An employee of a pharmaceutical company accidentally checked in code that contains AWS secret keys to a public GitHub repository, which exposes production resources to attackers. Which mitigation strategy must a security engineer recommend to prevent future reoccurrence?
A financial company uses a remote access solution that directs all traffic over a secure tunnel. The company recently received some large ISP bills from the headquarter location. According to traffic analysis during the investigation, most of the network traffic was due to employees spending a lot of time on video conferences provided by a SaaS collaboration company. What must the company modify to reduce the cost without negatively impacting security or employee experience?
After a recent security breach, a financial company is reassessing their overall security posture and strategy to better protect sensitive data and resources. The company already deployed on-premises next-generation firewalls at the network edge for each branch location. Security measures must be enhanced at the endpoint level. The goal is to implement a solution that provides additional traffic filtering directly on endpoint devices, thereby offering another layer of defense against potential threats. Which technology must be implemented to meet the requirement?
Refer to the exhibit.
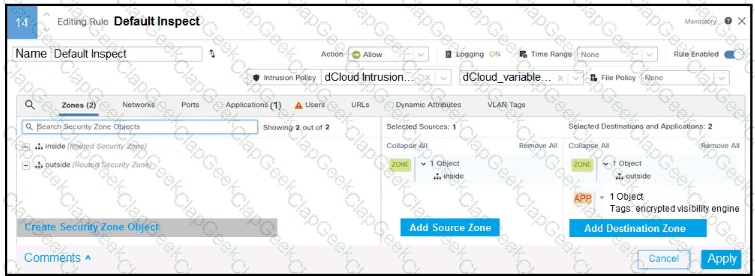
In addition to SSL decryption, which firewall feature allows malware to be blocked?
A developer company recently implemented a testing environment based on Linux operating system. The company needs a technology solution that produces tracing and filtering capabilities in the Linux kernel. Which technology meets these requirements without modifying the kernel source code?
A legal services company wants to prevent remote employees from accessing personal email and social media accounts while using corporate laptops. Which security solution enforces the policy?
Which financial reporting regulatory framework must a publicly traded company doing business in the US comply with?
A company published software that had a security vulnerability, and an attacker used the vulnerability to steal critical information from the environment. The issue was reported by the security team, and the administrator was instructed to run shift-left security tests before publishing the software. Which component of the software development pipeline must be recommended to run the tests?
Employees in a healthcare organization could not access their devices when they returned to work after the weekend. The security team discovered that a threat actor had encrypted the devices. Which security solution would mitigate the risk in future?
Considering recent cybersecurity threats, a company wants to improve the process for identifying, assessing, and managing risks with a comprehensive and holistic approach. Which framework must be used to meet these requirements?


