the computers in each office remain supported by Microsoft? To answer, select the appropriate options in the answer area.
NOTE: Each correct selection is worth one point.
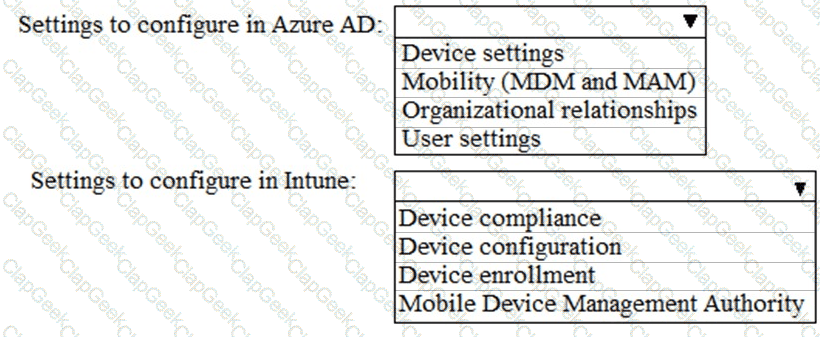
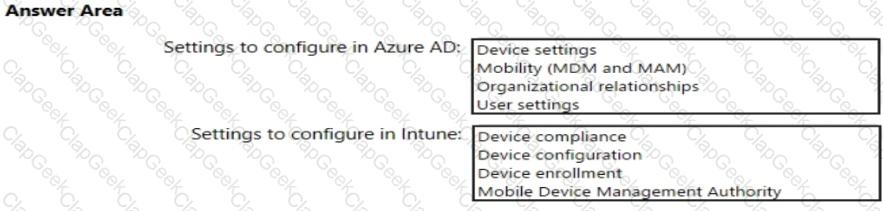
You need to meet the Intune requirements for the Windows 10 devices.
What should you do? To answer, select the appropriate options in the answer area.
NOTE: Each correct selection is worth one point.
Note: This question is part of a series of questions that present the same scenario. Each question in the series contains a unique solution that might meet the stated goals. Some question sets might have more than one correct solution, while others might not have a correct solution.
After you answer a question in this section, you will NOT be able to return to it. As a result, these questions will not appear in the review screen.
Your network contains an Active Directory domain named contoso.com that is synced to Microsoft Azure Active Directory (Azure AD).
You manage Windows 10 devices by using Microsoft System Center Configuration Manager (Current Branch).
You configure a pilot for co-management.
You add a new device named Device1 to the domain. You install the Configuration Manager client on Device1.
You need to ensure that you can manage Device1 by using Microsoft Intune and Configuration Manager.
Solution: You create a device configuration profile from the Device Management admin center.
Does this meet the goal?
You need to meet the compliance requirements for the Windows 10 devices.
What should you create from the Intune admin center?
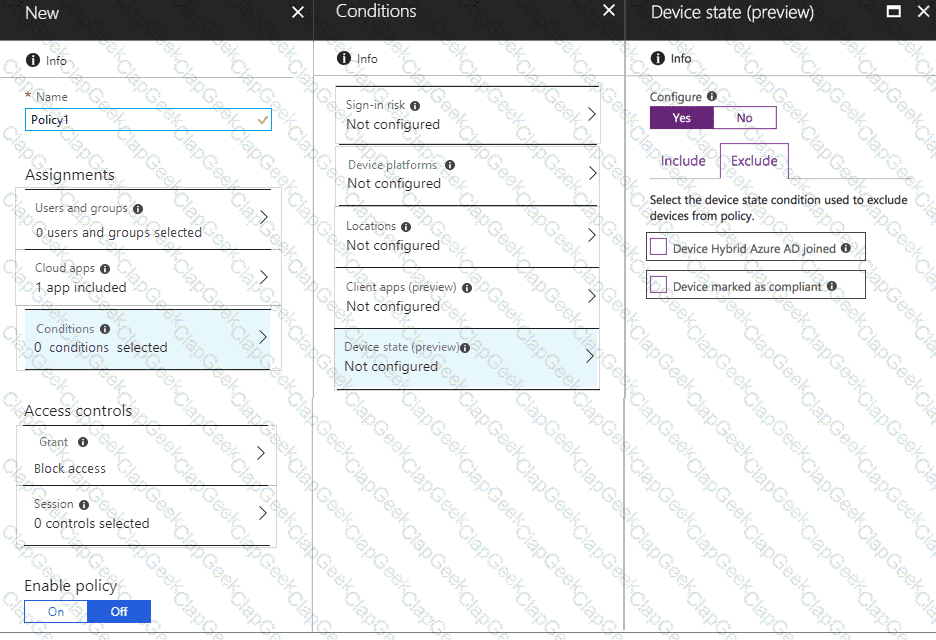
You need to configure a conditional access policy to meet the compliance requirements.
