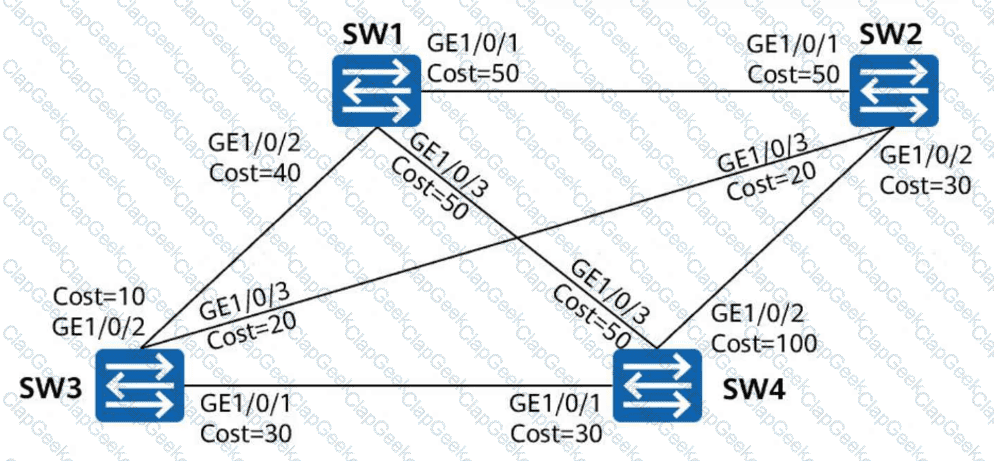
In the STP topology shown in the figure, all links have the same path cost, and SW1 is the root bridge. Which of the following ports will become designated ports? (Select all that apply)
The following command output is displayed on R1:
[R1] display aaa configuration
Domain Name Delimiter : @
Domainname parse direction : Left to right
Domainname location : After-delimiter
Administrator user default domain : default_admin
Normal user default domain : default
Domain : total: 256 used: 3
Authentication-scheme : total: 32 used: 2
Accounting-scheme : total: 32 used: 1
Authorization-scheme : total: 32 used: 2
Service-scheme : total: 256 used: 0
Recording-scheme : total: 32 used: 0
Local-user : total: 512 used: 2
Remote-admin-user block retry-interval : 5 Min(s)
Remote-admin-user block retry-time : 3
Remote-admin-user block time : 5 Min(s)
Session timeout invalid enable : No
Which of the following statements is false?
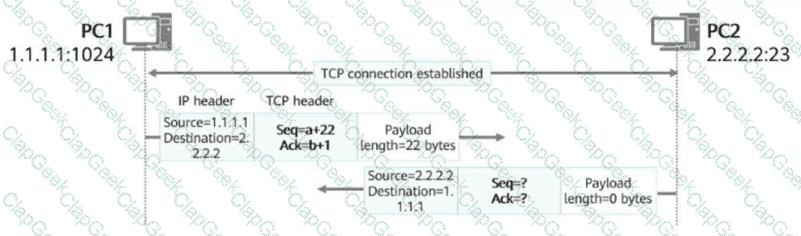
In the figure, a TCP connection has been established between PC1 and PC2. After PC1 sends a data segment to PC2, which of the following is the acknowledgment number in the packet returned by PC2?
On a switched network where STP is enabled on all devices, when a downstream device detects a topology change, it continuously sends configuration BPDUs to the upstream device until the root bridge is informed of the topology change.
According to the following routing table, it can be inferred that the IP address of VLANIF 2 on R1 is 10.0.12.1/24.
[R1] display ip routing-table
Proto: Protocol Pre: Preference
Route Flags: R - relay, D - download to fib, T - to vpn-instance, B - black hole route
Routing Table : public
Destinations : 10 Routes : 10
Destination/Mask Proto Pre Cost Flags NextHop Interface
10.0.12.0/24 Direct 0 0 D 10.0.12.1 Vlanif2
10.0.12.1/32 Direct 0 0 D 127.0.0.1 Vlanif2
10.0.12.255/32 Direct 0 0 D 127.0.0.1 Vlanif2
10.0.21.0/24 Direct 0 0 D 10.0.21.1 Vlanif3
10.0.21.1/32 Direct 0 0 D 127.0.0.1 Vlanif3
10.0.21.255/32 Direct 0 0 D 127.0.0.1 Vlanif3
During VLAN planning for a campus network, VLAN IDs for different service types must be allocated consecutively, without redundancy, to prevent omissions in future allocations.
DAD enables a node to detect whether an IPv6 address is already in use by another node before assigning it to an interface. This ensures that duplicate unicast addresses do not exist on a network. Which of the following packets are used for DAD? (Select all that apply)
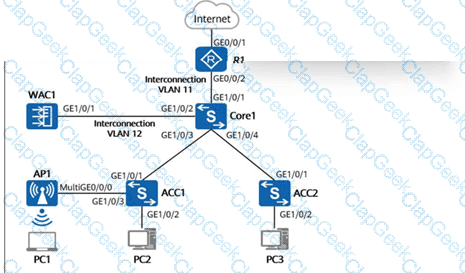
On the campus network shown in the figure below, the core switch Core1 functions as a Layer 3 gateway and as a DHCP server to dynamically assign IP addresses to AP1, PC1, PC2, and PC3. The network below Core1 is a Layer 2 network. WAC1 and R1 are connected to Core1 at Layer 3. AP1 goes online through VLAN 100. The wireless service VLAN is VLAN 101, and the wired service VLANs for PC2 and PC3 are VLAN 102 and VLAN 103, respectively. Additionally, the direct forwarding mode is used for wireless traffic forwarding. If no additional VLANs are allowed on device interfaces, which of the following VLANs must be allowed on GE1/0/1 of ACC1? (Select all that apply)
Which of the following IP addresses cannot be configured for a host by default?
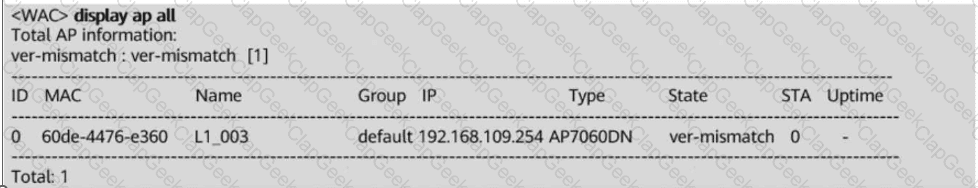
In the WAC + Fit AP networking, an AP fails to go online. The output of the display ap all command run on the WAC is shown below. According to the command output, which of the following is the possible cause of the AP’s failure to go online?
Which of the following commands can be used to check OSPF routes in the global routing table?
The emergence of AI poses new requirements on data center networks. To meet AI computing requirements, a high-speed intelligent computing data center network with zero packet loss needs to be constructed. Which of the following statements are false about the requirements and solutions of intelligent computing data center networks? (Select all that apply)
The domain to which a user belongs is determined by the user name used by the user to log in to the NAS device. If the domain name carried in the user name is not configured on the NAS device, the authentication fails.
With the development of data centers, a large number of services are deployed on virtual machines (VMs). The original VLAN isolation solution cannot achieve isolation between so many VMs. VXLAN uses VXLAN Network Identifiers (VNIs) to provide a larger range than VLAN IDs, so that a larger number of VMs can be isolated.
Which of the following phases are required for establishing a connection between an SSH server and an SSH client? (Select all that apply)