You add Exchange Online as a cloud app.
Which two additional settings should you configure in Policy1? To answer, select the appropriate options in the answer area.
NOTE: Each correct selection is worth one point.
You need to ensure that User1 can enroll the devices to meet the technical requirements. What should you do?
You need to meet the technical requirements and planned changes for Intune.
What should you do? To answer, select the appropriate options in the answer area.
NOTE: Each correct selection is worth one point.
You need to configure Office on the web to meet the technical requirements.
What should you do?
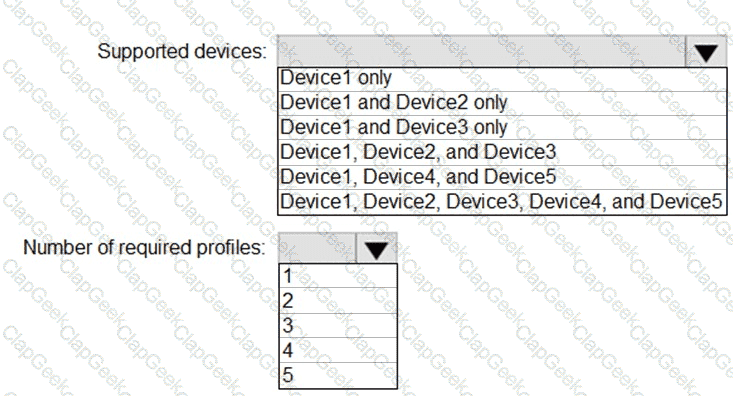
You plan to implement the endpoint protection device configuration profiles to support the planned changes.
You need to identify which devices will be supported, and how many profiles you should implement.
What should you identify? To answer, select the appropriate options in the answer area.
NOTE: Each correct selection is worth one point.
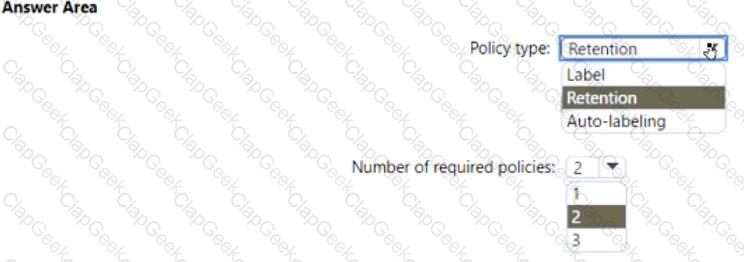
You need to configure the information governance settings to meet the technical requirements.
Which type of policy should you configure, and how many policies should you configure? To answer, select the appropriate options in the answer area.
NOTE: Each correct selection is worth one point.
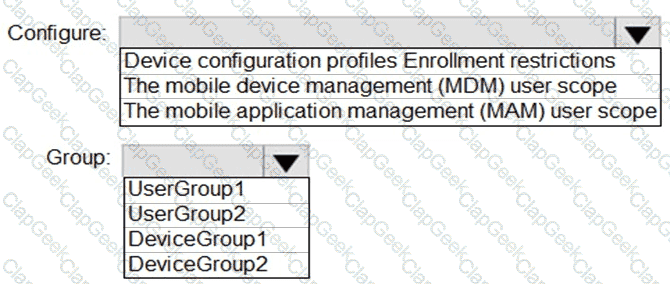
You need to configure automatic enrollment in Intune. The solution must meet the technical requirements.
What should you configure, and to which group should you assign the configurations? To answer, select the appropriate options in the answer area.
NOTE: Each correct selection is worth one point.
You need to create the DLP policy to meet the technical requirements.
What should you configure first?
You need to create the Safe Attachments policy to meet the technical requirements.
Which option should you select?
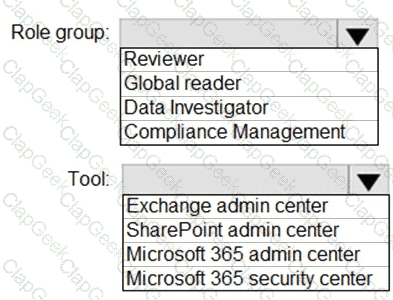
You need to ensure that User2 can review the audit logs. The solutions must meet the technical requirements.
To which role group should you add User2, and what should you use? To answer, select the appropriate options in the answer area.
NOTE: Each correct selection is worth one point.
You create the planned DLP policies.
You need to configure notifications to meet the technical requirements.
What should you do?
HOTSPOT
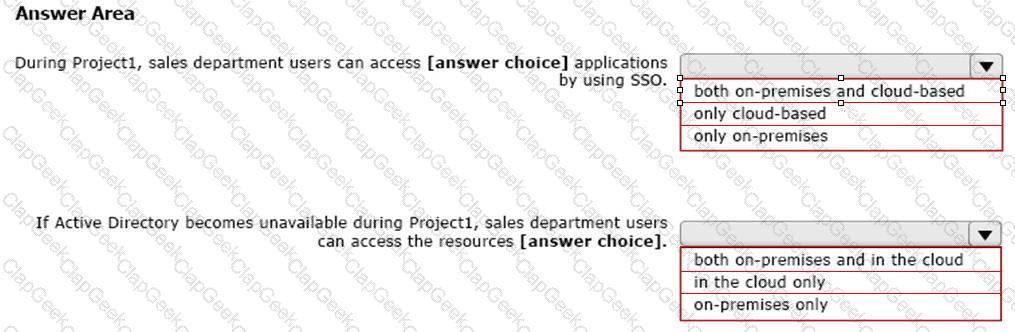
You create the Microsoft 365 tenant.
You implement Azure AD Connect as shown in the following exhibit.
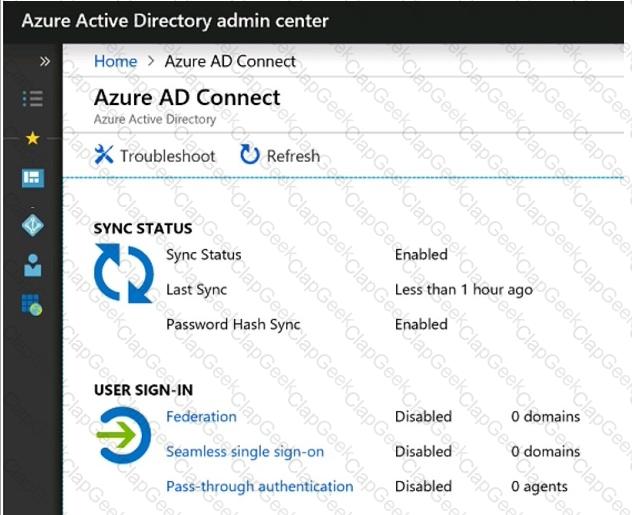
Use the drop-down menus to select the answer choice that completes each statement based on the information presented in the graphic.
NOTE: Each correct selection is worth one point.
Which role should you assign to User1?
Available Choices (select all choices that are correct)
You are evaluating the required processes for Project1.
You need to recommend which DNS record must be created while adding a domain name for the project.
Which DNS record should you recommend?
You need to ensure that all the sales department users can authenticate successfully during Project1 and Project2.
Which authentication strategy should you implement for the pilot projects?
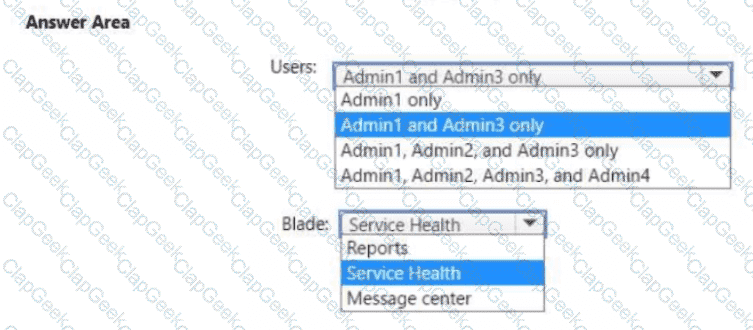
You need to ensure that the Microsoft 365 incidents and advisories are reviewed monthly.
Which users can review the incidents and advisories, and which blade should the users use? To answer, select the appropriate options in the answer area.
NOTE: Each correct selection is worth one point.
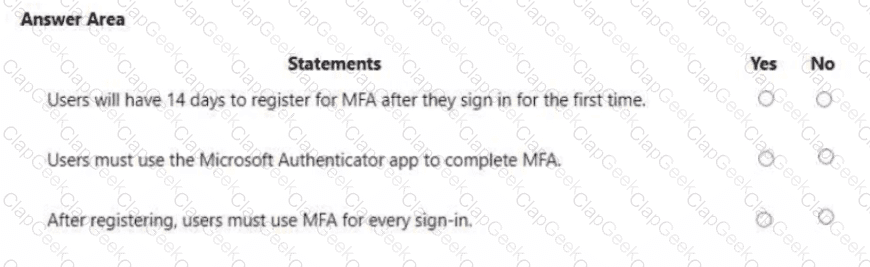
You are evaluating the use of multi-factor authentication (MFA).
For each of the following statements, select Yes if the statement is true. Otherwise, select No.
NOTE: Each correct selection is worth one point.
You need to configure Azure AD Connect to support the planned changes for the Montreal Users and Seattle Users OUs.
What should you do?
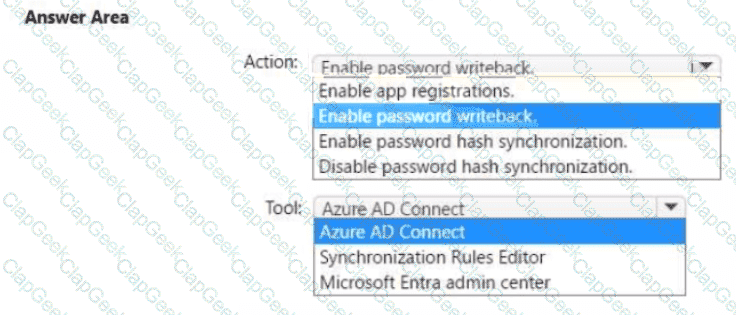
You need to ensure that Admin4 can use SSPR.
Which tool should you use. and which action should you perform? To answer, select the appropriate options m the answer area.
NOTE: Each correct selection is worth one point.
You need to configure just in time access to meet the technical requirements.
What should you use?
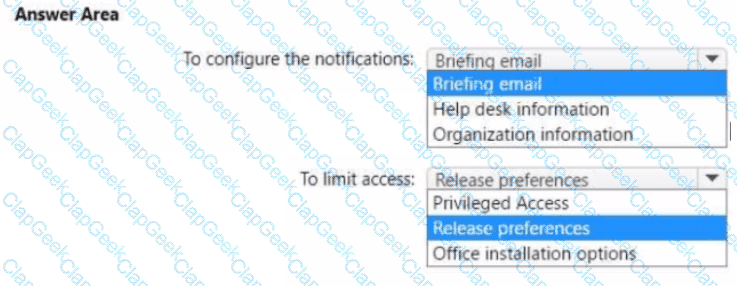
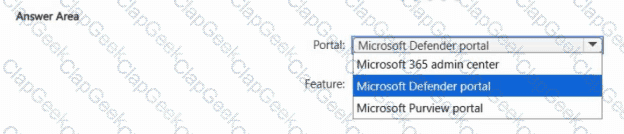
You need to configure the Office 365 service status notifications and limit access to the service and feature updates. The solution must meet the technical requirements.
What should you configure in the Microsoft 365 admin center? To answer, select the appropriate options in the answer area.
NOTE: Each correct selection is worth one point.